KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Threat actors are conducting a highly targeted phishing campaign impersonating Pfizer to steal business and financial information from victims.
Pfizer is a well-known pharmaceutical company that enjoys extensive publicity for producing one of the few mRNA vaccines currently available against COVID-19.
Phishing actors aim to exploit brand names that are widely known, as their chances of success increase dramatically compared to impersonating a fictional entity.
In a new report by INKY, researchers explain that threat actors are impersonating Phizer in a phishing email campaign that started around August 15, 2021.
The actors behind this campaign are diligent in their phishing operations, combining “clean” PDF attachments with newly registered domains that appear as official Pfizer online spaces.
Then, they spawn email accounts from these domains for phishing email distribution to bypass email protection solutions.
Also Read: PDPC: New guidance on personal data protection practices
The domains were registered through Namecheap, which accepts cryptocurrency as a payment method, allowing the actors to remain anonymous.
Some of the examples seen by INKY are:
The first one, pfizer-nl[.]com, may trick someone into believing it’s the official online portal of Pfizer Netherlands, a country where the company does have an office.
The subject lines typically involve urgent quotations, invitations to bid, and industrial equipment supply-related topics, as shown below.
Because of the galloping spread of new COVID-19 variants, phishing actors don’t have much difficulty encapsulating a sense of urgency in these emails.
In most of the 400 examples seen by INKY analysts, the actors use a professionally-looking three-page PDF document discussing due dates, payment terms, and other details that constitute a legitimate request for quotation.
The PDF isn’t laced with malware-dropping links or phishing URLs that would raise flags on email security tools and doesn’t contain any typos that would make the fraud obvious.
Also Read: PDPA compliance for Singapore schools
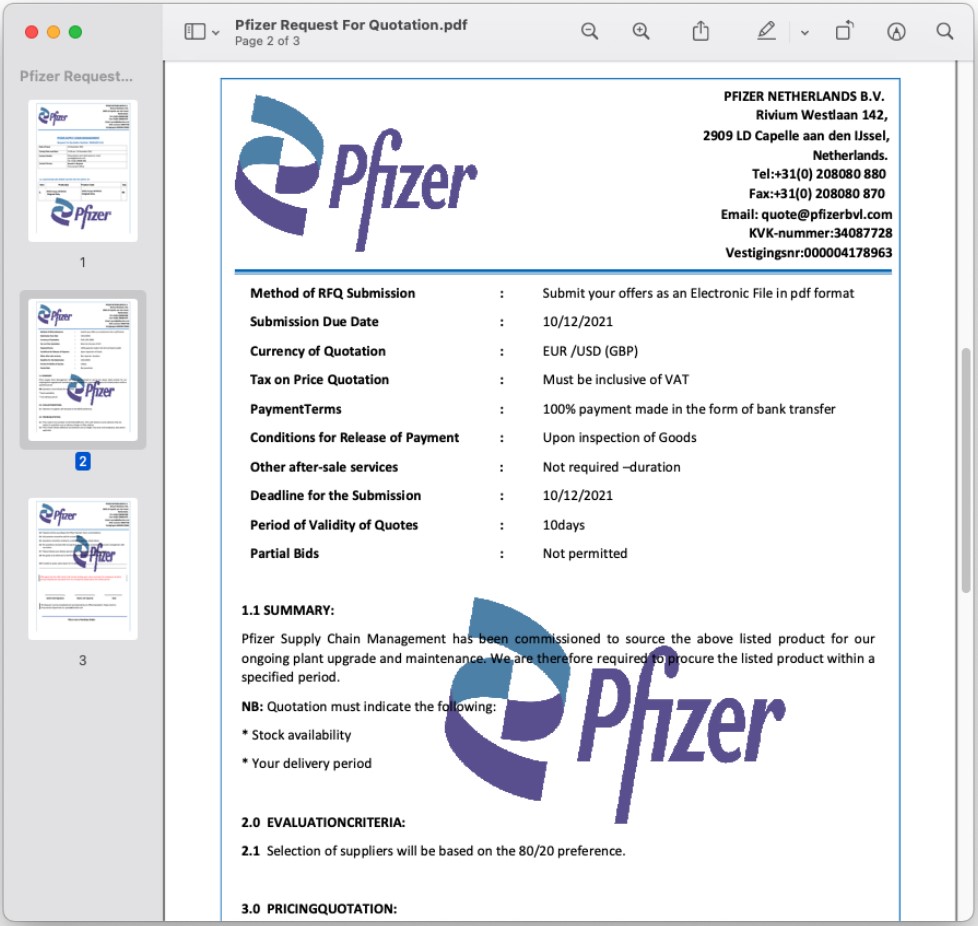
However, the recipients are requested to send their quotes to the impersonated Pfizer domain addresses, such as quote@pfizerbvl[.]com or quotation@pfizersupplychain[.]com.
While the exact goal of the campaign isn’t clear, the fact that payment terms are included in the PDF is an indication that the threat actors will request the recipient to share their banking details at some point.
If payment information is provided, it could be used by the attackers in future BEC campaigns used against the targeted company’s customers.
Also, the actors don’t request personal details on first contact, which helps the recipients lower their shields.
Responding to these emails only pushes the victim deeper into the deception, as they are then hoping to sign a lucrative deal with a prestigious firm.
When receiving emails with unusual bidding requests, it is always safer to contact the company on their regular number and ask to speak to the person.
If the person does not work at the firm or is unaware of these emails, you can ignore the requests and delete the emails.