KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Project Zero, Google’s zero-day bug-hunting team, discovered a group of hackers that used 11 zero-days in attacks targeting Windows, iOS, and Android users within a single year.
The Project Zero team revealed that the hacking group behind these attacks ran two separate campaigns, in February and October 2020.
This month’s report showcases the use of seven zero-days after a previous one published in January showed how four zero-days were used together with n-day exploits to hack potential targets.
Just as before, the attackers used a couple of dozen websites hosting two exploit servers, each of them targeting iOS and Windows or Android users.
“In our testing, both of the exploit servers existed on all of the discovered domains,” Project Zero team member Maddie Stone said.
“After initial fingerprinting (appearing to be based on the origin of the IP address and the user-agent), an iframe was injected into the website pointing to one of the two exploit servers.”
Also Read: Data Protection Officer Singapore | 10 FAQs
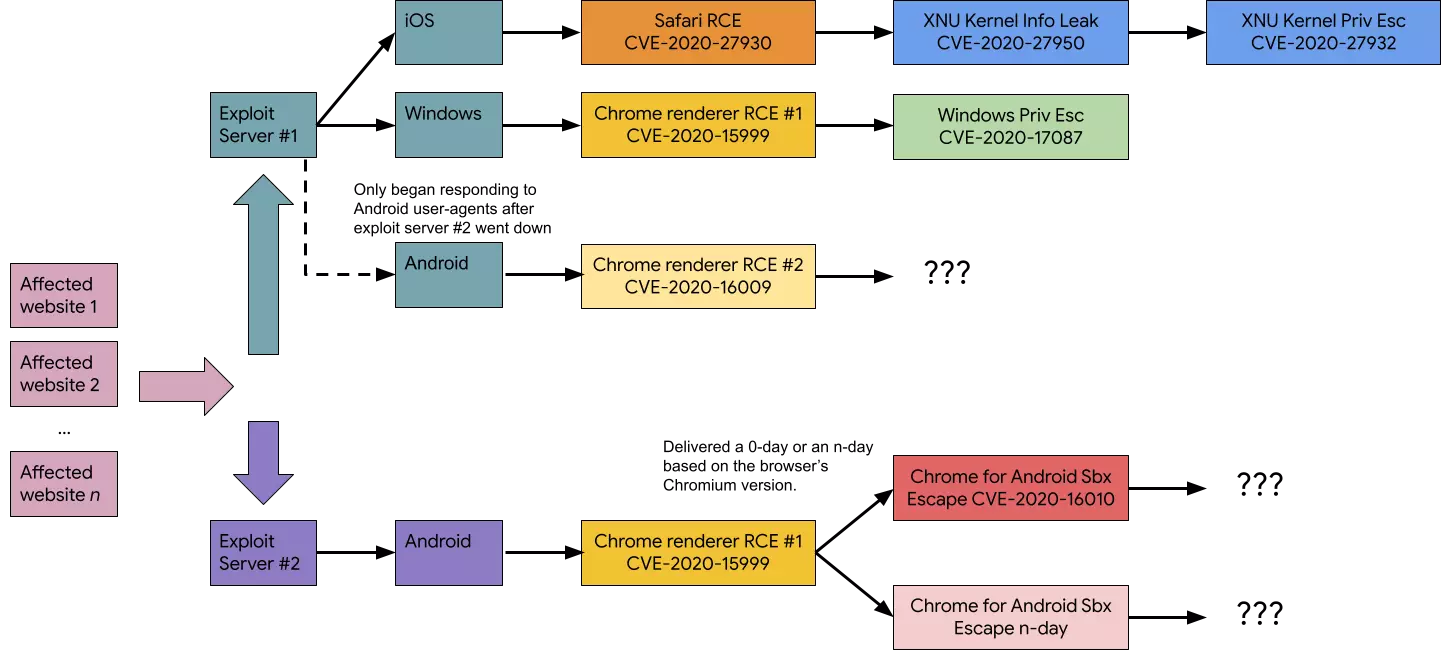
All in all, while analyzing the October 2020 campaign, the Project Zero researchers found:
“When combined with their earlier 2020 operation, the actor used at least 11 0-days in less than a year,” Stone added.
The 11 zero-days used to build the exploit chains during last year attacks include:
Each of the discovered exploits revealed an expert understanding of the vulnerability being exploited and exploit development.
Additionally, in the case of the Chrome Freetype zero-day, the exploitation method used by this hacking group was new to Project Zero.
“Exploitation aside, the modularity of payloads, interchangeable exploitation chains, logging, targeting, and maturity of this actor’s operation set these apart,” Project Zero added.
Also Read: Practitioner Certificate In Personal Data Protection: Everything You Need To Know
“The process to figure out how to trigger the iOS kernel privilege vulnerability would have been non-trivial. The obfuscation methods were varied and time-consuming to figure out.”