KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The Federal Bureau of Investigation (FBI) warned US companies in a recently updated flash alert that the financially motivated FIN7 cybercriminal group targeted the US defense industry with packages containing malicious USB devices to deploy ransomware.
The attackers mailed packages containing ‘BadUSB’ or ‘Bad Beetle USB’ devices with the LilyGO logo, commonly available for sale on the Internet.
Also Read: The Top 10 Primary GDPR Requirements PDF To Secure Business
They used the United States Postal Service (USPS) and United Parcel Service (UPS) to email the malicious packages to businesses in the transportation and insurance industries since August 2021 and defense firms starting with November 2021.
FIN7 operators impersonated Amazon and the US Department of Health & Human Services (HHS) to trick the targets into opening the packages and connecting the USB drives to their systems.
Since August, reports received by the FBI say that these malicious packages also contain letters about COVID-19 guidelines or counterfeit gift cards and forged thank you notes, depending on the impersonated entity.
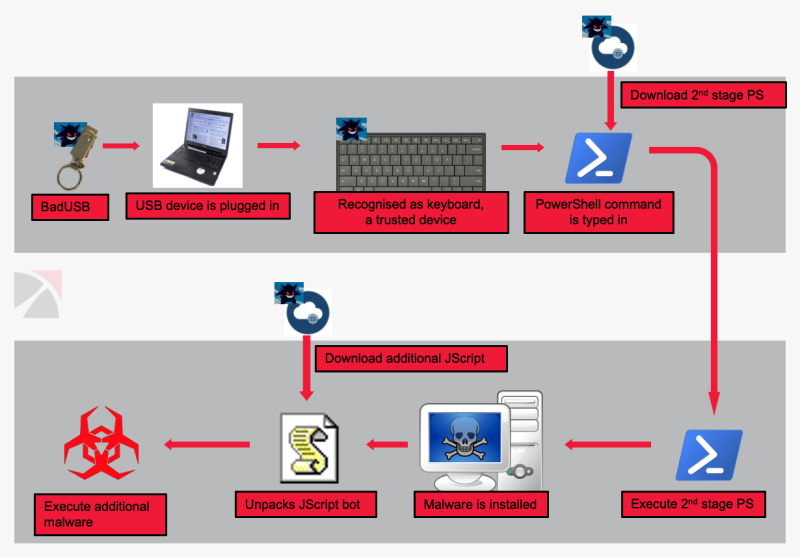
After the targets plug the USB drive into their computers, it automatically registers as a Human Interface Device (HID) Keyboard (allowing it to operate even with removable storage devices toggled off).
It then starts injecting keystrokes to install malware payloads on the compromised systems.
FIN7’s end goal in such attacks is to access the victims’ networks and deploy ransomware (including BlackMatter and REvil) within a compromised network using various tools, including Metasploit, Cobalt Strike, Carbanak malware, the Griffon backdoor, and PowerShell scripts.
These attacks follow another series of incidents the FBI warned about two years ago when FIN7 operators impersonated Best Buy and mailed similar packages with malicious flash drives via USPS to hotels, restaurants, and retail businesses.
Also Read: MAS Technology Risk Management Guidelines
Reports of such attackers started surfacing back in February 2020. Some of the targets also reported that the hackers emailed or called to pressure them into connecting the drives to their systems.
Beginning with at least May 2020, malicious packages sent by FIN7 also included items such as teddy bears designed to trick the targets’ into lowering their guard.
Attacks like those attempted by FIN7 are known as HID or USB drive-by attacks, and they can only be successful if the victims are willing to or tricked into plugging unknown USB devices into their workstations.
Companies can defend against such attacks by allowing their employees to connect only USB devices based on their hardware ID or if they’re vetted by their security team.