KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







This week, a Trustwave security researcher disclosed a privilege escalation flaw in Huawei’s USB LTE dongles.
A USB dongle is a piece of hardware that can be plugged into laptop and desktop computers, much like a thumb drive, to access the internet.
But, while quickly analyzing Huawei’s LTE device drivers, Trustwave researcher discovered a case of improper permissions.
Martin Rakhmanov, Security Research Manager at Trustwave has disclosed his findings on a privilege escalation flaw in Huawei’s USB LTE dongle model E3372.
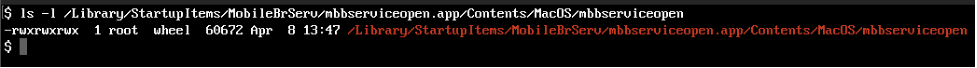
While browsing through the driver files installed by the dongle on his Mac OSX machine, the researcher came across the following file which would auto-run every time the USB dongle was plugged in:/Library/StartupItems/MobileBrServ/mbbserviceopen.app/Contents/MacOS/mbbserviceopen
On plugging in the USB device, this file would open up a web browser with Huawei’s device management interface.
On a closer look, however, Rakhmanov noticed this “mbbserviceopen” file ran with full permissions (777):
And this is problematic.
Also Read: The 5 Phases of Penetration Testing You Should Know
“All a malicious user needs to do is to replace the file with its own code and wait for a legitimate user to start using the cellular data service via Huawei device,” says Rakhmanov.
Privilege escalation attacks rely on a user with limited access to a system being able to obtain a higher level of access, in an illicit manner—such as through a vulnerability exploit, or improper permissions on shared files.
Because this particular vulnerability relies on tampering with the Huawei driver software installed on a computer, local or physical access to the computer is required, making this a case of local privilege escalation.
BleepingComputer reached out to Trustwave to get some insights on the vulnerability:
“The essence of this vulnerability is that one user, even an unprivileged one, can run code as another user on a multiuser system when the dongle is inserted,” Ziv Mador, VP Security Research at Trustwave SpiderLabs told BleepingComputer in an email interview.
Mador further explained that if a laptop using Huawei’s USB device is being used by different employees—for example, one on the day shift, and another on the night shift, the night shift employee can effectively replace the legitimate mbbserviceopen file easily with malware, such as a password stealer.
“With this vulnerability, the night shift manager can write a simple script that will first run a password stealer and then run the original Huawei executable that was used initially.”
“Then each time the manager plugs in the dongle, the password stealer will start, and then internet connectivity will be established.”
“Since the password stealer is invisible, the manager will believe they are having the same user experience – just like any other day – while in practice, the password stealer will be used to steal passwords,” Mador further explained to BleepingComputer.
In other cases, Mador states malware can exploit this vulnerability to cross user boundaries.
Trustwave has issued a security advisory and a blog post detailing the vulnerability.
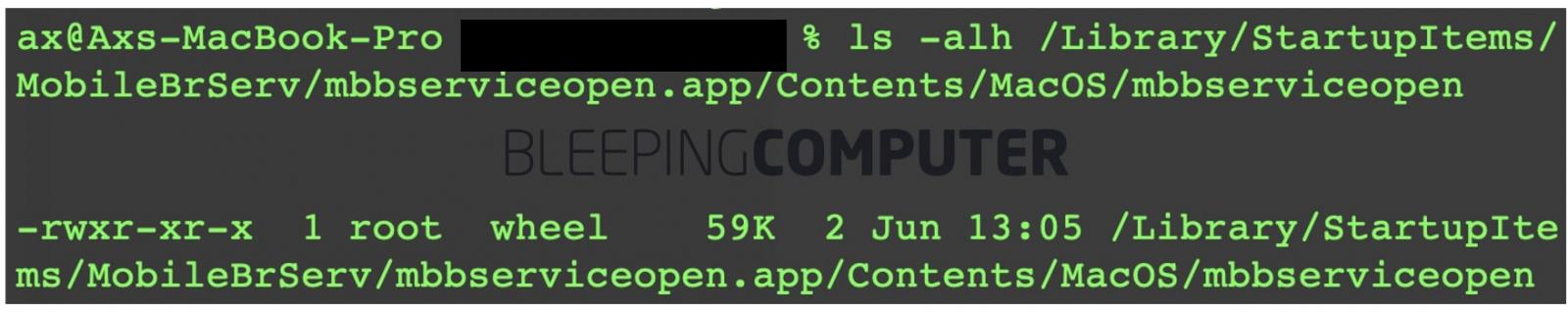
BleepingComputer also observed the driver available from Huawei’s website, did not have this flaw as of today:
Huawei confirmed to BleepingComputer that they had accepted this as a vulnerability and issued an advisory with the remediation instructions.
Also Read: Got Hacked? Here Are 5 Ways to Handle Data Breaches
Huawei has advised users of its USB LTE dongle (E3372) to obtain the “Hi Link” driver files from their website to resolve this vulnerability.
“Customer security is Huawei’s top priority and like all responsible businesses if vulnerabilities are discovered we encourage people to report them to our Product Security Incident Response Team – [email protected],” a Huawei spokesperson told BleepingComputer.
Update: Corrected attribution for one of the quotes.