KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A recently discovered cryptomining botnet is actively scanning for vulnerable Windows and Linux enterprise servers and infecting them with Monero (XMRig) miner and self-spreader malware payloads.
First spotted by Alibaba Cloud (Aliyun) security researchers in February (who dubbed it Sysrv-hello) and active since December 2020,the botnet has also landed on the radars of researchers at Lacework Labs and Juniper Threat Labs after a surge of activity during March.
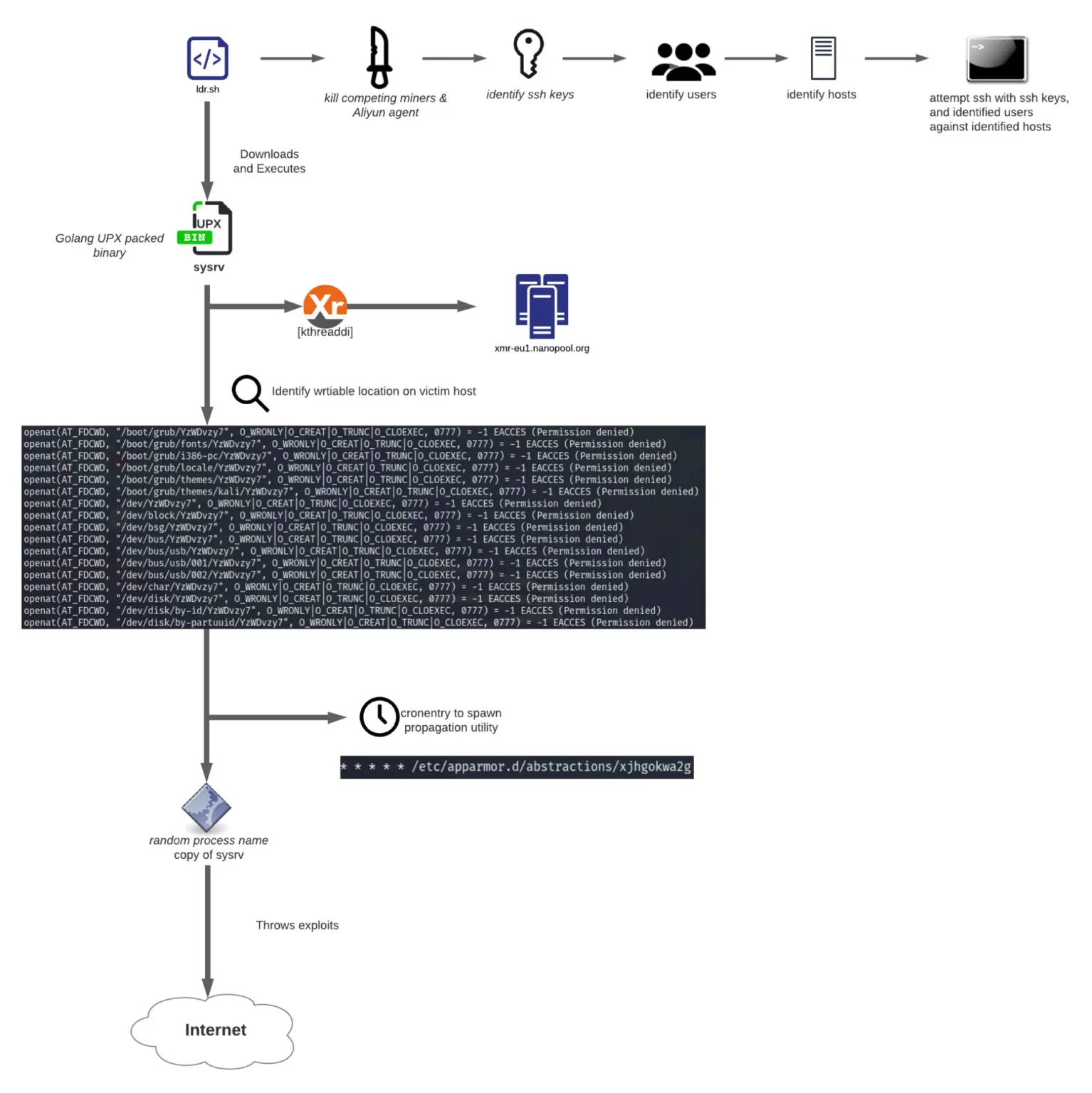
While, at first, it was using a multi-component architecture with the miner and worm (propagator) modules, the botnet has been upgraded to use a single binary capable of mining and auto-spreading the malware to other devices.
Sysrv-hello’s propagator component aggressively scans the Internet for more vulnerable systems to add to its army of Monero mining bots with exploits targeting vulnerabilities that allow it to execute malicious code remotely.
The attackers “are targeting cloud workloads through remote code injection/remote code execution vulnerabilities in PHPUnit, Apache Solar, Confluence, Laravel, JBoss, Jira, Sonatype, Oracle WebLogic and Apache Struts to gain initial access,” Lacework found.
After hacking into a server and killing competing cryptocurrency miners, the malware will also spread over the network in brute force attacks using SSH private keys collected from various locations on infected servers
“Lateral movement is conducted via SSH keys available on the victim machine and hosts identified from bash history files, ssh config files, and known_hosts files,” Lacework added.
Also Read: The DNC Singapore: Looking At 2 Sides Better
After the botnet’s activity surged in March, Juniper identified six vulnerabilities exploited by malware samples collected in active attacks:
Other exploits used by the botnet in the past also include:
The Lacework Labs team successfully recovered a Sysrv-hello XMrig mining configuration file which helped them find one of the Monero wallets used by the botnet to collect Monero mined on the F2Pool mining pool.
The latest samples spotted in the wild have also added support for the Nanopool mining pool after removing support for MineXMR.
Even though this wallet contains just over 12 XMR (roughly $4,000), cryptomining botnets regularly use more than one wallet linked to multiple mining pools to collect illegally earned cryptocurrency, and this can quickly add up to a small fortune.
For instance, another wallet connected to Nanopool and spotted by Juniper researchers contains 8 XMR (almost $1,700 worth of Monero) collected between March 1 and March 28.
Sysrv-hello is not alone trawling the Internet for free computing power, as other botnets are also actively trying to cash in from exploiting and enslaving vulnerable servers to mine for Monero cryptocurrency.
Also Read: 4 Best Practices On How To Use SkillsFuture Credit
360 Netlab researchers spotted an increasingly active and upgraded version of the z0Miner cryptomining botnet attempting to infect vulnerable Jenkins and ElasticSearch servers to mine for Monero.
Cybereason’s Nocturnus incident response team published findings on the Prometei botnet on Thursday, first spotted last year and active since at least 2016, now deploying Monero miners on unpatched Microsoft Exchange servers.