KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





New malware dubbed Cyclops Blink has been linked to the Russian-backed Sandworm hacking group in a joint security advisory published today by US and UK cybersecurity and law enforcement agencies.
The malware, used by Sandworm operators to create a botnet since at least June 2019, targets WatchGuard Firebox and other Small Office/Home Office (SOHO) network devices.
“The malware dubbed Cyclops Blink appears to be a replacement for the VPNFilter malware exposed in 2018, and its deployment could allow Sandworm to remotely access networks,” the UK National Cyber Security Centre said today.
“In common with VPNFilter, Cyclops Blink deployment also appears indiscriminate and widespread,” the joint advisory adds.
Also Read: Document Shredding Services for Commercial Document Destruction
“The actor has so far primarily deployed Cyclops Blink to WatchGuard devices, but it is likely that Sandworm would be capable of compiling the malware for other architectures and firmware.”
WatchGuard issued its own advisory today, saying that Cyclops Blink may have affected roughly 1% of all active WatchGuard firewall appliances, which are devices mainly used by business customers.
According to NCSC, FBI, CISA, and NSA analysis, the malware also comes with modules specifically developed to upload/download files to and from its command-and-control server, collect and exfiltrate device information, and update the malware.
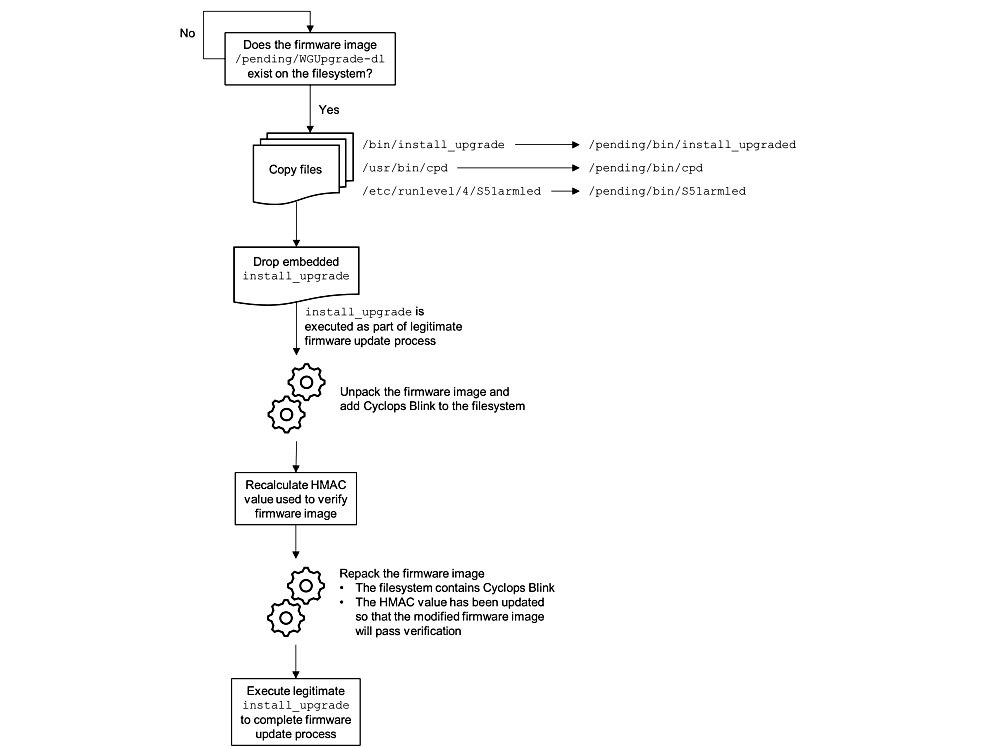
The malware uses the infected devices’ legitimate firmware update channels to maintain access to compromised systems by injecting malicious code and deploying repacked firmware images.
“Cyclops Blink persists on reboot and throughout the legitimate firmware update process. Affected organizations should therefore take steps to remove the malware,” the agencies added.
“WatchGuard has worked closely with the FBI, CISA and the NCSC, and has provided tooling and guidance to enable detection and removal of Cyclops Blink on WatchGuard devices through a non-standard upgrade process.”
Also Read: 4 Steps to Data Protection Certification For Your Business
All accounts on infected devices should be assumed as being compromised and organizations should immediately remove Internet access to the management interface of affected network devices.
Sandworm (also tracked as Voodoo Bear, BlackEnergy, and TeleBots) is an elite Russian-sponsored cyberespionage group active since the mid-2000s.
Its members are believed to be military hackers part of Unit 74455 of the Russian GRU’s Main Center for Special Technologies (GTsST).
This hacking group has been linked to the BlackEnergy malware behind the Ukrainian blackouts of 2015 and 2016 [1, 2, 3], as well as the KillDisk wiper attacks that targeted Ukrainian banks.
Sandworm is also behind the NotPetya ransomware that inflicted an estimated billions worth of damage to companies worldwide starting with June 2017.
In October 2020, the US Department of Justice charged six Sandworm operatives for hacking activities related to the PyeongChang 2018 Winter Olympics, the 2017 French elections, and the NotPetya ransomware attack.
The group was also linked by ANSSI, the French national cyber-security agency, to the Centreon supply-chain attack against French companies’ networks and breaches of multiple French IT providers in February 2021.
Additional information on Sandworm’s Cyclops Blink malware, including indicators of compromise, and Yara rules and signatures, are available at the end of NCSC’s malware analysis report [PDF].
Update February 23, 11:20 EST: Added info on guidance provided by WatchGuard.
Update February 23, 14:15 EST: Linked to WatchGuard advisory.