KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Malware researchers discovered a new threat that they named CDRThief targeting a specific Voice over IP system to steal call data records (CDR) from telephone exchange equipment.
Analysis of the malware revealed that it was specifically created for a particular Linux VoIP platform, namely Linknat VOS2009/3000 softswitches.
A softswitch is a software solution acting as a VoIP server that manages traffic (audio/video/text) in a telecommunication network. It is a central element that ensures a connection between both internal and external lines.
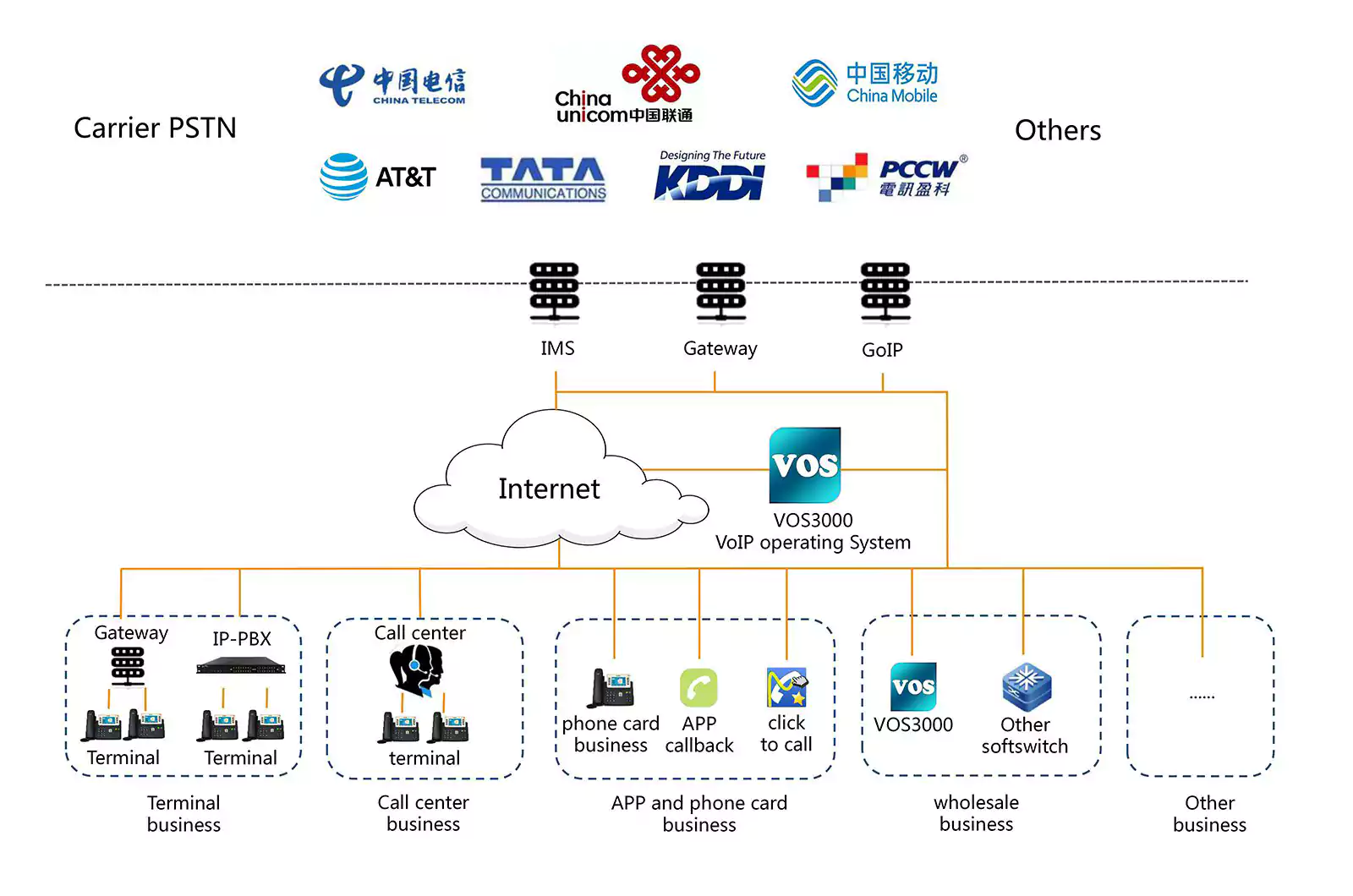
CDRThief’s purpose is to compromise VOS2009/3000 softswitches and steal call metadata from internal MySQL databases, such as IP addresses of the callers, phone numbers, start time and duration of the call, its route, and type.
Also read: How To Anonymised The Data: What Are The Importance Of This?
Analyzing the malware, researchers at ESET found it attempted to obfuscate malicious functionality using the Corrected Block TEA (XXTEA) cipher and then running Base64 encoding on suspicious-looking links.
Although access to the MySQL database is password-protected, the key is encrypted at rest in the configuration file, the CDRThief can read and decrypt it, indicating that whoever developed it knows the attacked platform very well.
ESET believes that the author had to reverse engineer platform binaries to get the details in the Linknat code about the encryption algorithm (AES) and the key that decrypts the database access password.
From the functions of the malware, the researchers determined that CDRThief’s interest is in tables containing logs of system events, information about VoIP gateways, and call metadata.
The malware delivers the information to a command and control (C2) server using JSON over HTTP after compressing and encrypting it with a hardcoded RSA-1024 public key.
“Based on the described functionality, we can say that the malware’s primary focus is on collecting data from the database. Unlike other backdoors, Linux/CDRThief does not have support for shell command execution or exfiltrating specific files from the compromised softswitch’s disk. However, these functions could be introduced in an updated version” – ESET
The analysis revealed that CDRThief can start from any location on the disk, using any file name. Once deployed, it tries to start a legitimate binary from the Linknat VOS2009/3000 platform:
exec -a '/home/kunshi/callservice/bin/callservice -r
/home/kunshi/.run/callservice.pid'It is unclear how persistence is achieved, but researchers say that the command above suggests that the malware might be inserted into the boot chain of the platform, possibly masquerading as a Linknat softswitch component.
Based on current observations from the analysis, CDRThief may be used for cyber espionage operations or VoIP fraud.
Also read: 10 Government Data Leaks In Singapore: Prevent Cybersecurity