KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






A security researcher has publicly disclosed an exploit for a Windows local privilege elevation vulnerability that allows anyone to gain admin privileges in Windows 10.
Using this vulnerability, threat actors with limited access to a compromised device can easily elevate their privileges to help spread laterally within the network, create new administrative users, or perform privileged commands.
The vulnerability affects all supported support versions of Windows 10 before the January 2022 Patch Tuesday updates.
Also Read: 10 Tips For Drafting Key Terms In A Service Agreement
As part of the January 2022 Patch Tuesday, Microsoft fixed a ‘Win32k Elevation of Privilege Vulnerability’ vulnerability tracked as CVE-2022-21882, which is a bypass for the previously patched and actively exploited CVE-2021-1732 bug.
Microsoft attributes the discovery of this vulnerability to RyeLv, who shared a technical analysis of the vulnerability after Microsoft released the patch.
This week, multiple exploits were publicly released for CVE-2022-21882 that allow anyone to gain SYSTEM privileges on vulnerable Windows 10 devices.
After the exploit’s release, Will Dormann, a vulnerability analyst for CERT/CC and Twitter’s resident exploit tester, confirmed that the exploits works and provides elevated privileges.
BleepingComputer also tested the vulnerability and had no problem compiling the exploit and using it to open Notepad with SYSTEM privileges on Windows 10, as shown below. BleepingComputer could not get the exploit to work on Windows 11.
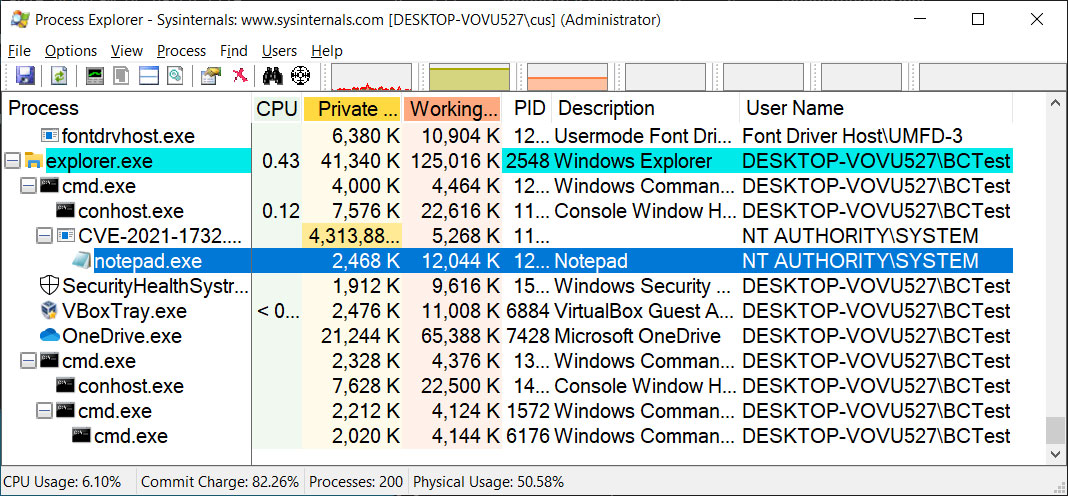
While we only opened Notepad using this exploit, threat actors can also use it to add new users with Administrator privileges or execute other privileged commands.
While we would not normally report on a patched vulnerability, many administrators chose to skip January 2022 updates due to the significant number of critical bugs introduced by the January 2022 updates, including reboots, L2TP VPN problems, inaccessible ReFS volumes, and Hyper-V issues the installation of these updates.
This means that their devices remain unprotected and vulnerable to an exploit that has historically been used in cyberattacks by APT hacking groups.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
With the release of these exploits and as Microsoft released OOB updates that resolve the issues introduced in the January 2022 updates, it is now strongly advised that admins install the updates rather than wait until the February 8th Patch Tuesday.
This same vulnerability was discovered two years ago by Israeli security researcher and Piiano CEO Gil Dabah, who decided not to disclose the bug due to the reduced bug bounty rewards by Microsoft.
Dabah is not alone in his frustrations over Microsoft’s diminishing bug bounty rewards.
In November, security researcher Abdelhamid Nacer released a zero-day privilege elevation exploit due to Microsoft’s decreasing payouts in their bug bounty program.
“Microsoft bounties has been trashed since April 2020, I really wouldn’t do that if MSFT didn’t take the decision to downgrade those bounties,” Naceri told BleepingComputer at the time.
RyeLv noted in his technical writeup for the CVE-2022-21882 vulnerability that the best way to eliminate this bug class is to improve Microsoft’s Windows kernel bug bounties.
“Improve the kernel 0day bounty, let more security researchers participate in the bounty program, and help the system to be more perfect,” advised RyeLv.