KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Cybercriminals have created a fake Microsoft DirectX 12 download page to distribute malware that steals your cryptocurrency wallets and passwords.
Even though the site comes complete with a contact form, privacy policy, a disclaimer, and a DMCA infringement page, there is nothing legitimate about the website or the programs it distributes.

Also Read: PDPA Singapore Guidelines: 16 Key Concepts For Your Business
When users click on the Download buttons, they will be redirected to an external page that prompts them to download a file. Depending on whether you click on the 32-bit or 64-bit version, you will be offered a file named ‘6080b4_DirectX-12-Down.zip’ [VirusTotal] or ‘6083040a__Disclaimer.zip’ [VirusTotal].
What both of these files have in common is that they lead to malware that tries to steal victims’ files, passwords, and cryptocurrency wallets.
First discovered by security researcher Oliver Hough, when the fake DirectX 12 installers are launched, they will quietly download malware from a remote site and execute it.
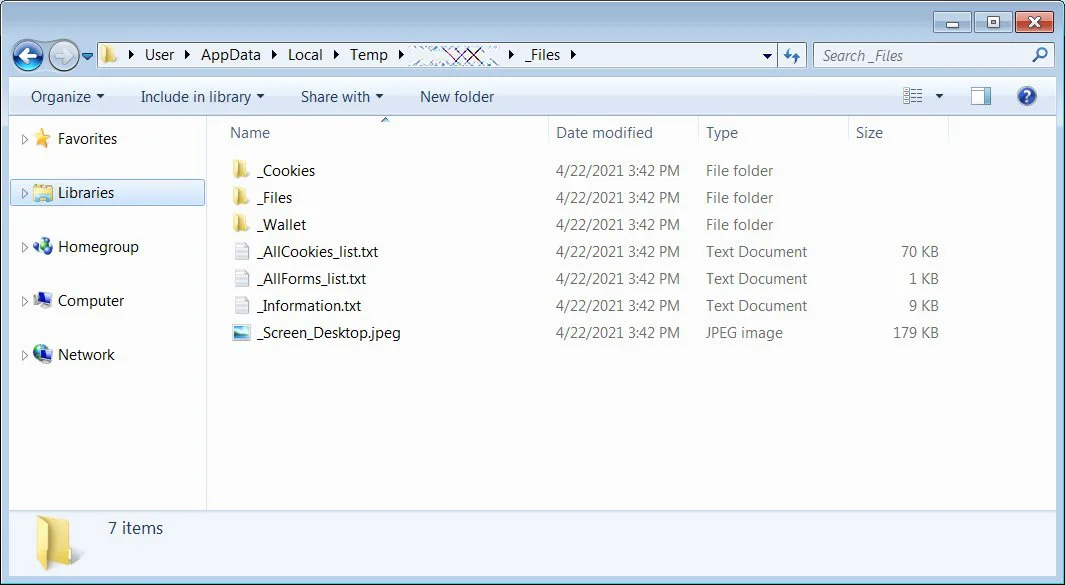
This malware is an information-stealing malware that attempts to harvest a victim’s cookies, files, information about the system, installed programs, and even a screenshot of the current desktop.
With the cryptocurrency craze in full swing, the malware developers also attempt to steal a wide variety of cryptocurrency wallets for Windows software, such as Ledger Live, Waves.Exchange, Coinomi, Electrum, Electron Cash, BTCP Electrum, Jaxx, Exodus, MultiBit HD, Aomtic, and Monero.
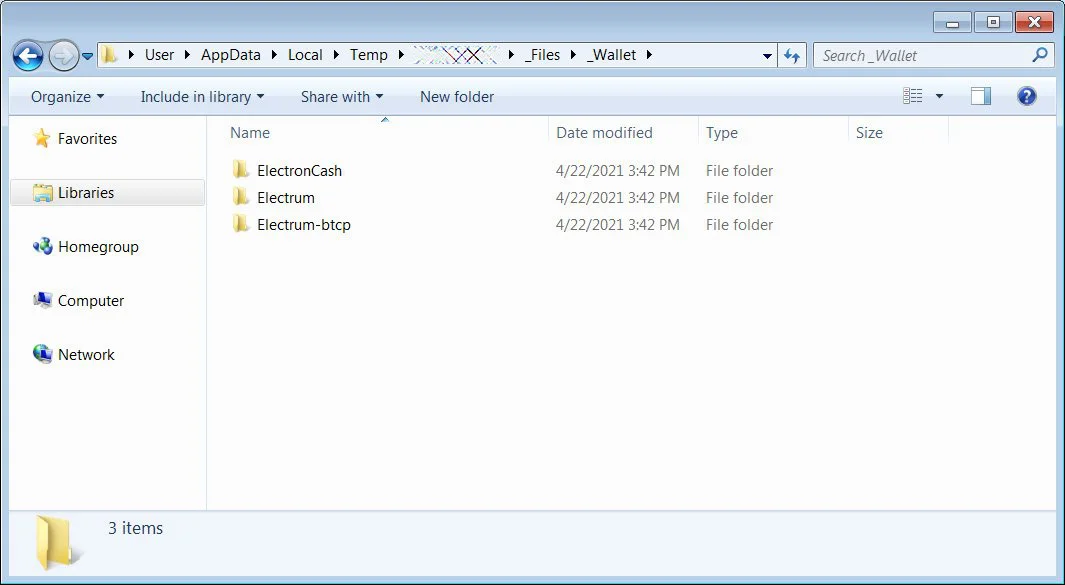
All of the data is collected into a %Temp% folder, which the malware will zip up and send back to the attacker. The attack can then analyze the data and use it for other malicious activities.
Threat actors are increasingly creating fake websites, and in many cases far more convincing websites, to distribute malware.
In the past, BleepingComputer has reported on malware distributors creating fake sites promoting ProtonVPN, Windows system cleaners, and BleachBit that push password-stealing Trojans on unsuspecting visitors.
With the web continuing to be the wild west, it is vital to take a paranoid approach to download software and only install software from trusted sites or the developer’s site.
Also Read: Data Protection Officer Singapore | 10 FAQs
As DirectX is a Microsoft feature, it makes sense that you should only install it from Microsoft and that downloading it from anywhere else can likely lead you to trouble.