KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new phishing campaign impersonating the United States Department of Labor asks recipients to submit bids to steal Office 365 credentials.
The phishing campaign has been ongoing for at least a couple of months and utilizes over ten different phishing sites impersonating the government agency.
In a new report by email security firm INKY, who shared the report with Bleeping Computer before publication, researchers illustrated how the phishing attack is used to steal credentials.
Also Read: 6 ways to recognize a potential phishing scam and what to do if you receive one
The emails are sent from spoofed domains that look as if they came from the actual Department of Labor (DoL) site, while some are based on a set of newly created look-alike domains such as:
Most of the emails pass through abused servers owned by non-profit organizations to evade email security blocks.
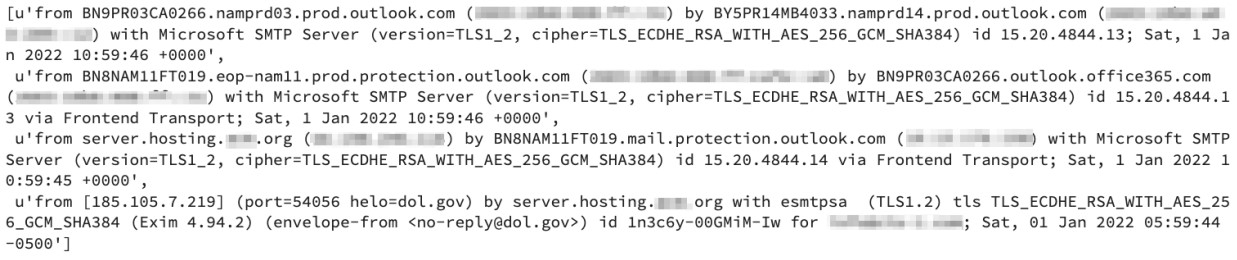
In other cases, they are sent through newly registered and unreported domains that aren’t yet included on anti-phishing lists.
The sender pretends to be a senior DoL employee who invites the recipient to submit their bid for an ongoing government project.
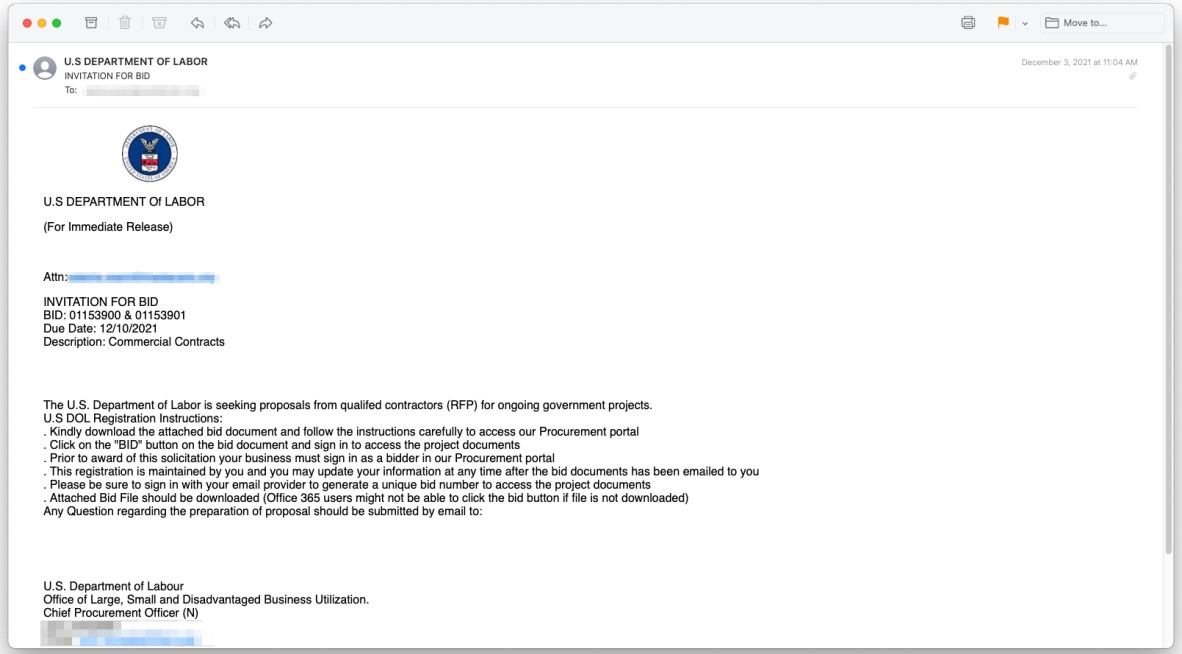
The emails contain a valid letterhead, professionally-arranged content, and a three-page PDF attachment of a seemingly legitimate form.
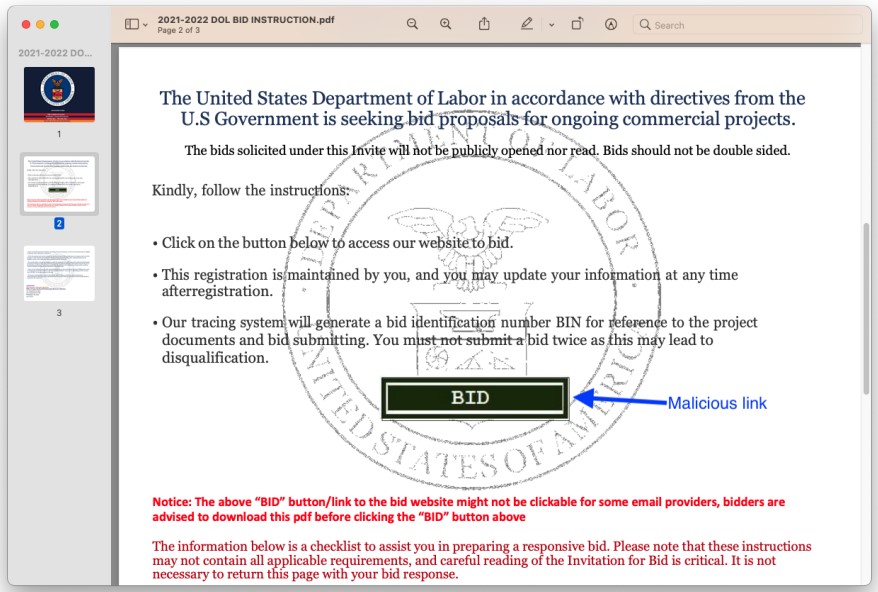
The PDF contains a “BID” button, which, if clicked, takes the victim to one of the phishing sites. INKY has confirmed the following landing pages as part of this campaign:
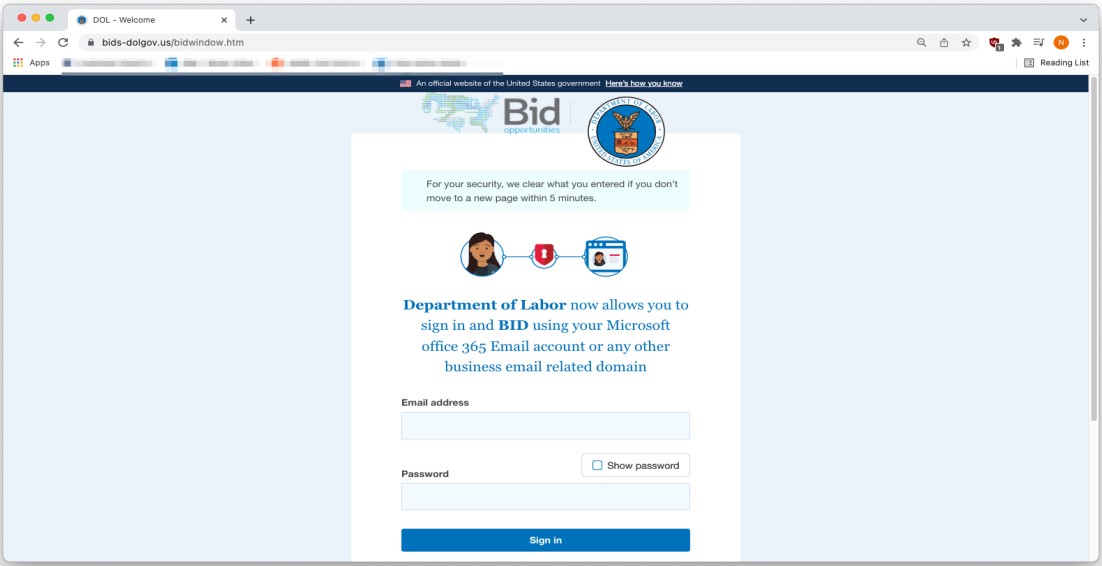
The spoofed site looks convincing, containing identical HTML and CSS to the real one. The threat actors have even included an instructions pop-up message to direct victims through the bidding (phishing) process.
Also Read: How does ransomware happen? Here are 7 ways to prevent them
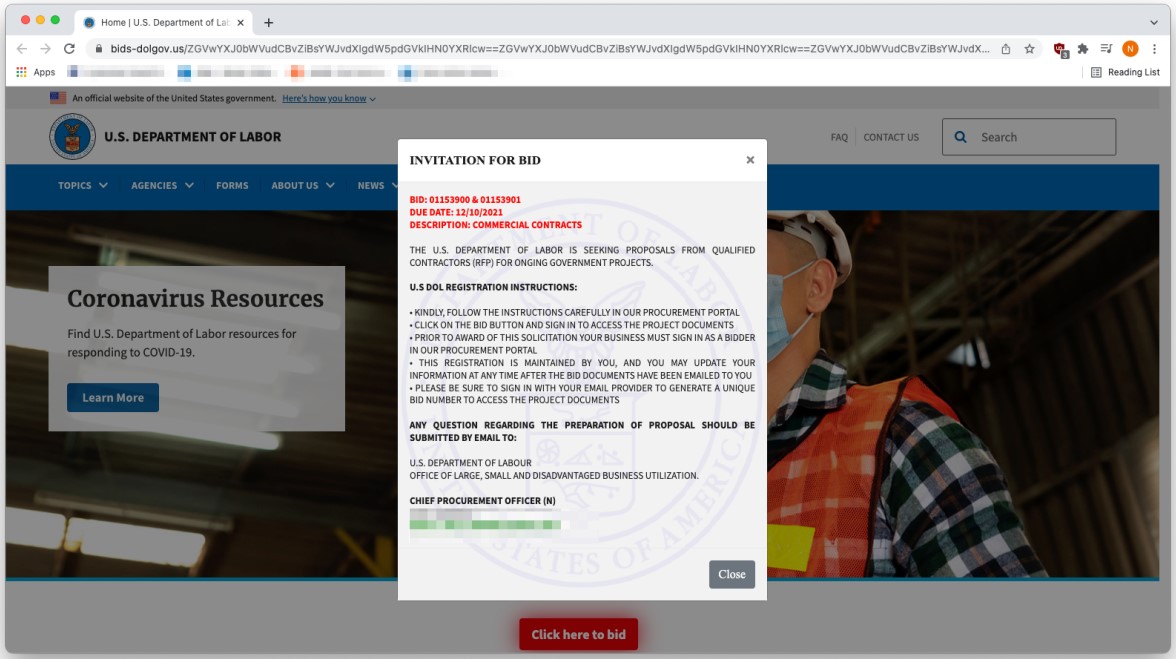
Those who bid for a project will be taken to a credential harvesting form that targets their Microsoft Office 365 email address and password.
No matter what’s inputted there, the website returns a bogus error to trick the victim into entering them again, thus reducing the chances of stealing mistyped credentials.
If the victim falls for the trap for a second time, they are eventually re-directed to the actual DoL site, left with little evidence as to what exactly has happened.
This campaign’s level of sophistication and diligence in setting up convincing web pages and writing error-free phishing emails is worrying.
We saw something similar in December 2021, with phishing actors impersonating Pfizer and using well-crafted PDF attachments to invite recipients to submit bids to the pharmaceutical company.
In this case, the actors take things one step further by abusing legitimate mail servers to send their phishing lures.
Unfortunately, all that leaves email recipients with is very subtle evidence of the trickery targeting them, so ultimate vigilance is advised.
In this case, the most obvious sign of the scam would be the Department of Labor requiring anyone to log in with Office 365 credentials to view a document, something that isn’t the case on any U.S. government website.