KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Recently discovered Gitpaste-12 worm that spreads via GitHub and also hosts malicious payload on Pastebin, has returned with even more exploits.
The first iteration of Gitpaste-12 shipped with reverse shell and crypto-mining capabilities and exploited over 12 known vulnerabilities, therefore the moniker.
This time, the advanced worm and botnet has returned with over 30 vulnerability exploits.
Researchers at Juniper Threat Labs observed the second iteration of Gitpaste-12 on November 10th 2020, present on a different GitHub repository.
Expanding on its predecessor, this new version of Gitpaste-12 comes equipped with over 30 vulnerability exploits, concerning Linux systems, IoT devices, and open-source components.
Initially, the researchers observed the new GitHub repository containing just 3 files.
“The wave of attacks used payloads from yet another GitHub repository, which contained a Linux cryptominer (‘ls’), a list of passwords for brute-force attempts (‘pass’) and a statically linked Python 3.9 interpreter of unknown provenance,” explains Asher Langton, a researcher at Juniper Threat Labs.
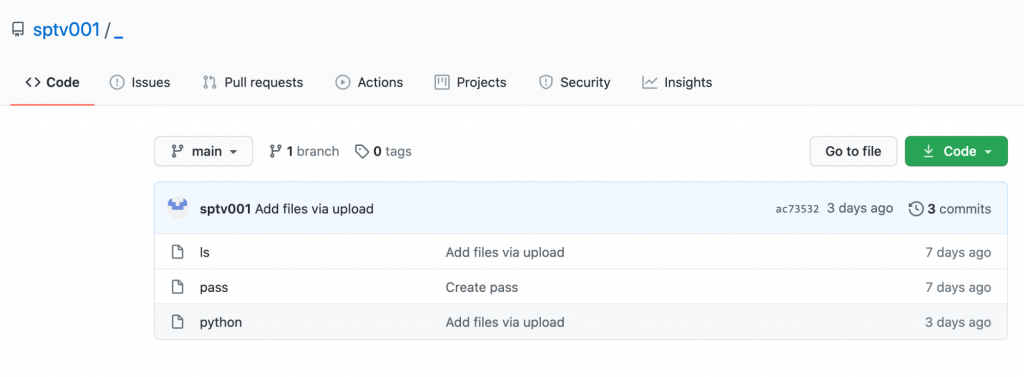
Later, however, two more files were added to the repository by Gitpaste-12 authors at the time of Juniper’s research.
Also Read: 10 Practical Benefits of Managed IT Services
These included, a configuration file (“config.json”) for a Monero cryptominer, and a UPX-packed Linux privilege escalation exploit.
The Monero address contained within the config.json file is the same as that observed in the Gitpaste-12 iteration that came out this October:41qALJpqLhUNCHZTMSMQyf4LQotae9MZnb4u53JzqvHEWyc2i8PEFUCZ4TGL9AGU34ihPU8QGbRzc4FB2nHMsVeMHaYkxus
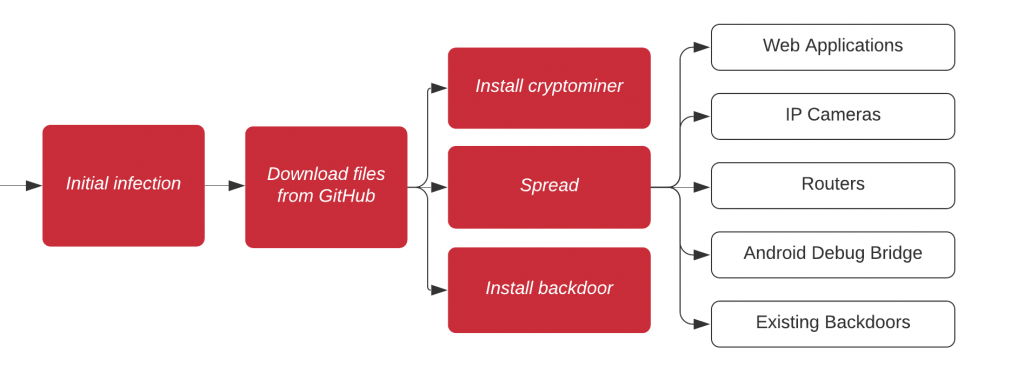
In an illustration shown below, the initial infection begins with Gitpaste-12 sample downloading the payload from GitHub, and dropping a cryptominer, along with a backdoor on the infected host.
The worm further spreads itself to attack web apps, Android Debug Bridge connections, and IoT devices, including IP cameras and routers.
The newer version of Gitpaste-12 has exploits for “at least 31 known vulnerabilities — seven of which were also seen in the previous Gitpaste-12 sample — as well as attempts to compromise open Android Debug Bridge connections and existing malware backdoors,” explains Langton.
The list of exploits, provided by the researchers includes:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-1871
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-3313
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-8361
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17215
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17562
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11511
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10758
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11447
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19509
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5902
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8816
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10987
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-17463
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-17496
https://www.exploit-db.com/exploits/37474
https://www.exploit-db.com/exploits/40500
https://www.exploit-db.com/exploits/45135
https://www.exploit-db.com/exploits/45161
https://www.exploit-db.com/exploits/46542
https://www.exploit-db.com/exploits/48225
https://www.exploit-db.com/exploits/48358
https://www.exploit-db.com/exploits/48676
https://www.exploit-db.com/exploits/48734
https://www.exploit-db.com/exploits/48737
https://www.exploit-db.com/exploits/48743
https://www.exploit-db.com/exploits/48751
https://www.exploit-db.com/exploits/48758
https://www.exploit-db.com/exploits/48771
https://www.exploit-db.com/exploits/48775
https://www.exploit-db.com/exploits/48805
https://www.exploit-db.com/exploits/48827
Some of these vulnerability exploits concern popular open-source applications, such as JBoss Seam 2, CutePHP, mongo-express, Pi-hole, and FuelCMS.
Whereas, well-known proprietary web applications like vBulletin are targeted by the worm.
In addition to exploiting these vulnerabilities, the X10-unix worm bundled within Gitpaste-12 attacks the Android Debug Bridge (adb) application running on port 5555, to upload a malicious native binary (“blu”) and APK to Android devices.
The sophisticated APK, on installation, posts the IP address of the device to Pastebin, and further downloads malicious payload.
This iteration of Gitpaste-12, according to the researchers, has compromised at least 100 distinct hosts.
“While it’s difficult to ascertain the breadth or effectiveness of this malware campaign, in part because Monero — unlike Bitcoin — does not have publicly traceable transactions, [Juniper Threat Labs] can confirm over a hundred distinct hosts have been observed propagating the infection,” stated the researchers.
Also Read: The PDPA Data Breach August 2020: A Recap of 8 Alarming Cases
This evolved version of Gitpaste-12 surfaced not too long after the initial October release.
We are yet to find out if there would be even more advanced versions of this attack coming up in the near future.
The complete research findings and a list of Gitpaste-12 Indicators of Compromise (IOCs) can be found in Juniper Threat Labs’ blog post.