KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







North Korean state hacking group APT37 targets South Korean journalists, defectors, and human rights activists in watering hole, spear-phishing emails, and smishing attacks delivering malware dubbed Chinotto capable of infecting Windows and Android devices.
APT37 (aka Reaper) has been active since at least 2012 and is an advanced persistent threat group (APT) linked to the North Korean government with high confidence by FireEye.
Other security companies also track it as StarCruft (Kaspersky Lab), Group123 (Cisco Talos), or FreeMilk (Palo Alto Networks).
The group is known for historically targeting individuals of interest to the North Korean regime, including journalists, diplomats, and government employees.
Chinotto, the malware deployed in their most recent campaign discovered by Kaspersky security researchers, allows the hacking group to control compromised devices, spy on their users via screenshots, deploy additional payloads, harvest data of interest, and upload it to attacker-controlled servers
Also Read: How can businesses protect their enterprise from Business Email Compromise (BEC) attacks?
As Kaspersky found, this backdoor was delivered onto victims’ devices months after the initial intrusions. In one case, the hackers waited as much as six months before installing Chinotto, which allowed them to exfiltrate sensitive data from the infected device.
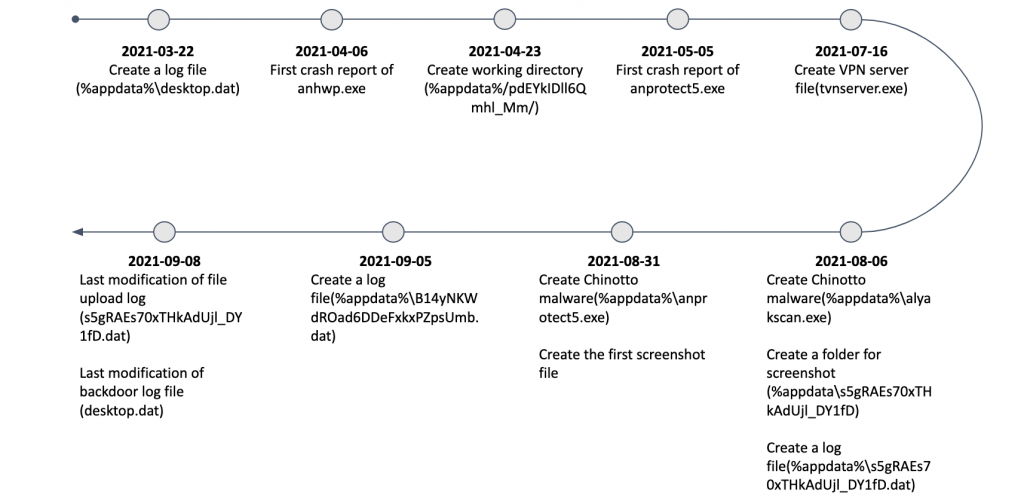
“We suspect this host was compromised on March 22, 2021. [..] The malware operator later delivered the Chinotto malware in August 2021 and probably started to exfiltrate sensitive data from the victim,” Kaspersky said.
“Based on what we found from this victim, we can confirm that the malware operator collected screenshots and exfiltrated them between August 6, 2021 and September 8, 2021.”
Chinotto is highly customizable malware, as shown by many variants found while analyzing the campaign, sometimes several payloads deployed on the same infected devices.
“The malware authors keep changing the capabilities of the malware to evade detection and create custom variants depending on the victim’s scenario,” the researchers said.
The malware’s Windows and Android variants use the same command-and-control communication pattern and send the stolen info to web servers located mainly in South Korea.
As the Android variants request for extended permissions on compromised devices, once granted, Chinotto can use them to collect large amounts of sensitive data, including the victims’ contacts, text messages, call logs, device info, and even audio recordings.
If it also finds and steals the victim’s credentials, it allows APT37 operators to reach out to other targets using the stolen credentials via email and social media.
Also Read: 6 ways to recognize a potential phishing scam and what to do if you receive one
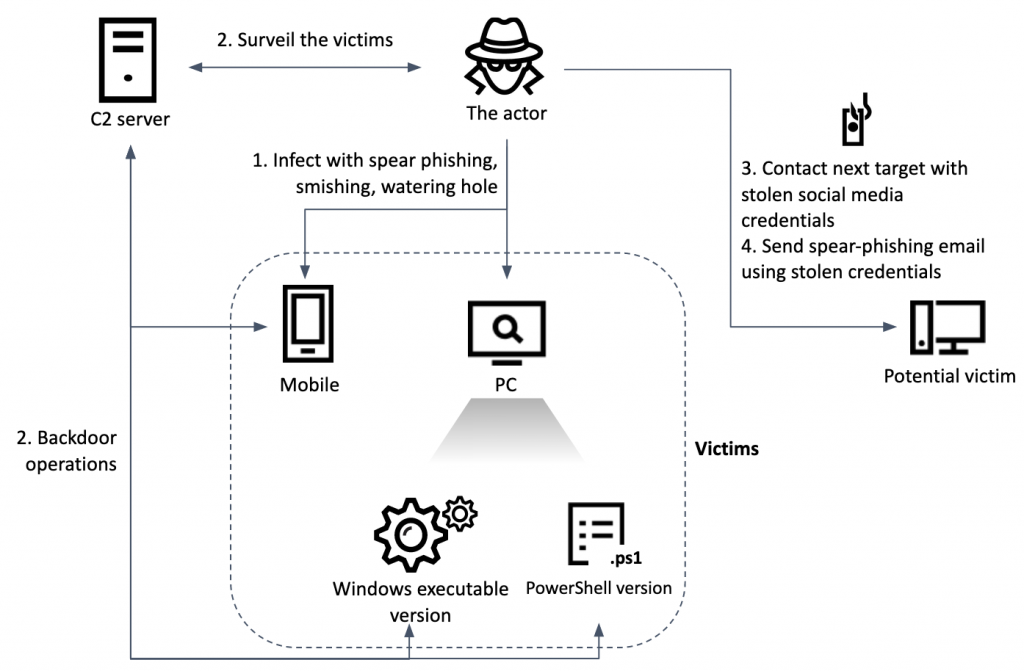
“To sum up, the actor targeted victims with a probable spear-phishing attack for Windows systems and smishing for Android systems. The actor leverages Windows executable versions and PowerShell versions to control Windows systems,” Kaspersky concluded.
“We may presume that if a victim’s host and mobile are infected at the same time, the malware operator is able to overcome two-factor authentication by stealing SMS messages from the mobile phone.”