KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The MyKings botnet (aka Smominru or DarkCloud) is still actively spreading, making massive amounts of money in crypto, five years after it first appeared in the wild.
Being one of the most analyzed botnets in recent history, MyKings is particularly interesting to researchers thanks to its vast infrastructure and versatile features, including bootkits, miners, droppers, clipboard stealers, and more.
The latest team of researchers to look into MyKings is Avast Threat Labs, which gathered 6,700 unique samples to analyze since the beginning of 2020.
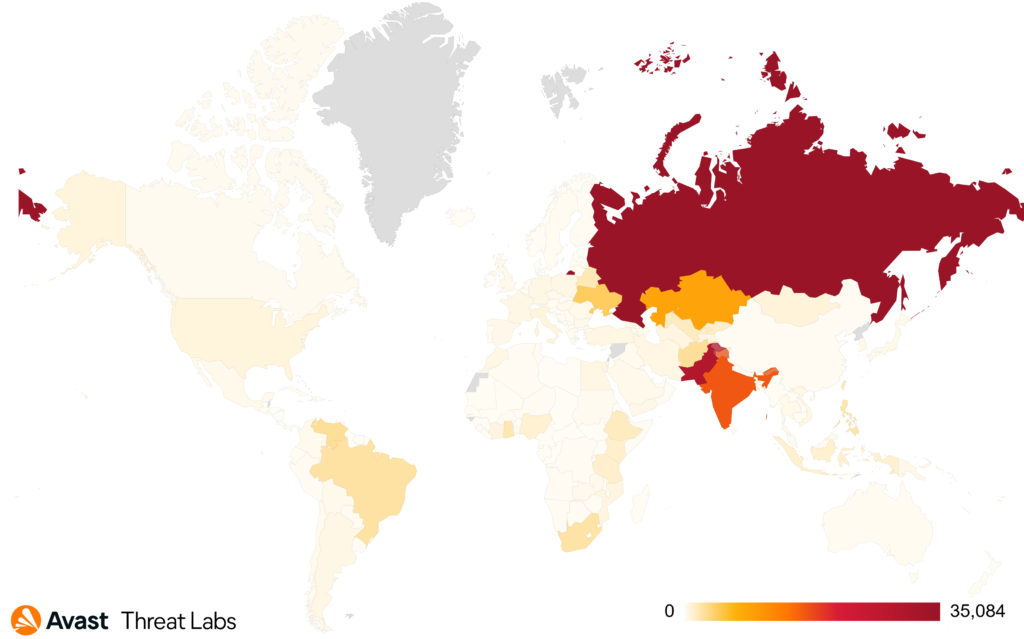
During the same period, Avast actively prevented over 144,000 attacks MyKings against its clients, most of them based in Russia, India, and Pakistan.
Also Read: Intrusion Into Privacy All About Law And Legal Definition
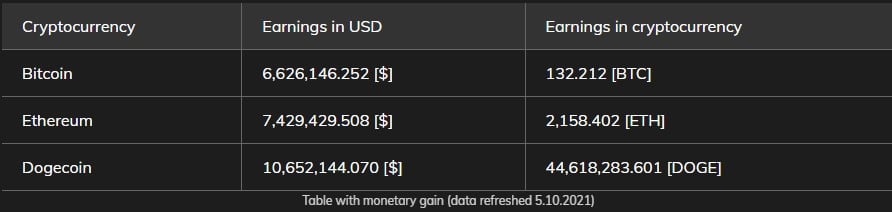
The botnet uses many cryptocurrency wallet addresses, with the balances in some of them being quite high. Avast believes that these wallets’ cryptocurrency was amassed by the clipboard stealer and the crypto mining components.
The earnings reflected in the wallet addresses linked to MyKings are approximately $24.7 million. However, since the botnet uses more than 20 cryptocurrencies in total, this amount is only a part of its total financial gains.
To protect the hardcoded wallet address value from extraction and analysis, the malware encrypts it with a simple ROT cipher. In general, though, no notable upgrades have been spotted on that front in the recent samples.
Apart from the wallet address substitution that diverts transactions, Avast has also spotted a new monetization technique used by MyKings operators involving the Steam gaming platform.
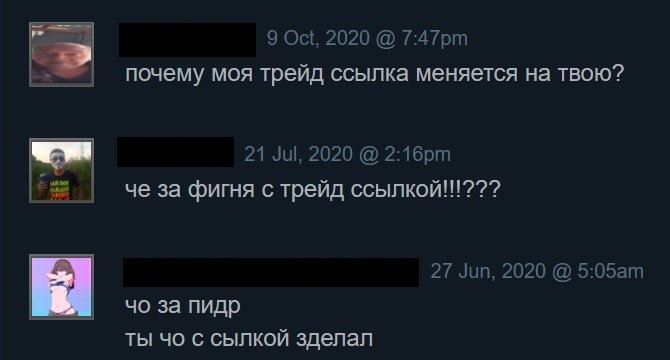
The latest versions of the malware also feature a new URL manipulation system in the clipboard stealer module, which the attackers created to hijack Steam item trade transactions. The module changes the trade offer URL, so the actor is placed at the receiving end, stealing valuable in-game items, etc.
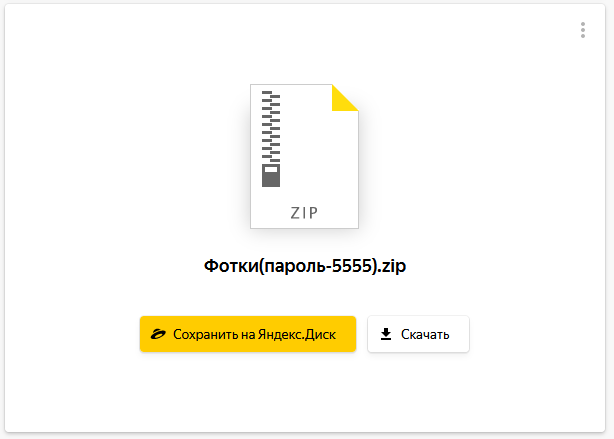
Similar functionality was added for the Yandex disk storage cloud service, with MyKing manipulating the URLs sent by users to their acquaintances.
Also Read: New Data Protection Laws Australia: How Implementation Works
The modified links point to Yandex storage addresses containing RAR or ZIP archives named “photos,” which deliver a copy of the MyKings malware to these machines.
In 2018, MyKings was growing steadily, with the malware reaching 520,000 infections and making millions of dollars for its operators.
Today, it appears that the botnet has grown to new proportions while still managing to remain hidden and free from law enforcement crackdowns.