KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







US department store Kmart has suffered a ransomware attack that impacts back-end services at the company, BleepingComputer has learned.
Sears Holding Corp originally owned both Kmart and Sears, but after the company filed for bankruptcy in 2018, it was purchased by Transform Holdco LLC (Transformco) in 2019.
While Kmart has been a household name in the USA, its number has dwindled over the past two years to only 34 stores remaining.
BleepingComputer has learned that Kmart suffered a cyberattack by the Egregor ransomware operation this week that encrypted devices and servers on the network.
A ransom note shared with BleepingComputer shows that the ‘KMART’ Windows domain was compromised in the attack.
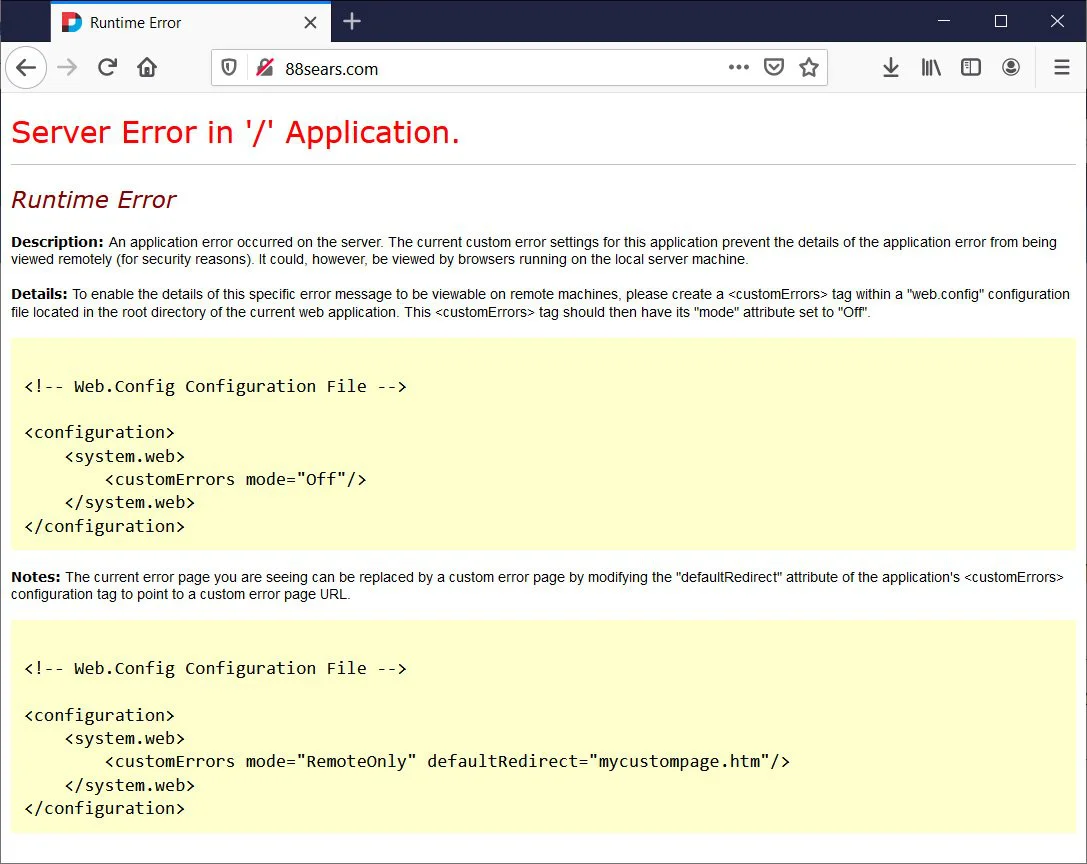
While online stores continue to operate, the ‘Transformco Human Resources Site,’ 88sears.com, is currently offline. Employees said that the outage is caused by the recent ransomware attack.
Also Read: PDPA For Companies: Compliance Guide For Singapore Business
Egregor is known for stealing unencrypted files before deploying their ransomware. The ransomware operation then threatens to post the data on ransomware data leak sites if a ransom is not paid.
It is unknown if the attackers stole data, how many devices were encrypted, or the ransom amount demanded by the Egregor cybercrime group.
Egregor is a new ransomware operation that started encrypting victims in September 2020. BleepingComputer has been told by threat actors that after the Maze Ransomware operation shut down, many of their partners switched over to the Egregor operation.
This migration of experienced threat actors has allowed Egregor to quickly amass many victims in a short period.
Other well-known companies recently attacked by Egregor include Cencosud, Crytek, Ubisoft, and Barnes and Noble.
Also Read: Trusted Data Sharing Framework IMDA Announced In Singapore
BleepingComputer has reached out to Kmart and their parent company Transformco, but has not received a response yet.
This is a developing story.