KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Demand for better return from IT governance framework PDF investments and concern over the generally increasing amount of IT governance framework PDF expenditures. The need to meet regulatory requirements for IT governance framework PDF controls in financial reporting and healthcare areas. The selection of service providers and the management of service outsourcing and acquisition.
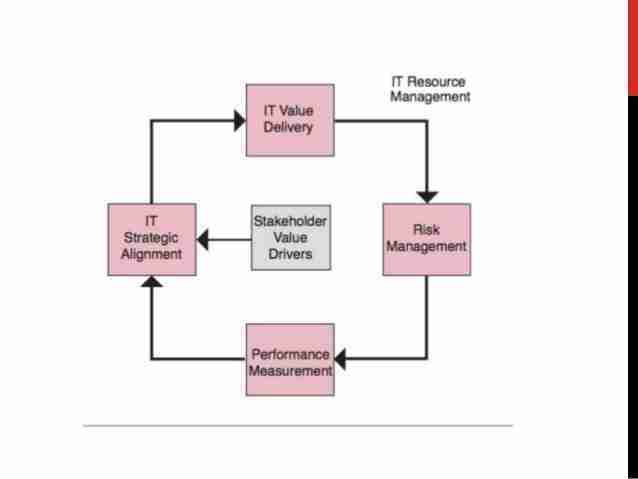
IT governance framework PDF is a continuous life cycle that can be entered at any point. Usually, one starts with the strategy and its alignment throughout the enterprise. Afterward, implementation occurs, delivering the value the strategy promised and addressing the risks that need mitigation. It recommended that strategy be monitored continuously, and the results must be: a. measured, b. reported, and c. acted upon.
Strategy must be re-evaluated and realigned annually, if needed. This life cycle operates in an environment that is influenced by:
Control Objectives for Information and Related Technology (COBIT) was designed as an IT governance framework PDF model, and it tells you what you should be doing. It is a framework created by ISACA for (IT) and IT governance framework PDF. It is also a supporting toolset that allows managers to bridge the gap between control requirements, technical issues, and business risks.
For COBIT to govern IT effectively, it is important to appreciate the activities and risks within IT that need to be managed. These can be summarized as follows:
Also read: How to Write an Effective Privacy Statement for Websites
Outcome measures, key goal indicators (KGIs) What is measured here: Is the information needed available all the time to support the business needs? Are integrity and confidentiality risks Absent? Is the information & resources reliable?
Performance Indicators, Performance indicators, or key performance indicators (KPIs), indicate whether goals are likely to be met. This can be through the Sales Target Measure, taking the number of wins over a specific time period and compare it to a future target and past performance to motivate your sales team.
Information Technology Infrastructure Library (ITIL) is a set of guidance developed by the United kingdom’s office of Government Commerce (OGC). ITIL does not doc how to do things but tells you what you could and should be doing. It shares with us what other people found to be the best way to approach IT as a service provider.

1. Service Strategy volume: Provide guidance in developing a strategy for IT service management. This involves understanding your market, your customers, your capabilities & resources & financial constraints under which services must be delivered and supported.
Processes Within Service Strategy Are:
1. Service Strategy
2. Service Design volume: Service Design begins with a set of business requirements and ends with a solution designed to meet these business needs.
3. Service Transition: Looks at managing change, risk and quality assurance during the deployment of service into operation.
4. Service Operation volume: It is concerned with daily activities, and it provides guidance on the effective & efficient operation of the service. It’s where the value of the service is realized & strategy of the organization is executed.
5. Continual Service Improvement volume (CSI): Provide guidance to improve the overall process and how its executed. This should be integrated into all the other life cycle stages. This is a continual activity Based on this report, org strive for improvements.
ITIL was designed as a service management framework to help you understand how you support processes, and how you deliver services .
COBIT was designed as an IT governance framework PDF model, particularly and initially with audit in mind to give you control objectives and control practices on how that process should behave
The difference between the two is, COBIT tells you what you should be doing, while ITIL tells you how you should be doing it. Put them together, and you have a very powerful model of what you need to be doing and how to do it.
None of these frameworks are in competition with each other, in fact, it is best if they are used together.
COBIT can be used to determine if the company’s needs (including security) are being properly supported by IT. ISO 17799 can be used to determine and improve upon the company’s security posture. And ITIL can be used to improve IT processes & services to meet the company’s goals (including security).
Start investigating possible tools for strategic planning and aligning IT with the organization’s strategic plan for toolkit. If you don’t know where to start, do a web search on SWOT analysis (strengths, weaknesses, opportunities and threats), metrics, analytics and the balanced scorecard. Describe what you find and share as appropriate on the D2L discussion topic for IT Toolkits.
While ITIL was designed as a service management framework to help you understand how you support processes and how you deliver services, and COBIT was designed as an IT governance framework PDF model, Val IT, on the other hand, talks about the strategy for your services (how well it is aligned), and its value. It talks about how to do the right things for the organisation (including security) in the right way and in doing them well.
Also read: Top 10 Reliable IT Companies in Singapore