KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A vulnerability in Argo CD, used by thousands of orgs for deploying applications to Kubernetes, can be leveraged in attacks to disclose sensitive information such as passwords and API keys.
Tracked as CVE-2022-24348, the path-traversal flaw was discovered by the security research team at Apiiro and can lead to privilege escalation, information disclosure, and lateral movement attacks.
Threat actors can exploit the vulnerability by loading a malicious Kubernetes Helm Chart YAML file onto the target system, allowing the extraction of sensitive information from other applications.
Also Read: Managing employee data under Singapore’s PDPA
The diagram below shows how an attack flow leveraging CVE-2022-24348 would work.
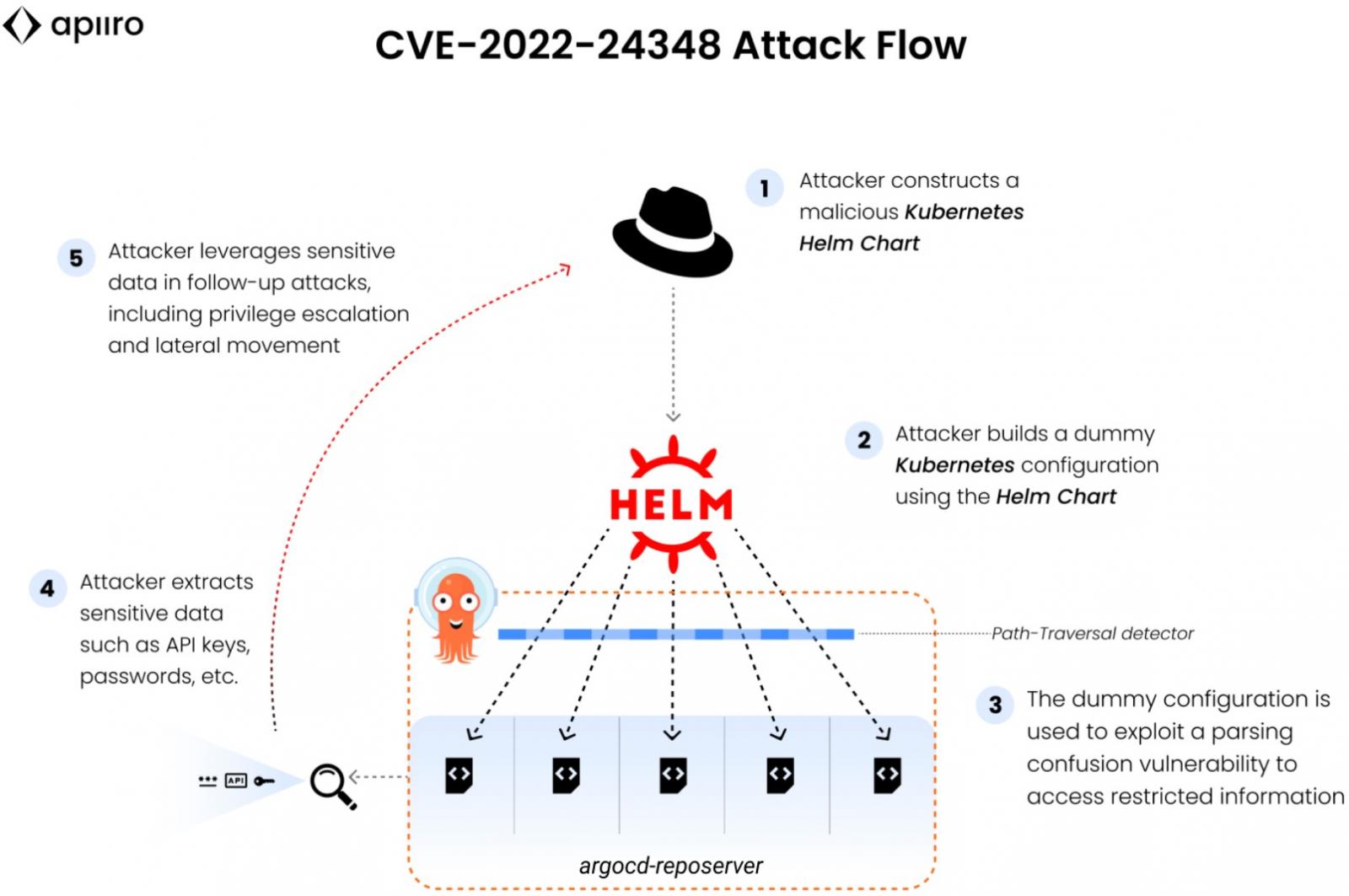
The prerequisite for a successful attack is to have permission to create or update applications and know or guess the full path to a file containing valid YAML.
Meeting these requirements opens the way to create a malicious Helm chart to consume YAML as values files, eventually gaining access to normally inaccessible data.
Argo CD is being used by thousands of organizations globally, so discovering the vulnerability is significant and requires immediate attention by developers and admins.
The developers of Argo CD envisioned the possibility of a malicious actor using Helm value files outside of the chart folder and attempted to address the issue with a new check mechanism introduced in version 1.3.0, released in 2019.
However, as discovered by Apiiro now, there’s a way to bypass the anti-path-traversal checks if the listed valueFiles are made to look like a URI.
The special parser treats the local file path as a URI, assumes it has received an HTTP request, and accepts it without additional sanity tests.
“Because the reposerver uses a monolithic and deterministic file-structure, all the other out-of-bound applications have a definite and predictable format and path,” – explains Apiiro
“An attacker can assemble a concatenated, direct call to a specified values.yaml file, which is used by many applications as a vassal for secret and sensitive values.”
Also Read: Race against time: How CSA dissect cyberattacks using sophisticated gadgets
The impact of this is the disclosure of contents of files on the same repository and the abuse of the contents to perform additional malicious actions.
The Apiiro team reported the problem to the vendor on January 30, 2022, and received an almost immediate response.
Argo CD released a security update that contains the fix for CVE-2022-24348 today, with version 2.3.0-rc4. Everyone is recommended to upgrade to it as there are no workarounds.
For more details from the vendor’s side, check out this security advisory published by the Argo CD team on GitHub.