KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






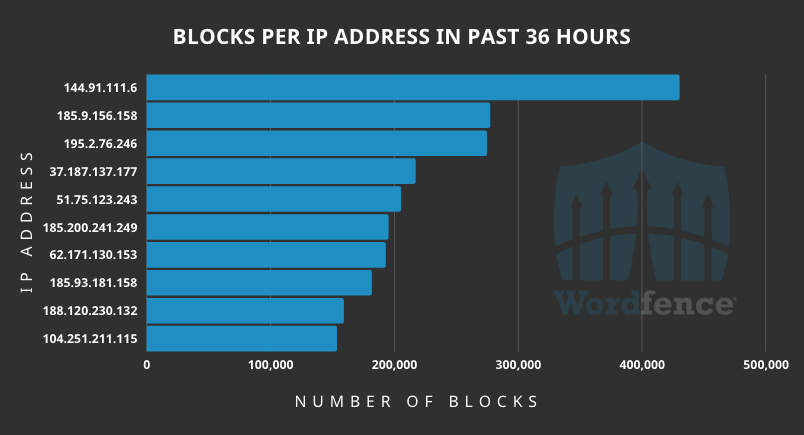
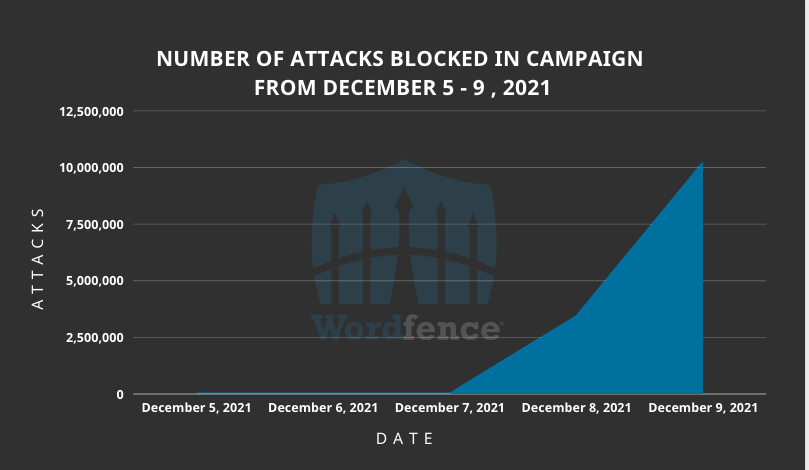
Wordfence analysts report having detected a massive wave of attacks in the last couple of days, originating from 16,000 IPs and targeting over 1.6 million WordPress sites.
The threat actors target four WordPress plugins and fifteen Epsilon Framework themes, one of which has no available patch.
Some of the targeted plugins were patched all the way back in 2018, while others had their vulnerabilities addressed as recently as this week.
Also Read: IT Governance Framework PDF Best Practices And Guidelines
The affected plugins and their versions are:
The targeted Epsilon Framework themes are:
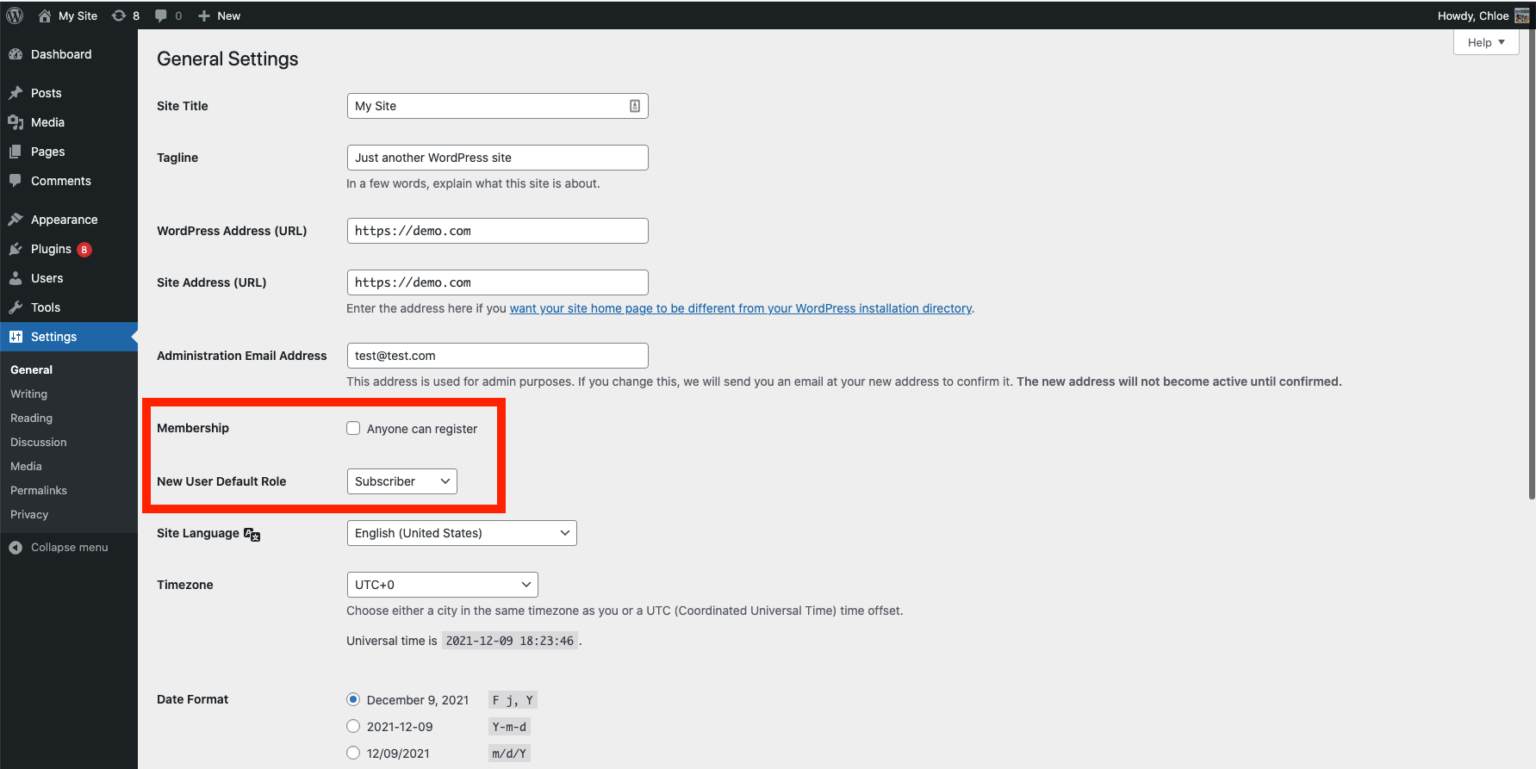
“In most cases, the attackers are updating the users_can_register option to enabled and setting the default_role option to administrator,” Wordfence explains.
“This makes it possible for attackers to register on any site as an administrator effectively taking over the site.”
Also Read: Steps On How To Create Complain About Telemarketing Calls
To check if your site has already been compromised, you can review all user accounts and look for any rogue additions that should be removed immediately.
Next, review the site’s settings at “http://examplesite[.]com/wp-admin/options-general.php” and pay attention to the Membership and the new user default role setting.
It is recommended to update your plugins and themes as soon as possible, even if they’re not in the above list. If you’re using NatureMag Lite, for which there’s no fix, you should uninstall it immediately.
Note that updating the plugins won’t eliminate the threat if your site has already been compromised. In this case, you are advised to follow the instructions found in detailed clean-up guides first.
In general, try to keep the number of plugins at your WordPress site to the absolute minimum necessary as this dramatically reduces the chances of being targeted and hacked in the first place.