KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new DeadBolt ransomware group is encrypting QNAP NAS devices worldwide using what they claim is a zero-day vulnerability in the device’s software.
The attacks started today, January 25th, with QNAP devices suddenly finding their files encrypted and file names appended with a .deadbolt file extension.
Instead of creating ransom notes in each folder on the device, the QNAP device’s login page is hijacked to display a screen stating, “WARNING: Your files have been locked by DeadBolt,” as shown in the image below.
Also Read: The PDPA Data Breach August 2020: A Recap of 8 Alarming Cases
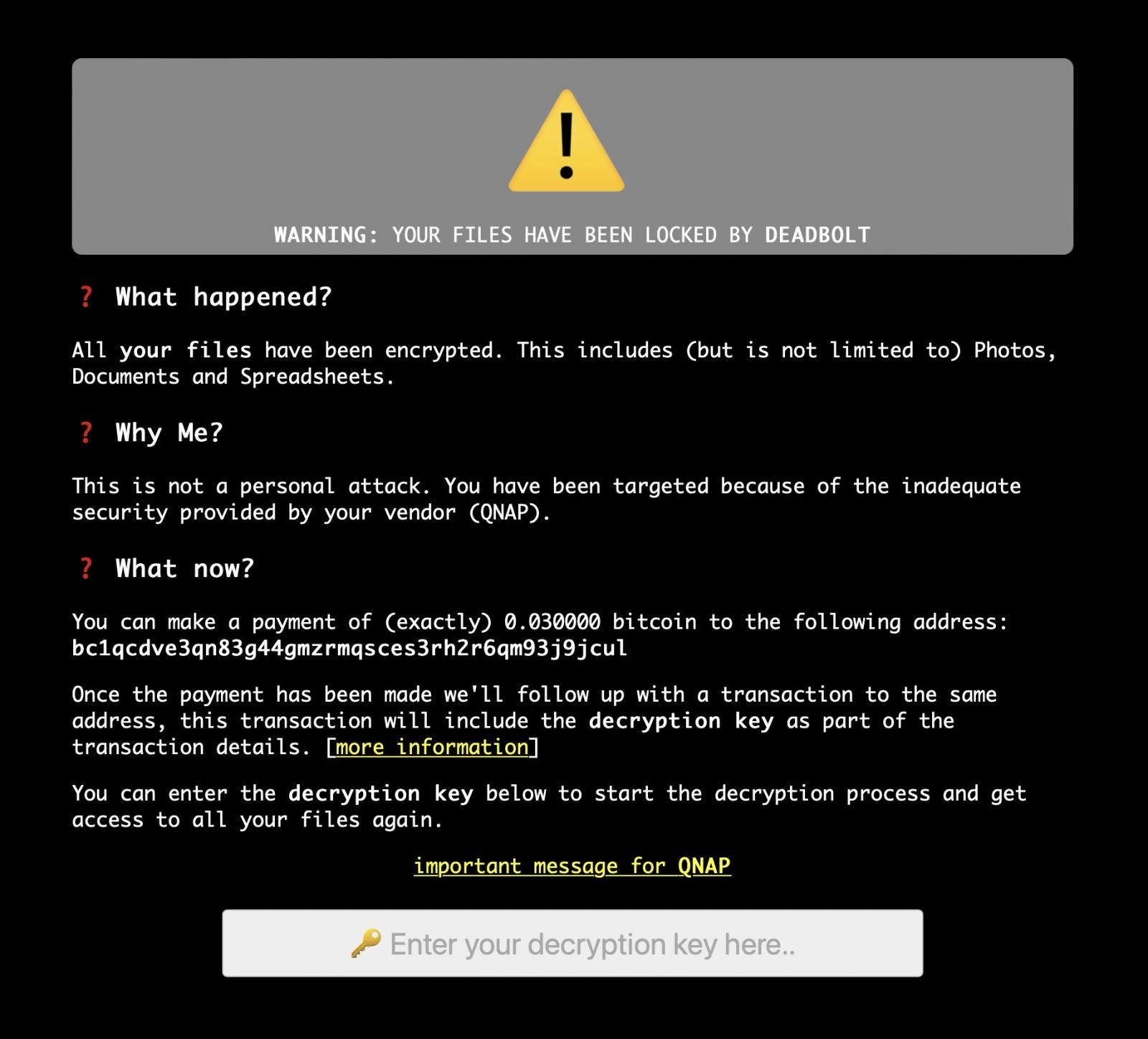
This screen informs the victim that they should pay 0.03 bitcoins (approximately $1,100) to an enclosed Bitcoin address unique to each victim.
After payment is made, the threat actors claim they will make a follow-up transaction to the same address that includes the decryption key, which can be retrieved using the following instructions.
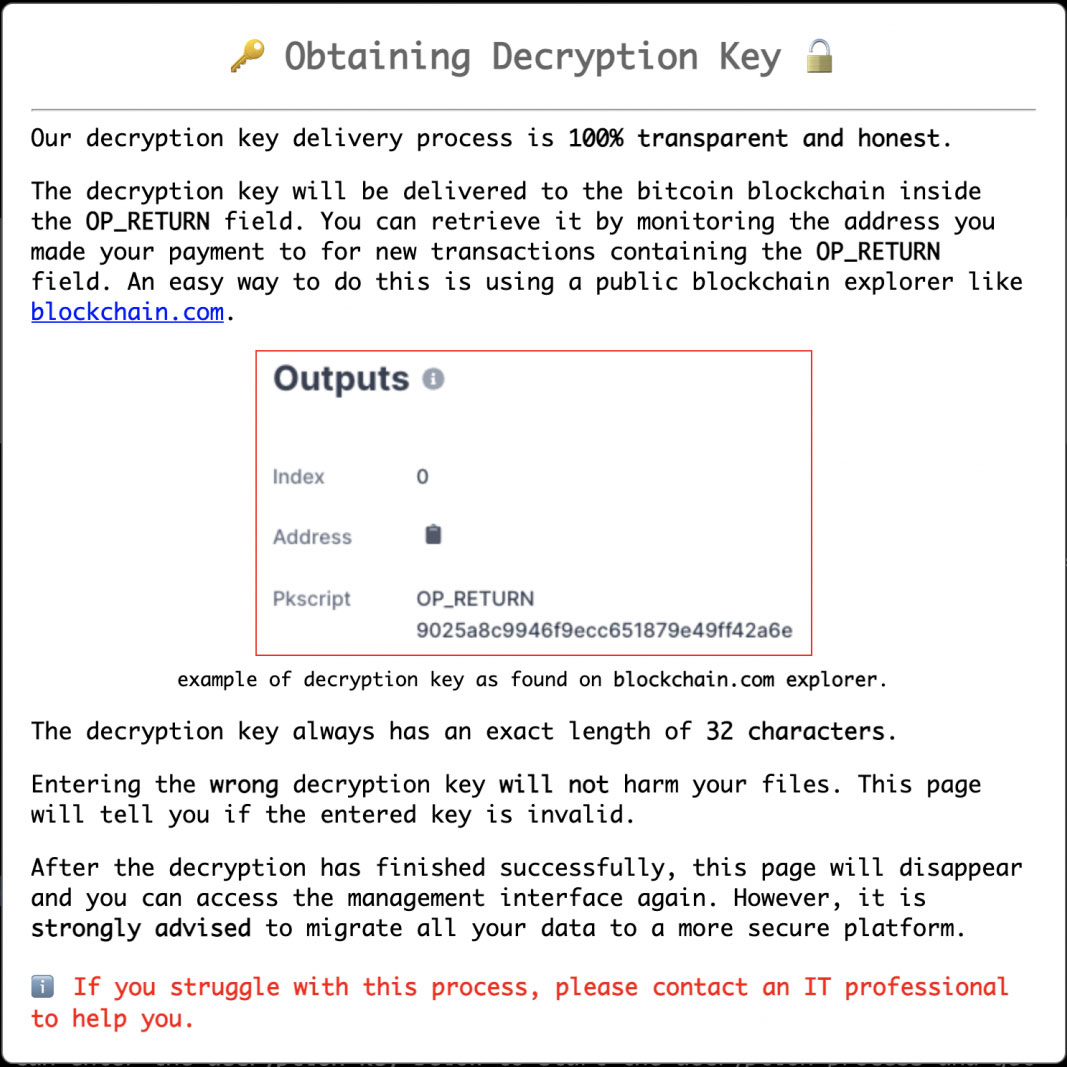
This decryption key can then be entered into the screen to decrypt the device’s files. At this time, there is no confirmation that paying a ransom will result in receiving a decryption key or that users will be able to decrypt files.
QNAP has told BleepingComputer that users can bypass the ransom screen and gain access to their admin page by using the http://nas_ip:8080/cgi-bin/index.cgi or https://nas_ip/cgi-bin/index.cgi URLs.
BleepingComputer is aware of at least fifteen victims of the new DeadBolt ransomware attack, with no specific region being targeted.
As with all ransomware attacks against QNAP devices, the DeadBolt attacks only affect devices accessible to the Internet.
As the threat actors claim the attack is conducted through a zero-day vulnerability, it is strongly advised that all QNAP users disconnect their devices from the Internet and place them behind a firewall.
QNAP further told us that their Product Security Incident Response Team (PSIRT) is investigating the attack vectors now and that owners should follow these steps to protect their data and NAS.
With QNAP owners being targeted by ongoing attacks from two other ransomware families known as Qlocker and eCh0raix, all owners should follow these steps to prevent future attacks.
BleepingComputer has created a DeadBolt ransomware support topic that can be used to discuss the attacks and potentially receive help from other QNAP owners.
Also Read: How Long Do Employers Keep Employee Records After Termination? 1 Hard Question
On the main ransom note screen, there is a link titled “important message for QNAP,” that when clicked, will display a message from the DeadBolt gang specifically for QNAP.
On this screen, the DeadBolt ransomware gang is offering the full details of the alleged zero-day vulnerability if QNAP pays them 5 Bitcoins worth $184,000.
They are also willing to sell QNAP the master decryption key that can decrypt the files for all affected victims and the zero-day info for 50 bitcoins, or approximately $1.85 million.
“Make a bitcoin payment of 50 BTC to bc1qnju697uc83w5u3ykw7luujzupfyf82t6trlnd8,” the threat actors wrote in a message to QNAP.
“You will receive a universal decryption master key (and instructions) that can be used to unlock all your clients their files. Additionally, we will also send you all details about the zero-day vulnerability to [email protected].”
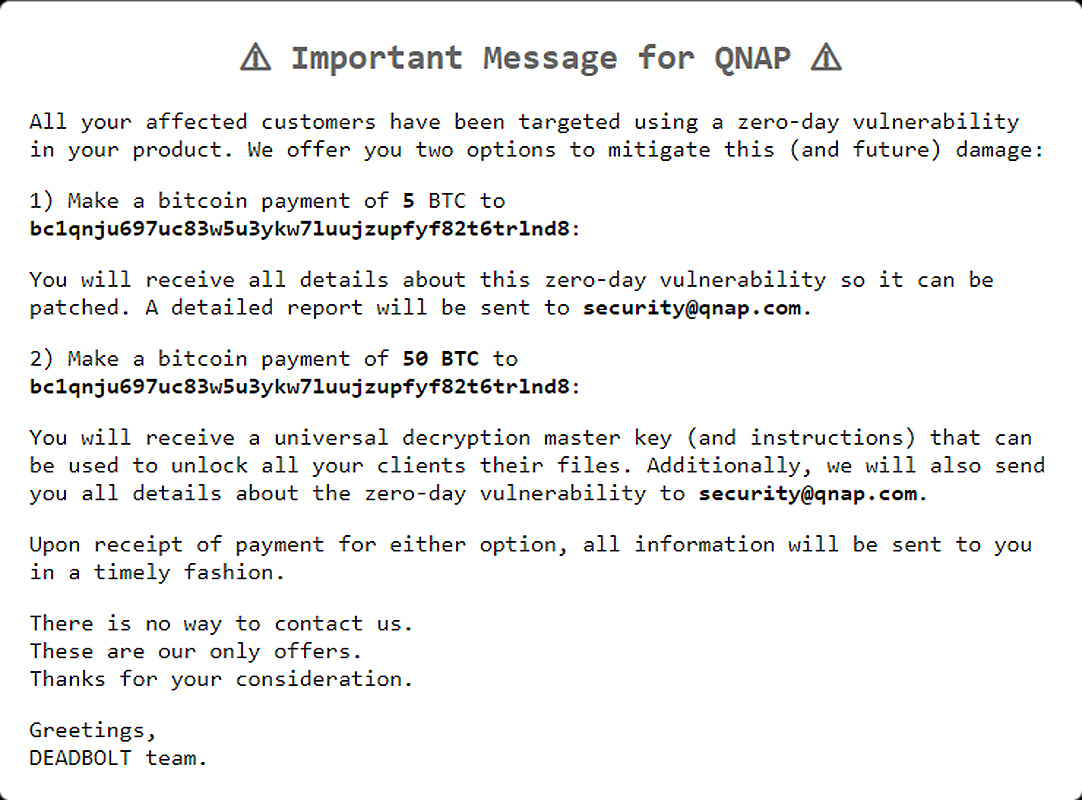
The ransomware gang further states that there is no way to contact them other than through Bitcoin payments.
This method of communication is a very different approach than other ransomware attacks that usually provide some form of communication, whether through a dedicated Tor website, email, or messaging platforms.
BleepingComputer has contacted QNAP with questions about the DeadBolt attacks and will update the story with their response
Update: Added further information on how the decryption key will be retrieved.
Update 1/26/22: Added further information from QNAP