KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A compromised Trezor hardware wallet mailing list was used to send fake data breach notifications to steal cryptocurrency wallets and the assets stored within them.
Trezor is a hardware cryptocurrency wallet that allows you to store your crypto assets offline, rather than using cloud-based wallets or wallets stored on your PC that are more vulnerable to theft.
When setting up a new Trezor, a 12 to 24-word recovery seed will be displayed that allows owners to recover their wallets if their device is stolen or lost.
However, anyone who knows this recovery seed can gain access to the wallet and its stored cryptocurrencies, making it vital to store the recovery seed in a safe place.
Starting today, Trezor hardware wallet owners began receiving data breach notifications prompting recipients to download a fake Trezor Suite software that would steal their recovery seeds.
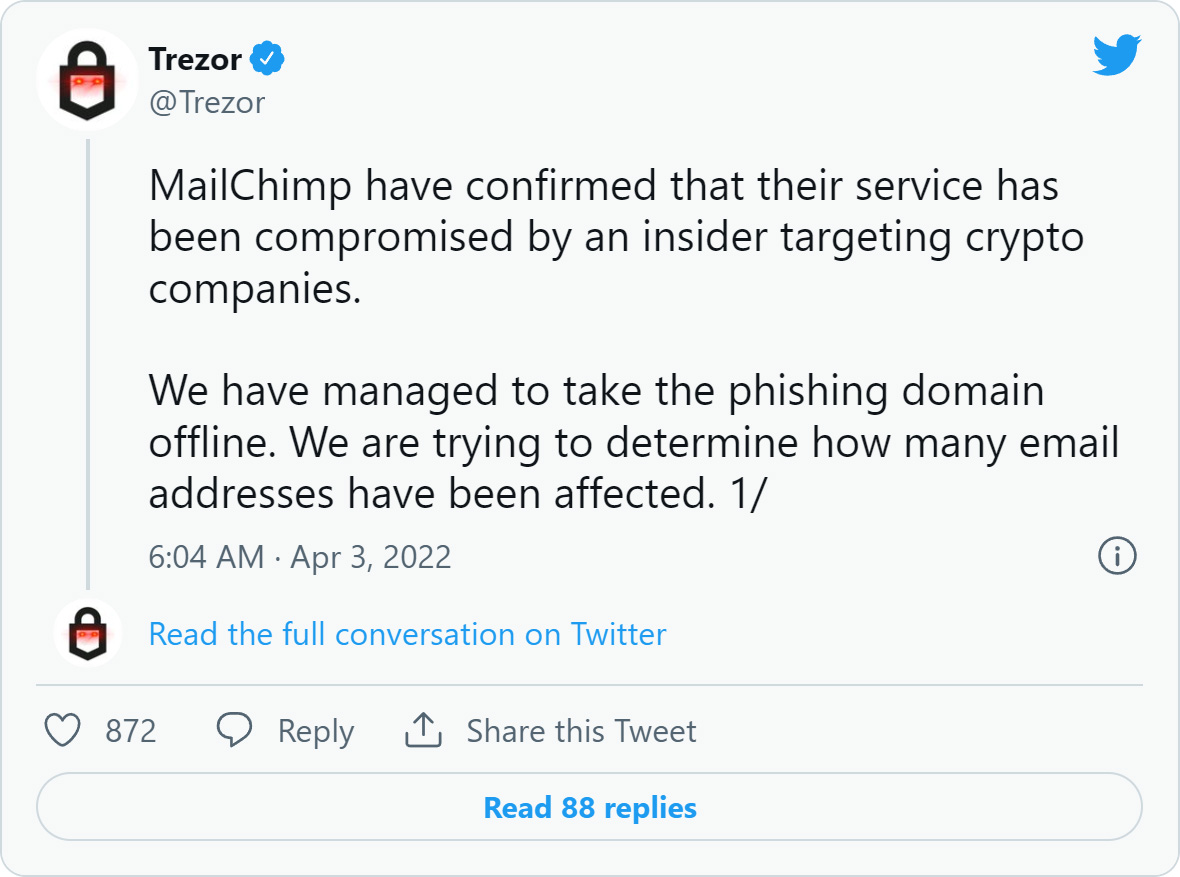
Trezor confirmed on Twitter that these emails were a phishing attack sent through one of their opt-in newsletters hosted at MailChimp.
Trezor later said that MailChimp allegedly confirmed their service was compromised by an “insider” targeting cryptocurrency companies.
Also Read: 5 Best practices for protecting corporate data when an employee leaves
BleepingComputer has contacted MailChimp to learn more about this compromise but has not received a reply at this time.
The phishing attack started with the Trezor hardware wallet owners receiving fake security incident emails claiming to be a data breach notification.
“We regret to inform you that Trezor has experienced a security incident involving data belonging to 106,856 of our customers, and that the wallet associated with your e-email address [email here] is within those affected by the breach.,” reads fake Trezor data breach phishing email.
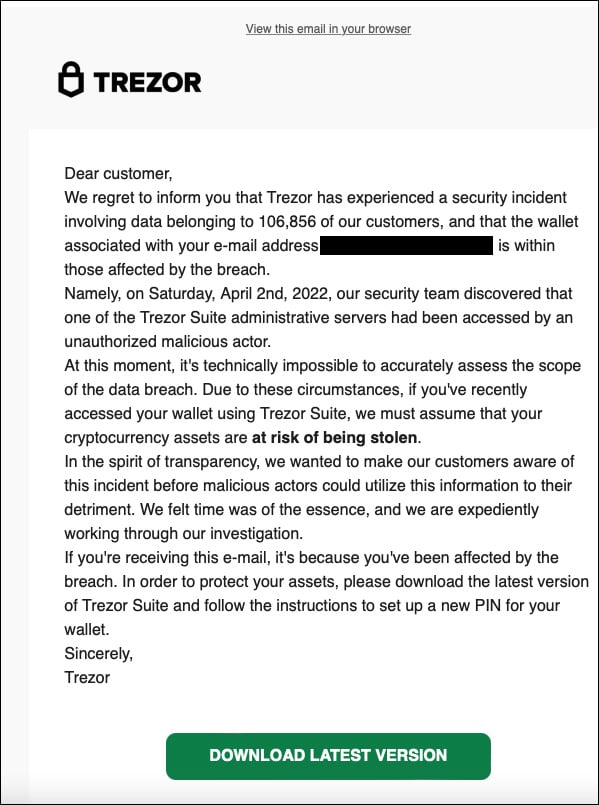
These fake data breach emails say that the company does not know the extent of the breach and that owners should download the latest Trezor Suite to set up a new PIN on their hardware wallet.
Also Read: The necessity of conducting penetration testing and vulnerability assessment
The email includes a ‘Download Latest Version’ button that brings the recipient to a phishing site that appears in the browser as suite.trezor.com.
However, the website is a domain name using Punycode characters that allows the attackers to impersonate the trezor.com domain using accented or Cyrillic characters, with the actual domain name being suite.xn--trzor-o51b[.]com.
It should be noted that the legitimate Trezor website is trezor.io.
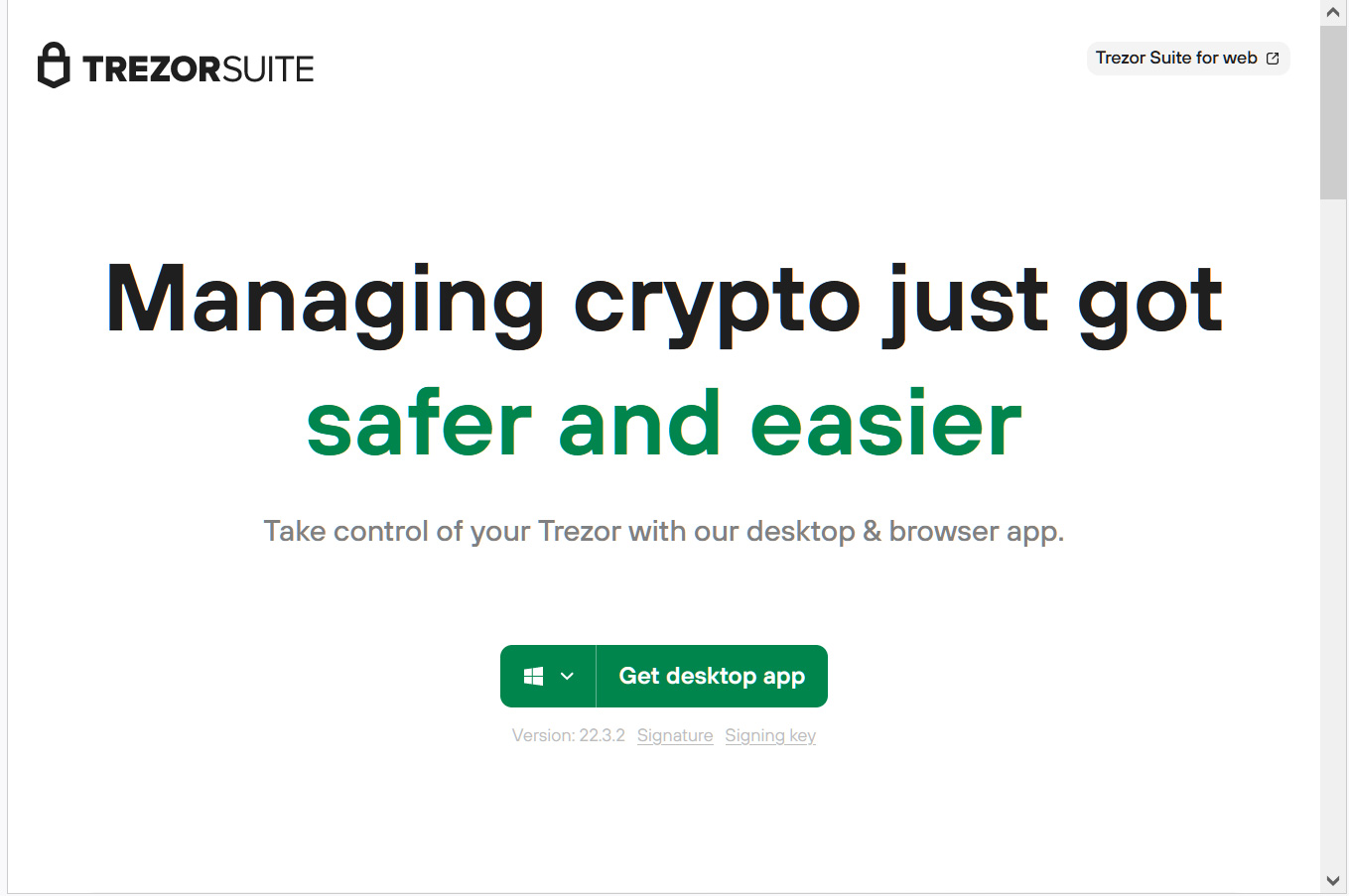
This fake site prompts users to download the Trezor Suite application, as shown below.
In addition to the suite.xn--trzor-o51b[.]com website, the threat actors also created phishing sites at the URLs:
http://trezorwallet[.]org/
trezor[.]us
http://suite.trezoriovpjcahpzkrewelclulmszwbqpzmzgub37gbcjlvluxtruqad[.]onion/ (Tor site)When a visitor downloads the desktop app, it will download a fake Trezor Suite application from the phishing site named ‘Trezor-Suite-22.4.0-win-x64.exe’.
As you can see below, the legitimate Trezor Suite application is signed using a certificate for “Satoshi Labs, s.r.o.” and the fake Windows version [VirusTotal] is signed by a certificate from “Neodym Oy” (right).
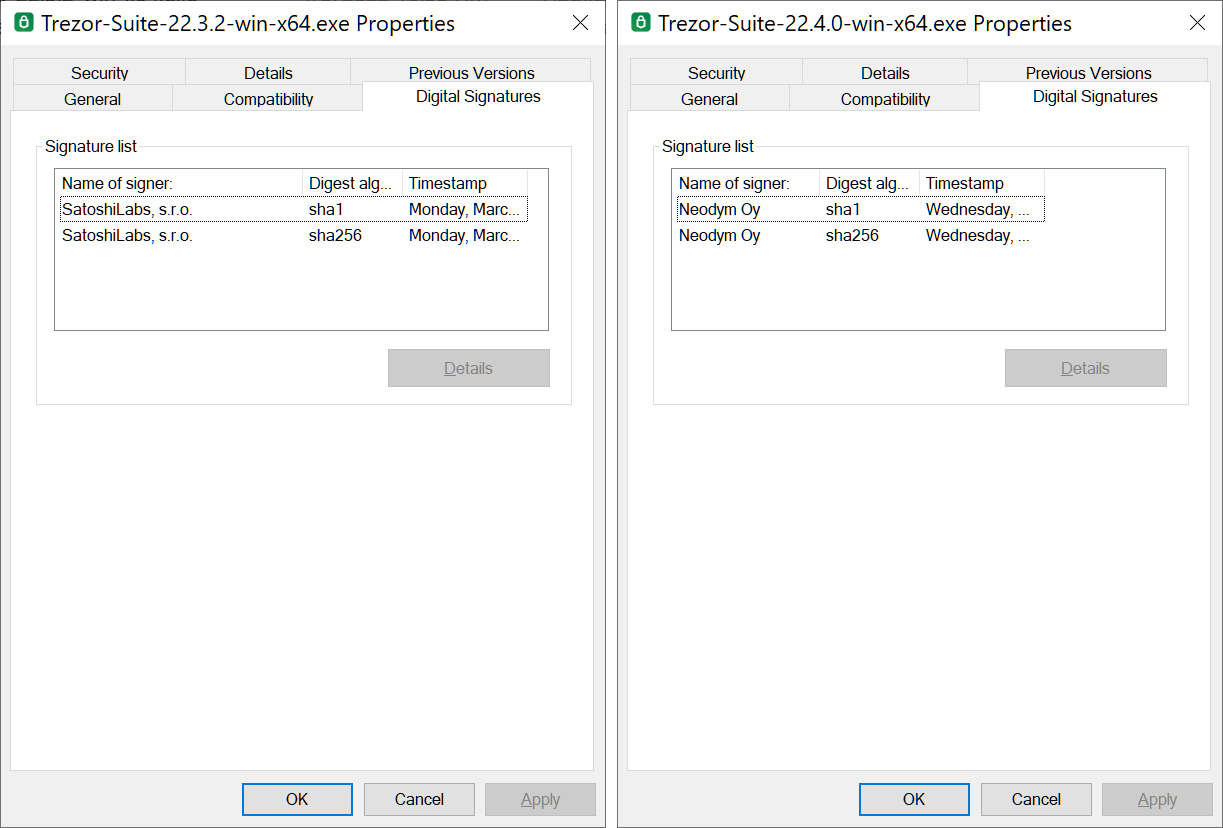
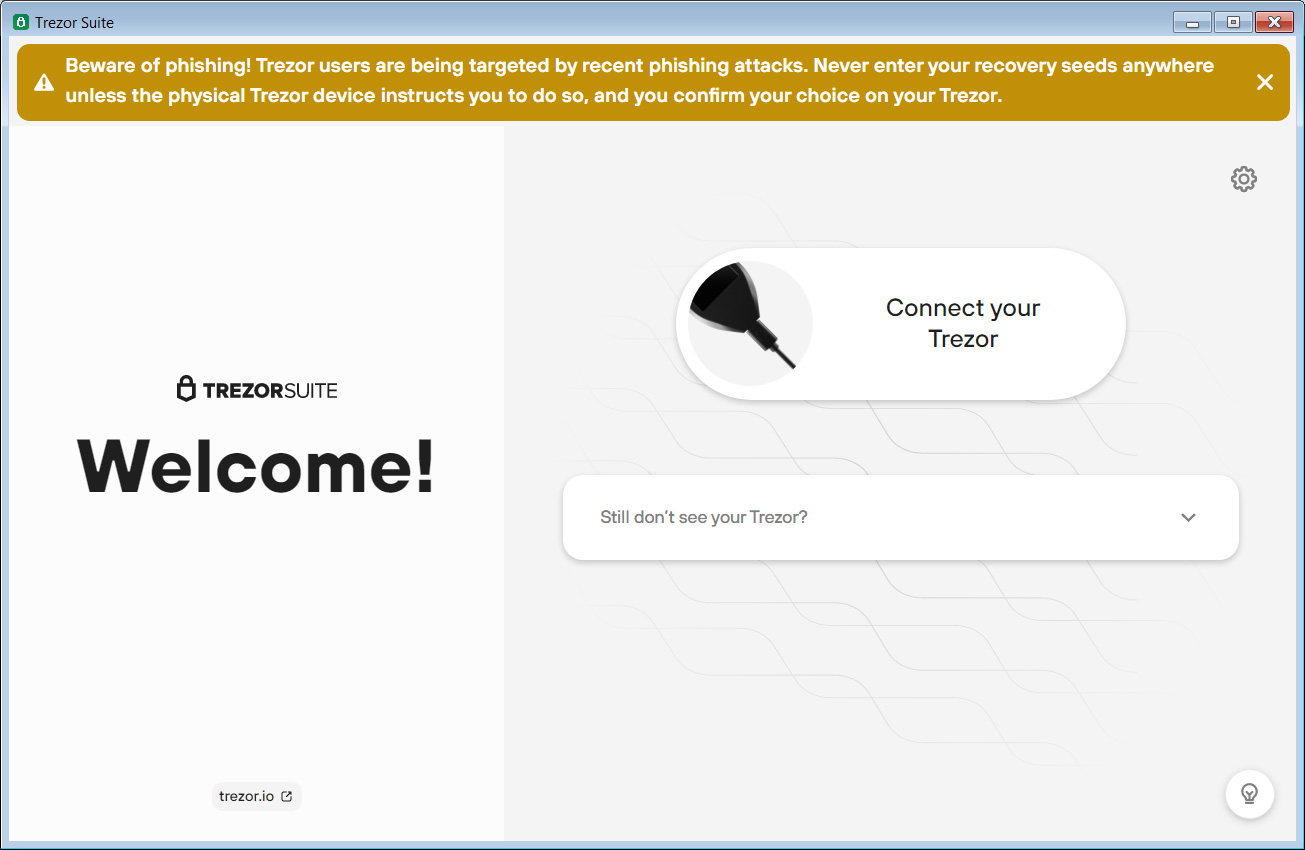
As the Trezor Suite is open source, the threat actors downloaded the source code and created their own modified app that looks identical to the original, legitimate application.
Ironically, this fake suite even includes Trezor’s warning banner about phishing attacks at the top of the application’s screen.
However, once Trezor owners connect their device to the fake Trezor Suite app, it will prompt them to enter their 12 to 24-word recovery phrase, which is sent back to the threat actors.
Now that the threat actors have your recovery phrase, they can use it to import the recovery phrase into their own wallets and steal victims’ cryptocurrency assets.
An almost identical attack targeted Ledger hardware crypto wallet owners wish phishing attacks leading to fake Ledger Live software.
First and foremost, never enter your recovery seed in any app or website. The seed should only be entered directly on the Trezor device you are trying to recover.
As it is easy to create lookalike domains that impersonate legitimate sites, when it comes to cryptocurrency and financial assets, always type the domain you’re trying to reach into your browser rather than relying on links in emails.
This way, you know you are going to the legitimate site rather than a site impersonating it.
Furthermore, Trezor’s official website is at trezor.io, so other domains, such as trezor.com, are unrelated to the crypto hardware wallet company.
Finally, disregard any emails claiming to be from Trezor stating that you were affected by a recent data breach. If you are concerned, rather than click on the link in these emails, contact Trezor directly for more information.