KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Security researchers found malware embedded within the official application of APKPure, a popular third-party Android app store and an alternative to Google’s official Play Store.
Android users use the application to install apps and games hosted on APKPure’s platform, supposedly identical to those available through the Play Store.
The malware was discovered by Kaspersky and Dr.Web malware analysts embedded within an advertisement SDK included with APKPure version 3.7.18.
As they discovered, it looks like a variant of the Triada trojan first spotted by Kaspersky in 2016 [1, 2], capable of spamming users of infected devices with ads and deliver additional malware.
Also Read: PDPA Singapore Guidelines: 16 Key Concepts For Your Business
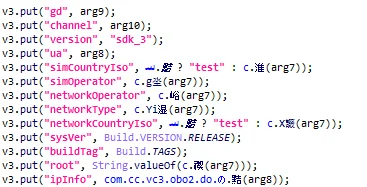
“The identified malicious code embedded in APKPure operates in the following way: upon launch of the application, the payload is decrypted and launched,” Kaspersky said. “It then collects information about the user device and sends it to the C&C server.”
“Then, a Trojan is loaded that has much in common with the notorious Triada malware, in that it can perform a range of actions – from displaying and clicking ads to signing up for paid subscriptions and downloading other malware.”
Next, depending on its operators’ instructions and monetizing scheme (ads or pay-per-install), it will:
The damage inflicted by this trojan varies depending on the Android version running on the compromised devices, ranging from being signed up for paid subscriptions and seeing intrusive ads on current versions to having unremovable malware like xHelper deployed on the system partition.
While no official download stats are available for the APKPure app, Kaspersky says that it has so far blocked the malware on the devices of 9,380 Android users running its security solutions on their devices.
Both Kaspersky and Dr.Web reported their findings to APKPure’s developers, who have released APKPure 3.17.19 today without the malicious code.
Indicators of compromise, including APKpure app, payload, and malware sample hashes, are available at the end of Kaspersky’s report.
Also Read: Data Protection Officer Singapore | 10 FAQs
BleepingComputer has reached out to APKPure’s development team for more information but has not heard back.