KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The Maze ransomware operators have adopted a tactic previously used by the Ragnar Locker gang; to encrypt a computer from within a virtual machine.
In May, we previously reported that Ragnar Locker was seen encrypting files through VirtualBox Windows XP virtual machines to bypass security software on the host.
The virtual machine would mount a host’s drives as remote shares and then run the ransomware in the virtual machine to encrypt the share’s files.
As the virtual machine is not running any security software and is mounting the host’s drives, the host’s security software could not detect the malware and block it.
Also Read: Data Protection Framework: Practical Guidance for Businesses
While performing an incident response for one of their customers, Sophos discovered Maze had attempted to deploy their ransomware twice but were blocked by Sophos’ Intercept X feature.
For the first two attempts, the Maze attacker attempted to launch various ransomware executables using scheduled tasks named ‘Windows Update Security,’ or ‘Windows Update Security Patches,’ or ‘Google Chrome Security Update.’
After the two failed attacks, Sophos’ Peter Mackenzie told BleepingComputer that the Maze threat actors tried a tactic previously used by the Ragnar Locker ransomware.
In their third attack, Maze deployed an MSI file that installed the VirtualBox VM software on the server along with a customized Windows 7 virtual machine.
Once the virtual machine was started, like the previous Ragnar Locker attacks, a batch file called startup_vrun.bat batch file would be executed that preps the machine with the Maze executables.
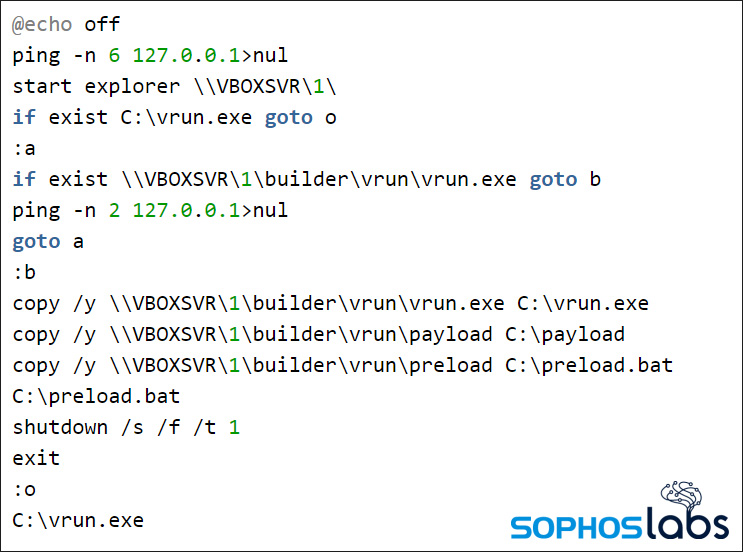
The machine is then shut down, and once restarted again, will launch vrun.exe to encrypt the host’s files.
As the virtual machine is performing the encryption on the host’s mounted drives, security software could not detect the behavior and stop it.
The SophosLabs researchers note that this is an expensive attack method in terms of disk size compared to Ragnar Locker’s previous attacks.
As Ragnar Locker’s VM attack utilized Windows XP, the total footprint was only 404 MB in size. As Maze used Windows 7, the footprint was much larger at a total of 2.6 GB.
This attack illustrates how ransomware operations monitor the tactics of their competitors and adopt them as necessary.
It should also be noted that Ragnar Locker is part of the ‘Maze Cartel,’ so it is possible that Ragnar offered help to Maze in this attack method.
Also Read: MAS Technology Risk Management Guidelines