KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The OptinMonster plugin is affected by a high-severity flaw that allows unauthorized API access and sensitive information disclosure on roughly a million WordPress sites.
Tracked as CVE-2021-39341, the flaw was discovered by researcher Chloe Chamberland on September 28, 2021, with a patch becoming available on October 7, 2021.
All users of the OptinMonster plugin are advised to upgrade to version 2.6.5 or later, as all earlier versions are affected.
Also Read: Top 3 Common Data Protection Mistakes, Revealed
OptinMonster is one of the most popular WordPress plugins used to create beautiful opt-in forms that help site owners convert visitors to subscribers/customers.
It is essentially a lead generator and monetization tool, and thanks to its ease of use and abundance of features, it’s deployed on approximately a million sites.
As Chamberland explains in her vulnerability disclosure report, OptinMonster’s power relies upon API endpoints that allow seamless integration and a streamlined design process.
However, the implementation of these endpoints isn’t always secure, and the most critical example concerns the ‘/wp-json/omapp/v1/support’ endpoint.
This endpoint can disclose data such as the site’s full path on the server, API keys used for requests on the site, and more.
An attacker holding the API key could make changes on the OptinMonster accounts or even plant malicious JavaScript snippets on the site.
The site would execute this code every time an OptinMonster element was activated by a visitor without anyone’s knowledge.
Also Read: The Financial Cost of Ransomware Attack
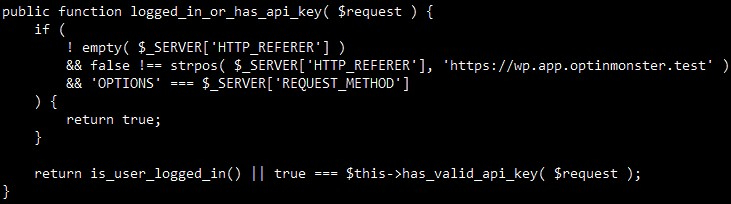
To make matters worse, the attacker wouldn’t even have to authenticate on the targeted site to access the API endpoint, as an HTTP request would bypass security checks under certain, easy to meet conditions.
While the case of the ‘/wp-json/omapp/v1/support’ endpoint is the worse, it’s not the only insecure REST-API endpoint vulnerable to exploitation.
After the researcher’s report reached the OptinMonster team, the developers of the popular WordPress plugin realized that the entire API needed revisiting.
As such, you must install any OptinMonster updates that land on your WordPress dashboard over the following weeks, as these will likely address additional API flaws.
In the meantime, all API keys that could have been stolen were invalidated immediately, and site owners were forced to generate new keys.
This case highlights that even widely deployed and extremely popular WordPress plugins can carry multiple undiscovered flaws for extensive periods.
If you are a site owner, try to use the minimum number of plugins to cover the necessary functionality and usability and apply plugin updates as soon as possible.