KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Scammers monitor every tweet containing requests for support on MetaMask, TrustWallet, and other popular crypto wallets, and respond to them with scam links in just seconds.
To conduct these targeted phishing attacks, scammers abuse Twitter APIs that allow them to monitor all public tweets for specific keywords or phrases.
If those phrases are present, these same programs will direct Twitter bots under the scammer’s control to automatically reply to the tweets as fake support agents with links to scams that steal cryptocurrency wallets.
These attacks are nothing new, and we reported on them in May. However, these attacks have expanded to other cryptocurrencies, and the scams continue to run rampant.
Therefore, we felt it was vital for our readers to revisit this attack and illustrate how it works, so you do not accidentally become a victim.
Also Read: Data Protection Trustmark Certification: Business Advantage
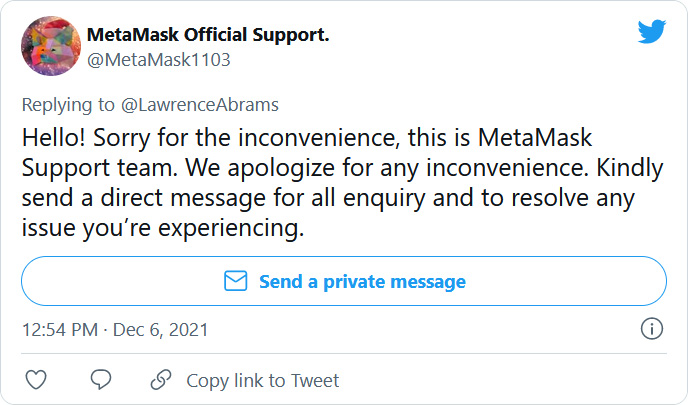
In tests conducted by BleepingComputer, tweets containing the words ‘support,’ ‘help,’ or ‘assistance’ along with the keywords like ‘MetaMask,’ ‘Phantom,’ ‘Yoroi,’ and ‘Trust Wallet’ will result in almost instantaneous replies from Twitter bots with fake support forms or accounts.
Other keywords have mixed results, such as wallets’ names and the word ‘stolen.’
Our first test of these cryptocurrency scam bots was to pack a tweet with numerous keywords and see what would happen.
I need trust wallet metamask phantom yoroi support! I lost all my crypto and password recovery phrase.
Come on all you bots!— Lawrence Abrams (@LawrenceAbrams) December 6, 2021
We then conducted further tests to try and narrow down what keywords would trigger the bot’s replies.
Within seconds of posting our tests, we received replies from numerous scam accounts pretending to be MetaMask and TrustWallet support accounts, “previous victims,” or helpful users.
 | 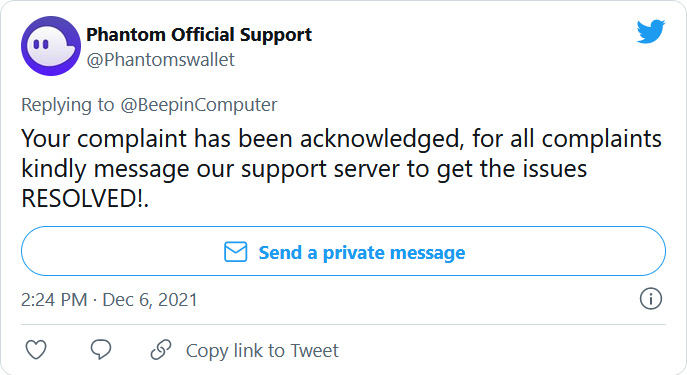 |
 |  |
All of the scammer’s replies share a common purpose – to steal the recovery phrases for a victim’s wallet, which the attackers can then use to import the wallet onto their own devices.
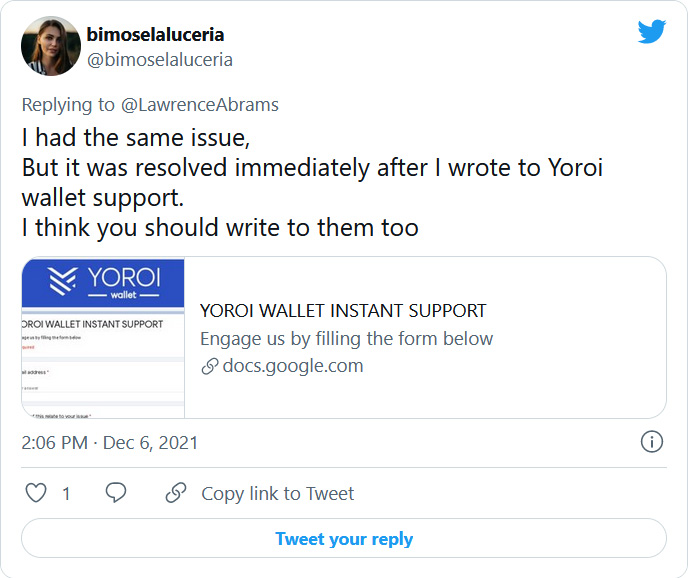
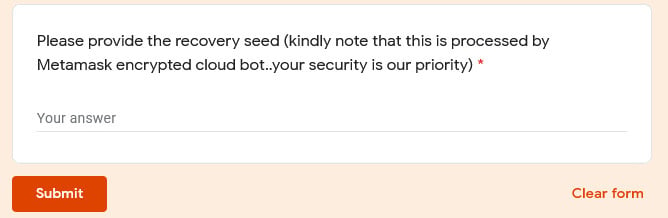
To steal the recovery phrases (aka seed phrases), the threat actors set up support forms on Google Docs and other cloud platforms.
These forms impersonate a basic support form, asking the user for their email address, the problem they are having, and their wallet’s recovery phrase, as shown by the fake MetaMask support form below.
Also Read: Data Anonymisation: Managing Personal Data Protection Risk
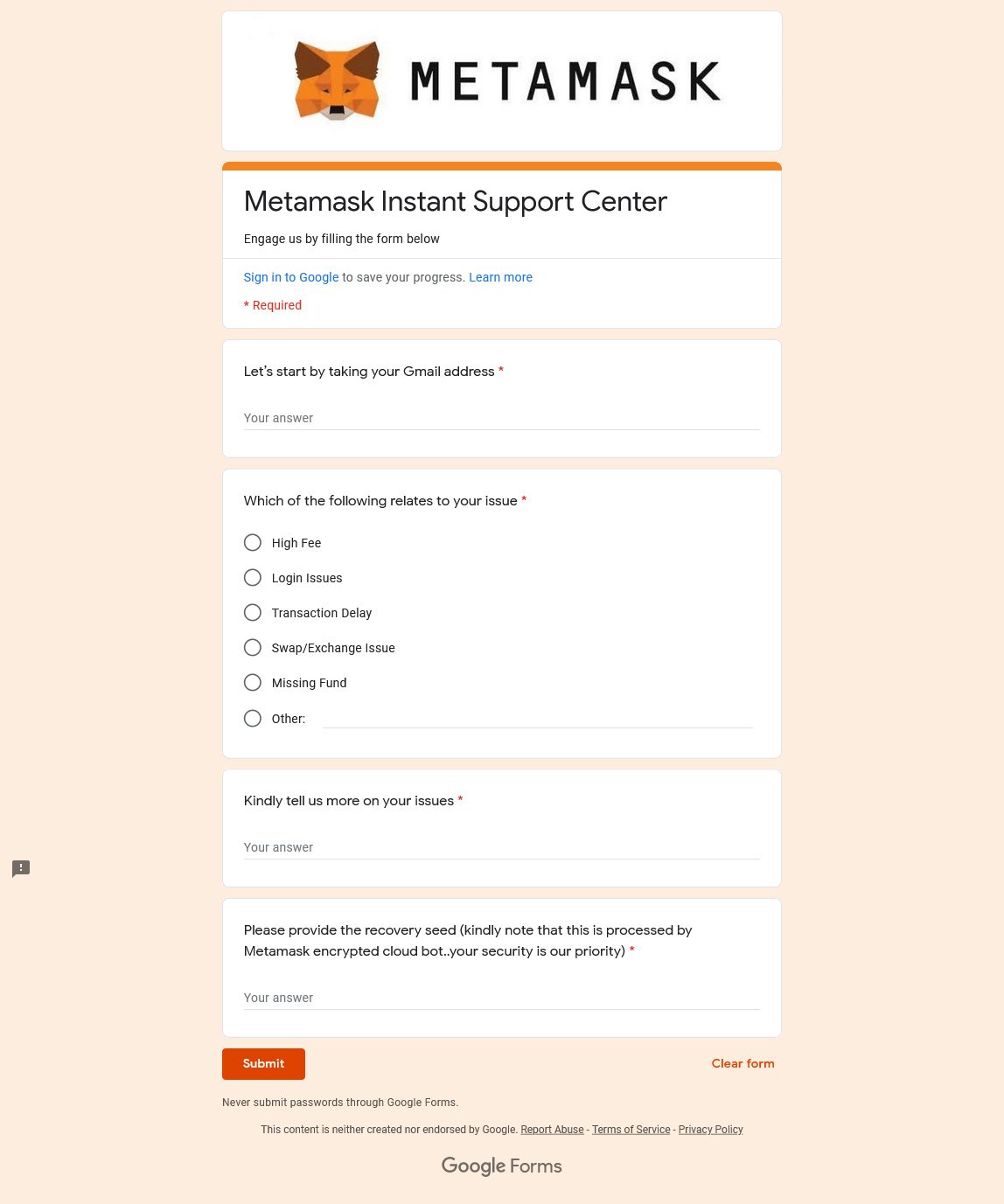
When prompting for the recovery phrase, they include silly language about it being processed by their “encrypted cloud bot,” likely to try and convince the user to post the sensitive information.
Once the recovery phrase is sent to the attackers, it’s game over and they now have full access to the cryptocurrency within your wallet and can transfer it to other wallets under their control.
Before you say that no one falls for these scams, sadly, that is untrue, and Twitter users have had their wallets, cryptocurrency, and NFTs, stolen.
@merchant_token I wasn’t able to change my withdrawal address from Binance to metamask, so I contacted and have been fooled by a fake metamask support @MetaMasko who stole my tokens from my Metamask Wallet.— Sébastien FC (@fc_sebastien) July 9, 2021
Thank you Kenzie. I was getting what I thought was customer support for funds that were missing since last week. The fake customer support shared a link , and through that they extracted my Metamask. I’ve been all day trying to at least recover art that wasn’t sold.— Nightversion (@NightversionHQ) November 24, 2021
Twitter told BleepingComputer that using Twitter APIs to spam is against the rules and that they are actively working on new methods to prevent these attacks.
“It’s against our rules to use scam tactics on Twitter to obtain money or private financial information, including through automated activity. Our Developer Policy also strictly prohibits the use of the Twitter API and developer products to spam people,” explained a Twitter spokesperson.
“When we identify apps or accounts that violate these policies, we take appropriate enforcement action. We’re constantly adapting to bad actors’ evolving methods and we’ll continue to move quickly to address cryptocurrency scams on the platform as they evolve. “
As a general rule, you should never share your wallet’s recovery phrase with anyone. The recovery phrase is only for you, and no legitimate support person from MetaMask, TrustWallet, or elsewhere will ever ask for it.
It is also important to remember not to share your screen with an untrusted user who then requests that you display your recovery phrase. At that point, they can simply take a screenshot and write it down manually.
Ultimately, these attacks will continue unless Twitter figures out a way to prevent these bots from running rampant, restrict the use of specific keywords, or put more stringent controls on who can join their developer platform.
Update 12/7/21: Added statement from Twitter.