KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Threat actors are actively scanning the Internet for open SSH devices and trying to login to them using a new recently patched Zyxel hardcoded credential backdoor.
Last month, Niels Teusink of Dutch cybersecurity firm EYE disclosed a secret hardcoded backdoor account in Zyxel firewalls and AP controllers. This secret ‘zyfwp’ account allowed users to login via SSH and the web interface to gain administrator privileges.
In an advisory, Zyxel states that they used the secret account to deliver firmware updates via FTP automatically.
This backdoor is a significant risk as it could allow threat actors to create VPN accounts to gain access to internal networks or port forward Internal services to make them remotely accessible and exploitable.
Also Read: Data Protection Authority GDPR: Everything You Need To Know
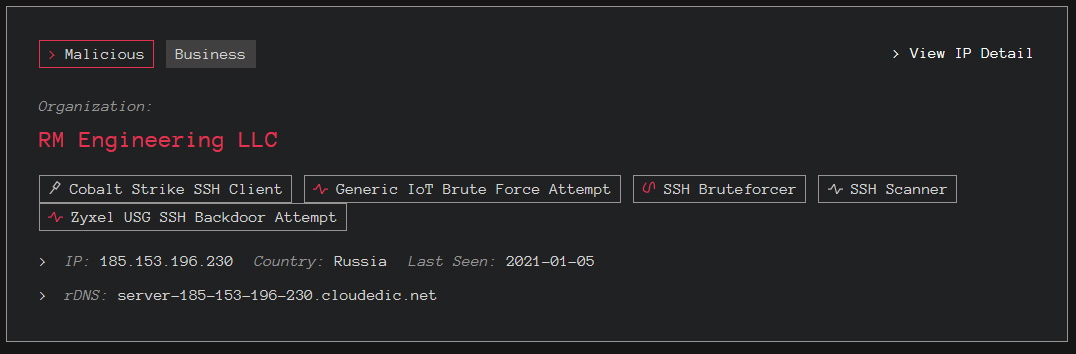
Yesterday, cybersecurity intelligence firm GreyNoise detected three different IP addresses actively scanning for SSH devices and attempting to login to them using the Zyxel backdoor credentials.
GreyNoise CEO Andrew Morris told BleepingComputer that the threat actor does not appear to be scanning specifically for Zyxel devices but is instead scanning the Internet for IP addresses running SSH.
When SSH is detected, it will attempt to brute force an account on the device, with one of the credentials tested being the new Zyxel ‘zyfwp’ backdoor account.
Of particular interest is that one of the IP addresses is using the built-in SSH client of Cobalt Strike to perform the scans. Morris told BleepingComputer that the actor might be scanning this way to evade threat intelligence vendors.
Zyxel released the ‘ZLD V4.60 Patch 1’ last month that removes the backdoor accounts on firewall devices. Zyxel announced yesterday that they would release the patch for AP controllers on January 8th, 2021.
Also Read: The Importance Of Knowing Personal Data Protection Regulations
BleepingComputer strongly recommends that all users install the patch as soon as possible to prevent threat actors from gaining access to vulnerable networks, deploying ransomware, or stealing data.