KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Cisco said that unauthenticated attackers could bypass TLS inspection filtering tech in multiple products to exfiltrate data from previously compromised servers inside customers’ networks.
In such attacks, the threat actors can exploit a vulnerability in the Server Name Identification (SNI) request filtering impacting 3000 Series Industrial Security Appliances (ISAs), Firepower Threat Defense (FTD), and Web Security Appliance (WSA) products.
“Using SNIcat or a similar tool, a remote attacker can exfiltrate data in an SSL client hello packet because the return server hello packet from a server on the blocked list is not filtered,” Cisco explained.
“This communication can be used to execute a command-and-control attack on a compromised host or perform additional data exfiltration attacks.”
So far, the Cisco Product Security Incident Response Team (PSIRT) is not aware of attackers or malware exploiting this security flaw in the wild.
Also Read: The Financial Cost of Ransomware Attack
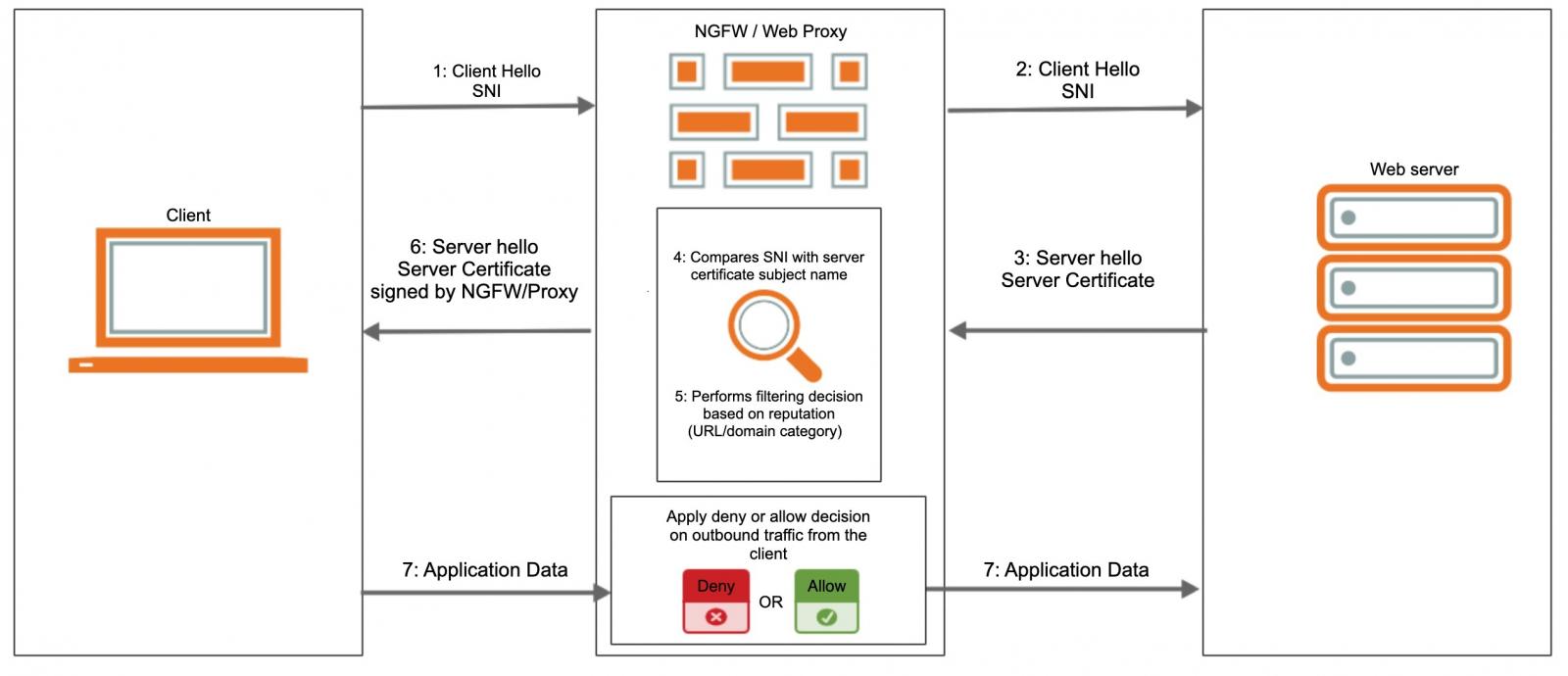
SNIcat (Server Name Indication Concatenator) is a stealthy exfiltration method discovered by mnemonic Labs security researchers that bypasses security perimeter solutions and TLS inspection devices (e.g., web proxies, next-gen firewalls (NGFW) via TLS Client Hello packets.
“By using our exfiltration method SNIcat, we found that we can bypass a security solution performing TLS inspection, even when the Command & Control (C2) domain we use is blocked by common reputation and threat prevention features built into the security solutions themselves,” the reearchers said.
“In short, we found that solutions designed to protect users, introduced them to a new vulnerability.”
Besides Cisco, mnemonic Labs have successfully tested SNIcat against products from F5 Networks (F5 BIG-IP running TMOS 14.1.2, with SSL Orchestrator 5.5.8), Palo Alto Networks (Palo Alto NGFW running PAN-OS 9.1.1), and Fortinet (Fortigate NGFW running FortiOS 6.2.3).
The researchers also developed a proof of concept tool that helps extract data from previously hacked servers via an SNI covert channel, using an agent on the compromised host and a command-and-control server that gathers the exfiltrated data.
“Cisco is investigating its product line to determine which products may be affected by this vulnerability,” Cisco added.
Also Read: Lessons from PDPC Incident and Undertaking: August 2021 Cases
“As the investigation progresses, Cisco will update this advisory with information about affected products.”