KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Accenture, a global IT consultancy giant has allegedly been hit by a ransomware cyberattack from the LockBit ransomware gang.
Accenture is an IT giant known to serve a wide range of industries including automobiles, banks, government, technology, energy, telecoms, and many more.
Valued at $44.3 billion, Accenture is one of the world’s largest tech consultancy firms employing around 569,000 employees across 50 countries.
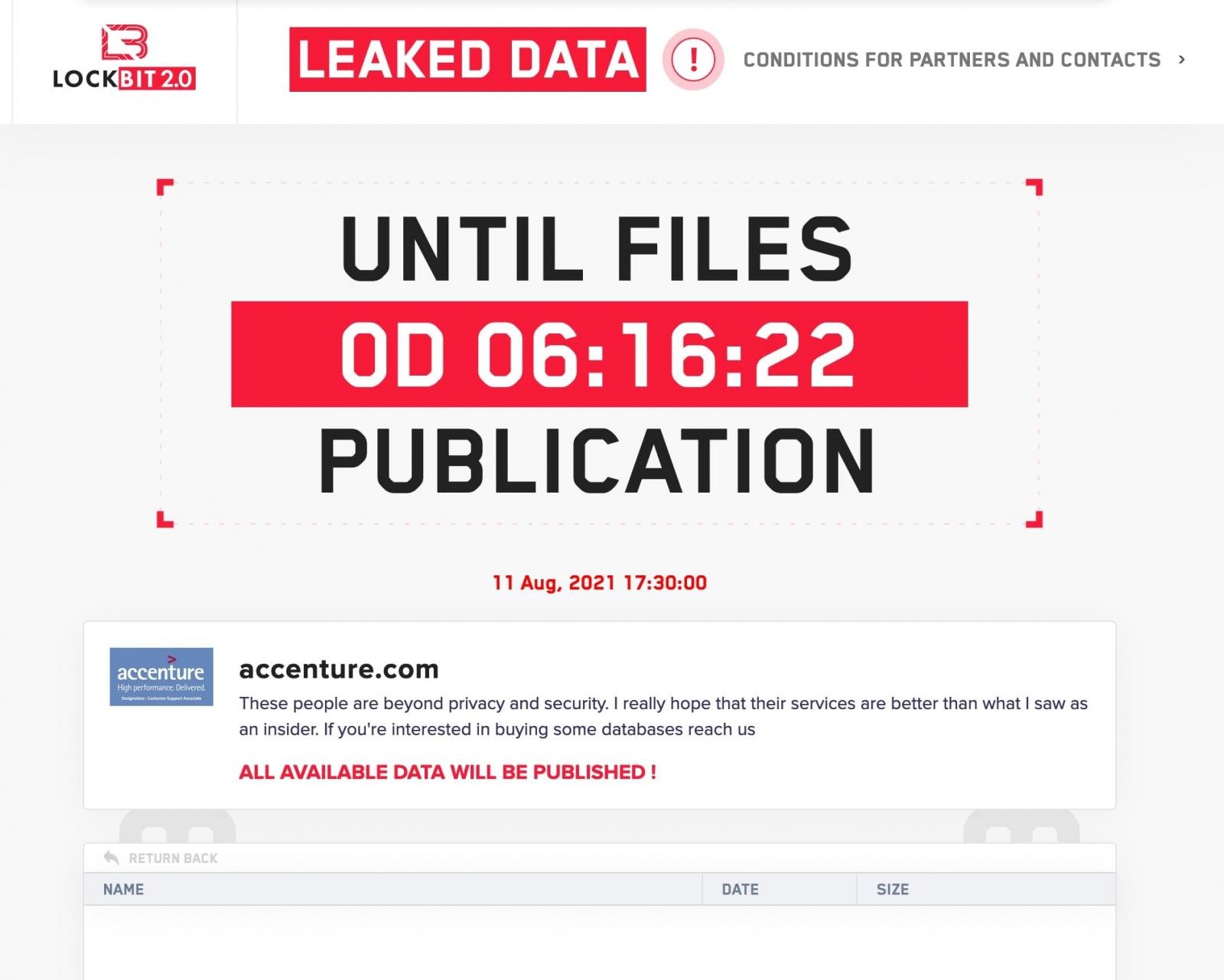
A ransomware group known as LockBit 2.0 is threatening to publish files data allegedly stolen from Accenture during a recent cyberattack.
Also Read: What is Social Engineering and How Does it Work?
The threat actors state that they will publish the data later today if a ransom is not paid, as seen by BleepingComputer:
While LockBit has not shown proof of the stolen data, they claim to be willing to sell it to any interested parties.
“These people are beyond privacy and security. I really hope that their services are better than what I saw as an insider. If you’re interested in buying some databases reach us,” states LockBit on their data leak site.
The exact details as to when the breach occurred, when was it detected, its scope or, the technical cause of exploitation are yet to be known.
Accenture told BleepingComputer that affected systems had been recovered from a backup:
“Through our security controls and protocols, we identified irregular activity in one of our environments. We immediately contained the matter and isolated the affected servers.”
“We fully restored our affected systems from back-up. There was no impact on Accenture’s operations, or on our clients’ systems,” Accenture told BleepingComputer.
In conversations seen by the Cyble research team, the LockBit ransomware gang claims to have stolen six terabytes of data from Accenture and are demanding a $50 million ransom.
The threat actors claim to have gotten access to Accenture’s network via a corporate “insider.”
Sources familiar with the attack have told BleepingComputer that Accenture had confirmed the ransomware attack to at least one CTI vendor, and the IT services provider is also in the process of notifying more customers.
Additionally, cybercrime intelligence firm Hudson Rock shared that Accenture had 2,500 compromised computers belonging to employees and partners:
LockBit has previously hit many victims, including UK’s Merseyrail train network.
Also Read: 4 Reasons Why You Need an Actively Scanning Antivirus Software
Earlier this week, the Australian government had warned of escalating LockBit 2.0 ransomware attacks, after the group was seen actively recruiting insiders at companies they plan on breaching, in exchange for millions of dollars in rewards.
Edit 12:40 PM ET: BleepingComputer had reached out to Accenture well in advance of publishing but received a quote after press time which has been added with proper attribution.