KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





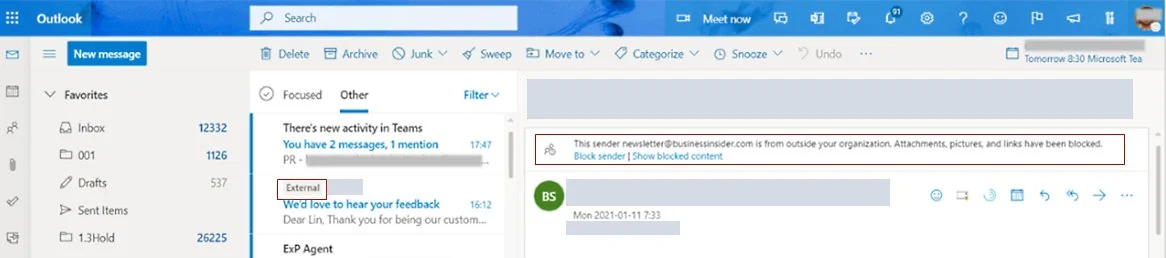
The “external sender” warnings shown to email recipients by clients like Microsoft Outlook can be hidden by the sender, as demonstrated by a researcher.
Turns out, all it takes for attackers to alter the “external sender” warning, or remove it altogether from emails is just a few lines of HTML and CSS code.
This is problematic as phishing actors and scammers can simply include some HTML and CSS code in their outgoing emails to tamper with the wording of the warning message or to make it disappear altogether.
Email security products such as enterprise email gateways are often configured to display the “external sender” warning to a recipient when an email arrives from outside of the organization.
IT administrators enforce displaying such warnings to safeguard users against phishing and scam emails arriving from untrusted sources.
However, this week a researcher has shown a rather simple way that email senders can use to circumvent this protection applied by email security products.
By appending just a few lines of HTML and CSS code, researcher Louis Dion-Marcil showed how an external sender could hide the very warning from an email message.
Also Read: Data Protection Officer Singapore | 10 FAQs
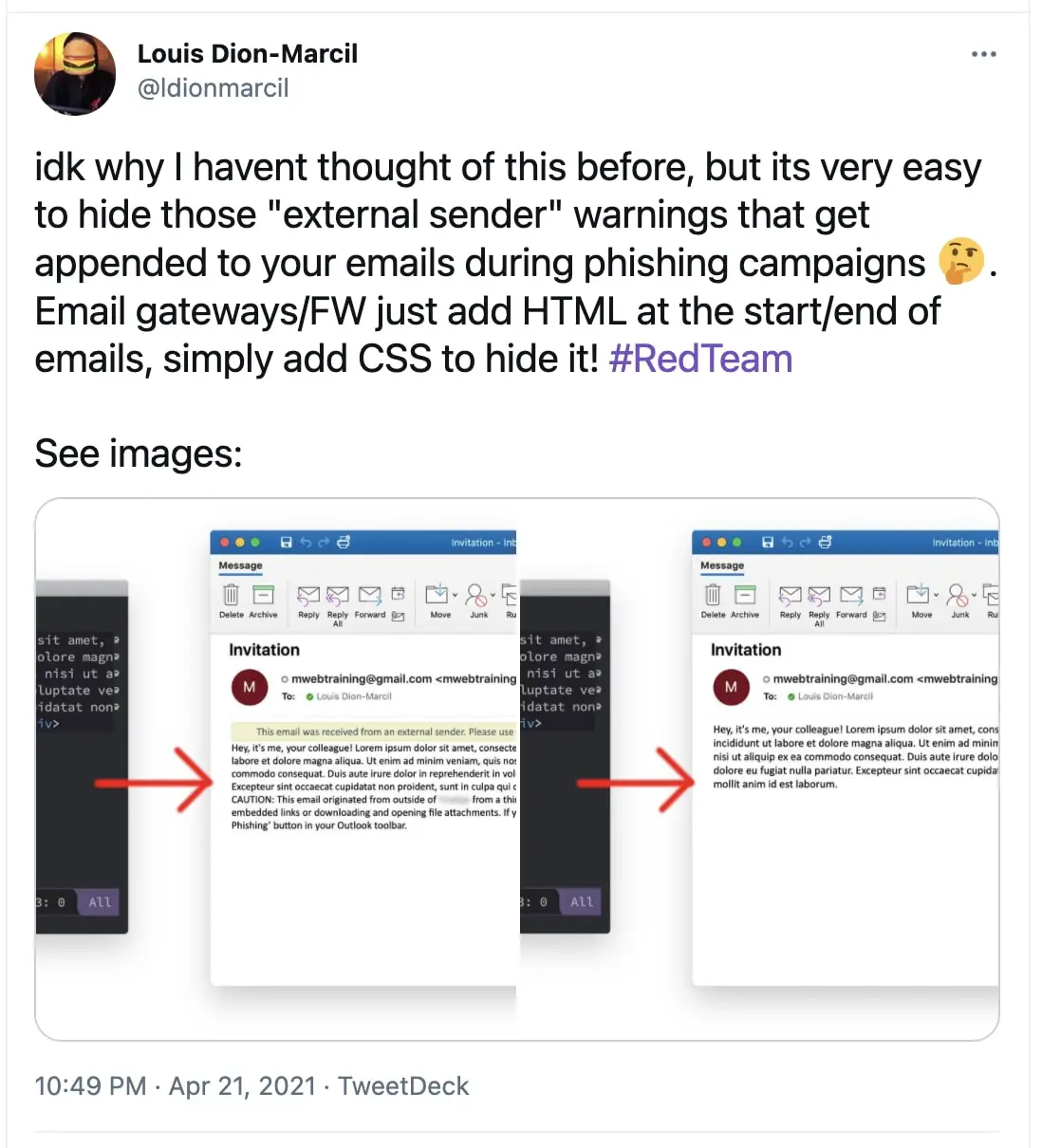
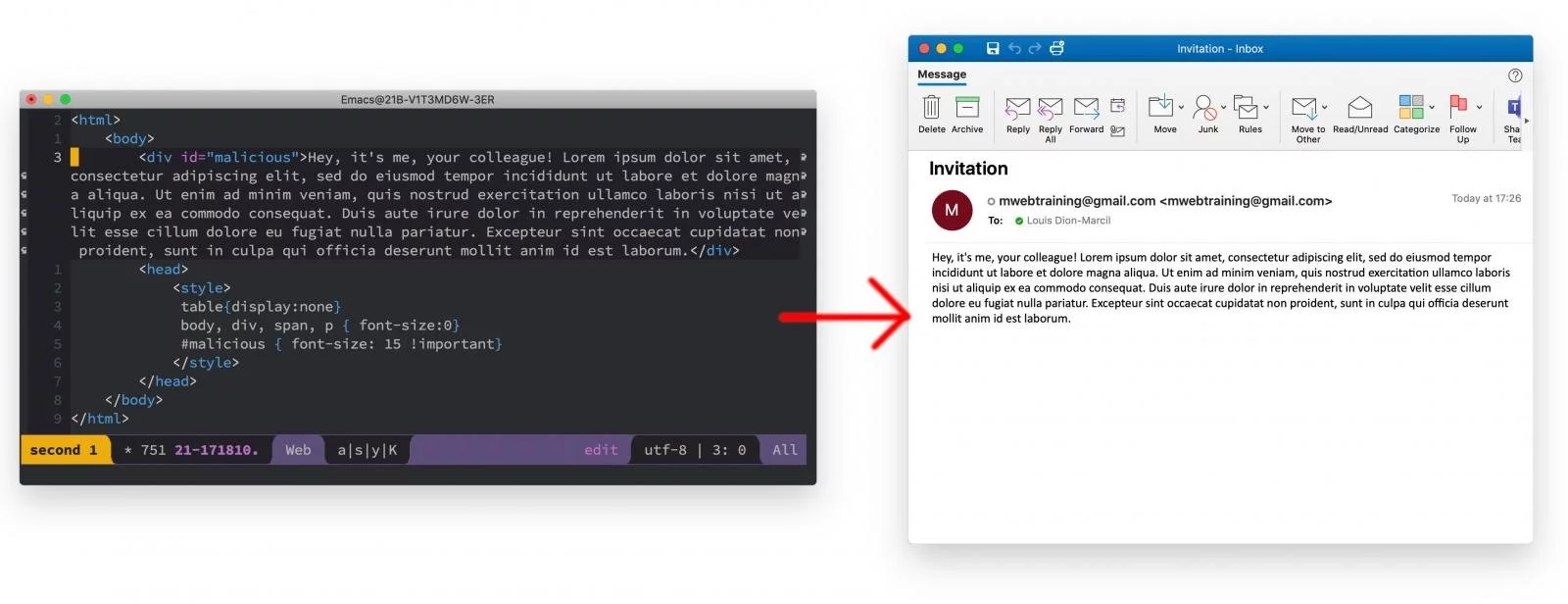
This happens because email security products and gateways that are intercepting and scanning incoming emails for suspicious content are simply injecting the “external sender” warning as an HTML/CSS code snippet in the email body itself, as opposed to the UI of the native email client displaying the message.
As such, an attacker-crafted email that contains CSS instructions to override the warning snippet’s CSS code (display rules) can make the warning disappear altogether:
Another researcher who alluded to also being aware of this behavior from the past implied an attacker could also exploit this flaw to alter the warning message:
“You could even fake HTML and CSS to [sic] instead of hiding it, indicating the content was scanned and deemed safe,” said Jean Maes in the same thread.
Dion-Marcil has shared some insights with BleepingComputer on this behavior:
The researcher says that this is not a bug in any email client app per se, and is client-agnostic.
“It’s not really a client bug, so it’s client agnostic. nothing to do with Outlook really. I just happened to take a screenshot in Outlook, but [this] would work in Gmail, Thunderbird, etc.”
“It’s a limitation of HTML emails. If the warning is added to the HTML body, and the attacker obviously controls the HTML body, then they can add CSS rules to hide those elements.”
“It is impossible to fix, other than moving to a non-HTML-based warning label,” Dion-Marcil told BleepingComputer in an email interview.
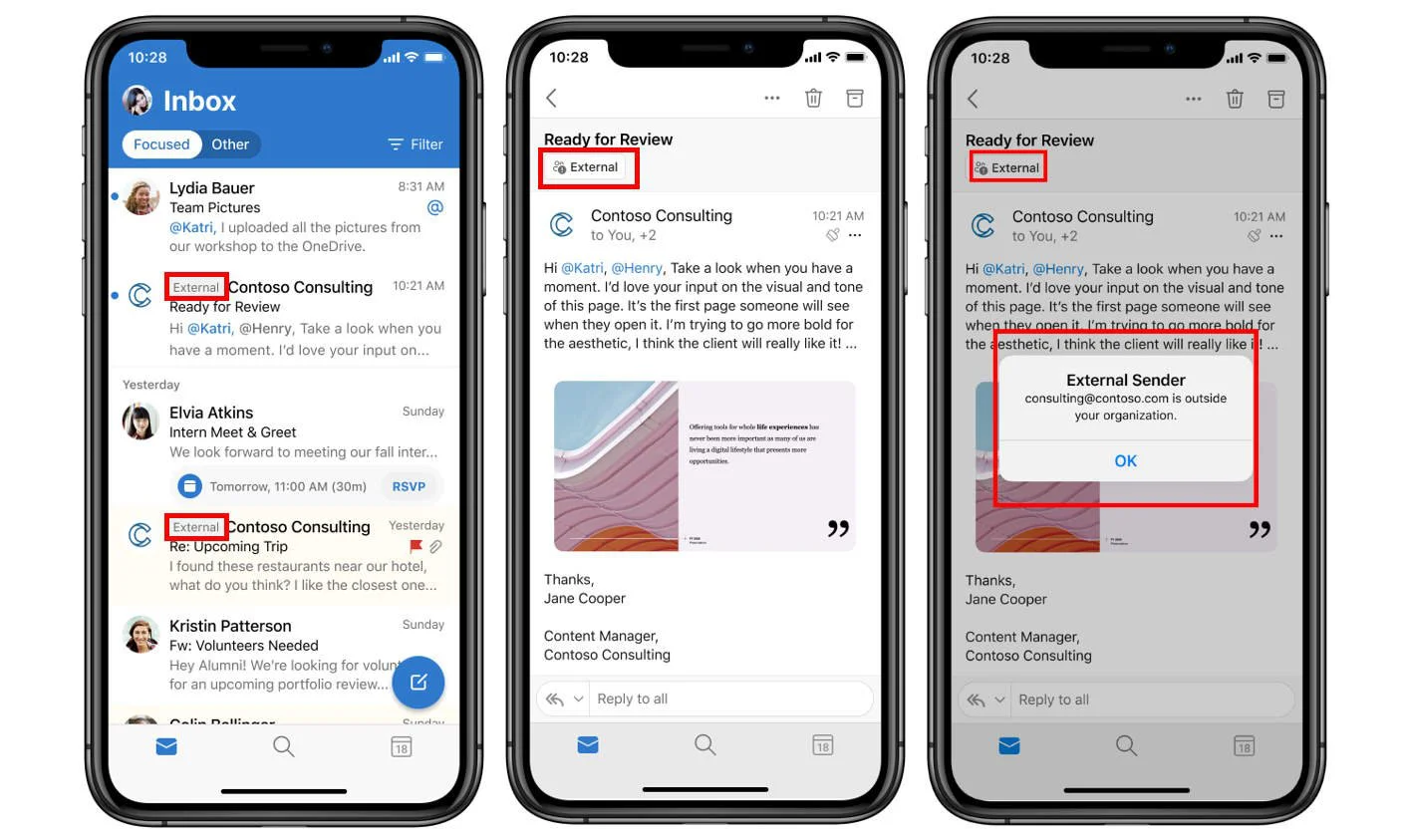
Last month, Microsoft Exchange announced the addition of an upcoming “external” email tagging feature, as reported by BleepingComputer.
If IT administrators enable this feature on their organization’s Exchange server, emails received from external sources, when parsed by native clients like Microsoft Outlook, will carry the “external” tags displayed within the native email client app’s UI, as opposed to the email body.
As an example, screenshots shared by Microsoft show external emails received in Microsoft Outlook and Outlook mobile apps showing the “External” tag in the native email client’s UI:
Also Read: The DNC Singapore: Looking At 2 Sides Better
Once the “external” email tagging feature rolls out to different Office 365 environments, however, it will be disabled by default.
As such, IT administrators interested in enabling this feature will need to use the Get-ExternalInOutlook and Set-ExternalInOutlook PowerShell cmdlets to view and modify external sender identification configuration in supported Outlook versions.
“If you enable the cmdlet, within 24-48 hours, your users will start seeing a warning tag in email messages received from external sources (outside of your organization),” says Microsoft.
“In Outlook mobile, by tapping on the External tag at the top of the message, the user will see the email address of the sender.”
Regardless of whether an email contains the “external sender” warning, or on the contrary, touts itself to be “safe,” users should be careful prior to opening any links or attachments in the emails they receive.
Update 10:52 AM: Added quotes received from Dion-Marcil.