KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







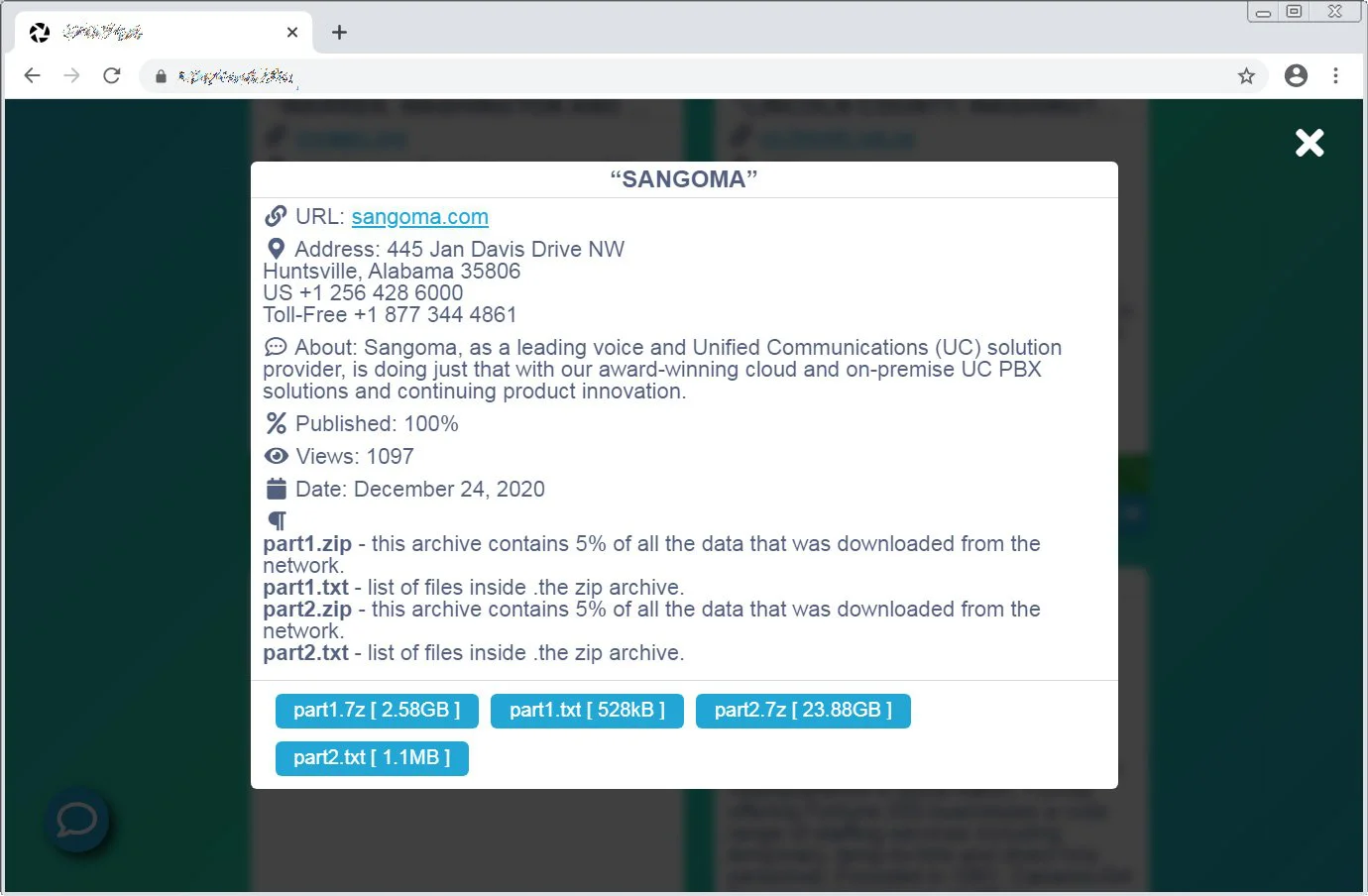
Sangoma disclosed a data breach after files were stolen during a recent Conti ransomware attack and published online.
Sangoma is a voice over IP hardware and software provider known for the popular open-source FreePBX PBX phone system that allows organizations to create cheap corporate phone system on their network.
Yesterday, the Conti ransomware gang published over 26 GB of data on their ransomware data leak site that was stolen from Sangoma during the recent cyberattack. This leaked data includes files related to the company’s accounting, financials, acquisitions, employee benefits and salary, and legal documents.
Also Read: Personal Data Websites: 3 Things That You Must Be Informed
Today, Sangoma confirmed that the ransomware attack resulted in a data breach after private and confidential for their company and employees were published online.
“Sangoma Technologies Corporation (TSXV: STC) (the “Company” or “Sangoma”) announced that, as a result of a ransomware cyber attack on one of the Company’s servers, private and confidential data belonging to the Company was posted online yesterday,” Sangoma disclosed in an advisory.
In attacks against software developers, there is always the concern that their products were modified to deliver malware in supply chain attacks, similar to the recent SolarWinds cyberattack.
In the data breach disclosure, Sangoma is reassuring its customers and users that there is no evidence that customer accounts or Sangoma products were compromised due to this attack.
“There is no initial indication that customer accounts were compromised, nor that any Sangoma products or services were affected as a result of this breach. While the investigation is continuing, and out of an abundance of caution, the company recommends that customers change their Sangoma passwords,” Sangoma stated in the advisory.
The ransomware operation behind this attack is known as Conti, which was first spotted in isolated attacks at the end of December 2019, with attacks picking up in June 2020.
This ransomware shares code with the Ryuk Ransomware and is known to be distributed by the TrickBot trojan.
Conti operators breach corporate networks and spread laterally until they gain access to domain admin credentials to deploy the ransomware payloads used to encrypt devices.
Operating as a private Ransomware-as-a-Service (RaaS) that recruits experienced hackers to deploy the ransomware in exchange for large ransom shares, Conti opened their own data leak site with twenty-six victims in August 2020.
Also Read: PDPA For Companies: Compliance Guide For Singapore Business