KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Oxfam Australia has confirmed a data breach after suffering a cyberattack and their donor databases put up for sale on a hacker forum in January.
Oxfam Australia is a charity focused on alleviating poverty in Africa, Asia, and the middle east. The charity is part of a confederation of twenty individual charities operating under the Oxfam name.
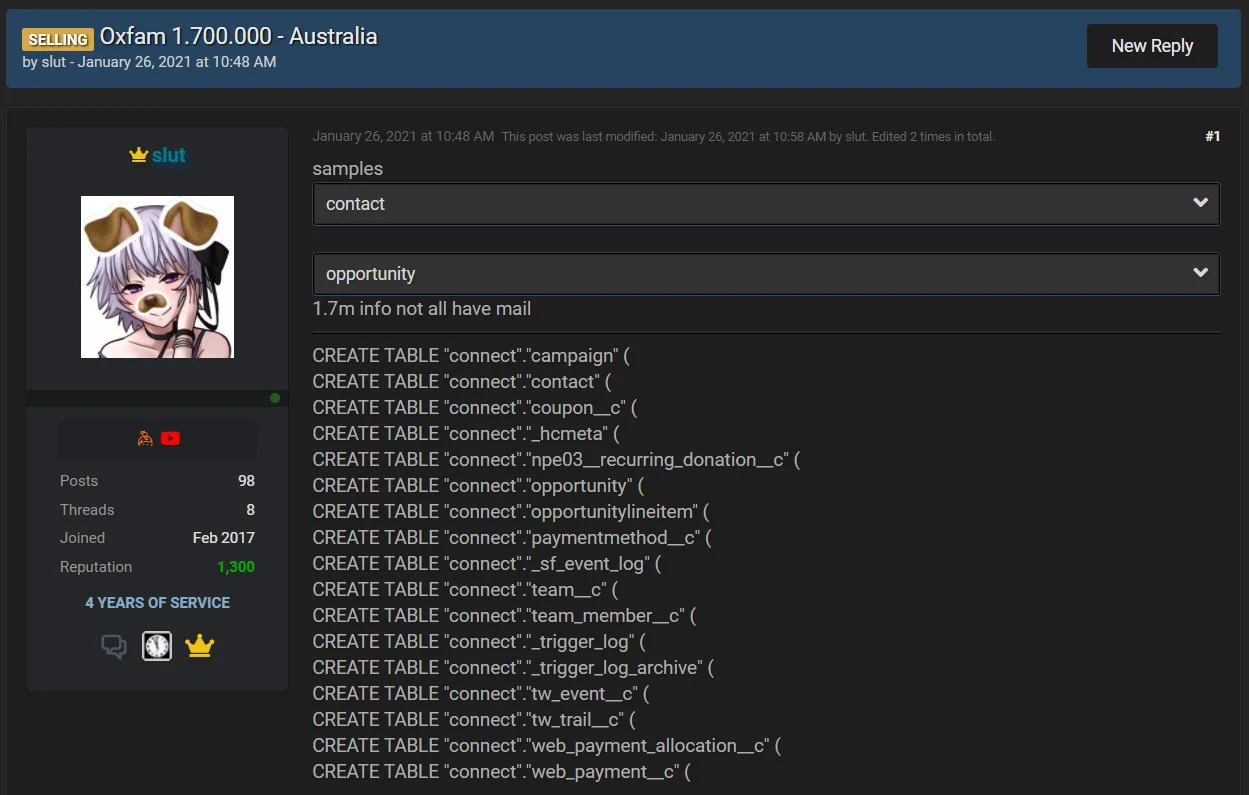
Last month, BleepingComputer was the first to report that a threat actor was selling a stolen Oxfam Australia database containing 1.7 million user records. These records included names, email addresses, addresses, phone numbers, and donation amounts.
From the database samples shared by the threat actor, BleepingComputer was able to confirm that at least one of the records contained accurate information.
After contacting Oxfam Australia about the sale, the charity told BleepingComputer that they had begun an investigation into the attack.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
Today, Oxfam Australia has confirmed that they suffered a data breach that has exposed donor information.
“Following an independent IT forensic investigation, Oxfam Australia announced today that it has found supporters’ information on one of its databases was unlawfully accessed by an external party on 20 January 2021.”
“The database includes information about supporters who may have signed a petition, taken part in a campaign or made donations or purchases through our former shops.”
“While the investigation found that no passwords were compromised, the database unlawfully accessed by the external party for the majority of supporters included names, addresses, dates of birth, emails, phone numbers, gender and in some cases, donation history. For a limited group of supporters, the database contained additional information, and Oxfam is contacting these supporters directly to inform them of the specific types of information relevant to them,” Oxfam Australia disclosed today.
Oxfam Australia states that a small subset of donors the threat actor may have had access to bank names, account numbers, and partial credit card numbers.
It is not known if any threat actors purchased the stolen data after it was marketed on hacker forums.
When we first reported on the breach, we advised Oxfam Australia donors to change their password on the site and other sites that utilize the same password.
While Oxfam Australia states that no passwords have been changed, we still advise that you secure your accounts to be safe due to the amount of data stolen by the threat actor.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
As threat actors commonly use stolen data to harvest further sensitive information, Oxfam Australia donors should be on the lookout for targeted phishing emails, SMS texts, and phone calls pretending to be from Oxfam.