KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Nowadays, security is all about knowing who and what to trust. In a world of constant exchange of information and correspondence, it can be quite tricky to pinpoint what is genuine and what is not. Would you even trust a new website and key in your personal information as you sign up? Or how would you know that you are chatting with your real friend at the end of the line? These instances could be real hard to come by, especially if you have no idea on the tactics employed by cybercriminals.
In this article, we would answer two questions that can would raise your awareness and decrease your chance of falling for this feat; 1) what is social engineering, and 2) how does it work?
Social engineering is a mode of manipulation employed by an individual to deceitfully gain access to another’s valuables, including tangible and nontangible stuff. In the context of cybersecurity, social engineering can be defined an attack vector that relies on human interaction and often involves manipulating an individual into breaking cybersecurity procedures to gain unauthorized access to systems, networks, or private personal data.
These cybercriminals may target an individual into giving them their passwords or bank information, or simply their login credentials. From there, the perpetrator can further steal other information, or valuable asset, or even target other individuals by accessing the victim’s contacts.
What makes social engineering rampant is how it exploit’s the human nature to instinctively trust something or someone that appears genuine upfront. For those who are particularly not adamant and wary, this can be a real problem.
Social engineering can be perpetuated in a variety of ways, which we will take about later. But if you do not know what is social engineering, you might be an easy target to this ever-present cybersecurity threat.
Also Read: 4 Reasons Why You Need an Actively Scanning Antivirus Software
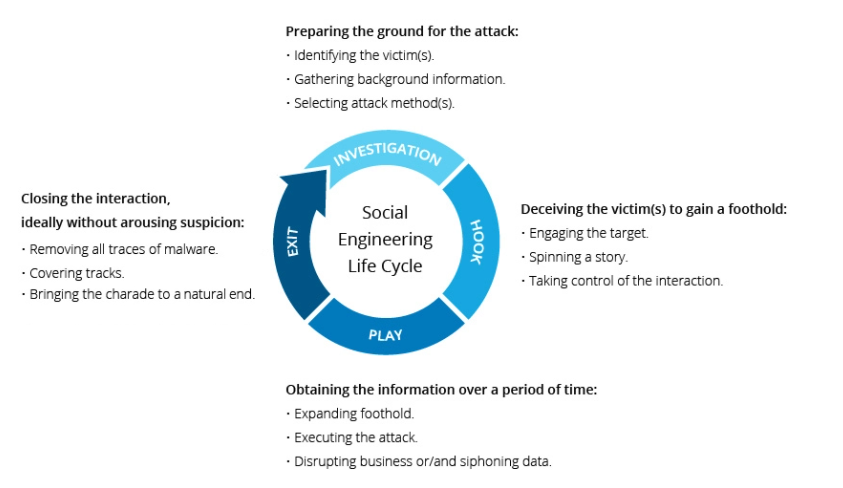
Although varying types of social engineering can happen in one or more steps, the most common ones generally follow a certain pattern. First, you must remember that this scheme is fairly grounded on psychological manipulation to tricking victims to commit security mistakes or give away their private personal information. Logically, the first step of the perpetrator is to investigate is target victim.
After gaining sufficient intel on the target’s background information, including potential points of entry and vulnerabilities in security protocol, the cybercriminal may now proceed with the attack. The strategy is to gain the victim’s trust and confidence by providing stimuli for the next actions to break security protocols. Below is a perfect example of how social engineering works and how it is propagated through a cycle:
A lot of criminals would often use people’s innate willingness to be helpful or fear of punishment. For example, the perpetrator might pretend to be your one of your close friends that would request you to send her your private information in order to help her post-haste. Another is when the attacker pretends to be your boss, commanding you to disclose via email, SMS, or chat a confidential information immediately. This creates a certain degree of panic or sense of urgency which further pushes the victim to make snappy and erroneous decisions.

If you know what social engineering is, then you are one step closer in preventing it. The most important thing is to take control of your emotions when facing suspicious and too-good-to-be-true offers, requests, or any other messages. Be wary when you feel alarmed by an unsolicited email or highly engaging website displays.
You can also take note of the following precautions:
In the cybersecurity landscape, your personal information is your most valuable asset. Protecting it from malicious schemes such as social engineering should always be your top priority. While there are certainly some advanced steps you can take into consideration to prevent it, the most effective one is being a master of your own psyche.
Also Read: 5 Types of Ransomware, Distinguished
Protecting personal data that the organisation manages is the primary duty that must be upheld, or else risk the financial penalty imposed by the PDPC in case of a breach. Employees are the weakest in the organisation’s cybersecurity. Oftentimes, they are targeted using social engineering tactics to trick them into giving access to the organisation’s system.
To help organisations with their data protection compliance and to avoid being a victim of this clever tactic, they can outsource a DPO, which is an officer responsible for ensuring that all data protection provisions are complied with at all times. It is the officer that is responsible for the employee’s guidelines and policies to follow whenever they encounter a malicious email asking for their credentials.