KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Europol has announced the arrest of 12 individuals believed to be linked to ransomware attacks against 1,800 victims in 71 countries.According to the law enforcement report, the actors have deployed ransomware strains such as LockerGoga, MegaCortex, and Dharma, as well as malware like Trickbot and post-exploitation tools like Cobalt Strike.LockerGoga first appeared in the wild in January 2019, when it hit ‘Altran Technologies’, a French engineering and R&D consultant, part of the Capgemini group.
LockerGoga and MegaCortex infections culminated during that year, with a report from the National Cyber Security Centre (NCSC) in the Netherlands attributing 1,800 infections to Ryuk and the two strains.
The most notable case linked to the suspects is a 2019 attack against Norsk Hydro, the Norwegian aluminum production giant, causing severe and lengthy disruption in the company’s operations.
Also Read: Ways to protect HR data and avoid penalties for data breaches
Today, the Norwegian police posted a relevant announcement saying that they never stopped hunting for the threat actors, working with foreign counterparts to bring them down.
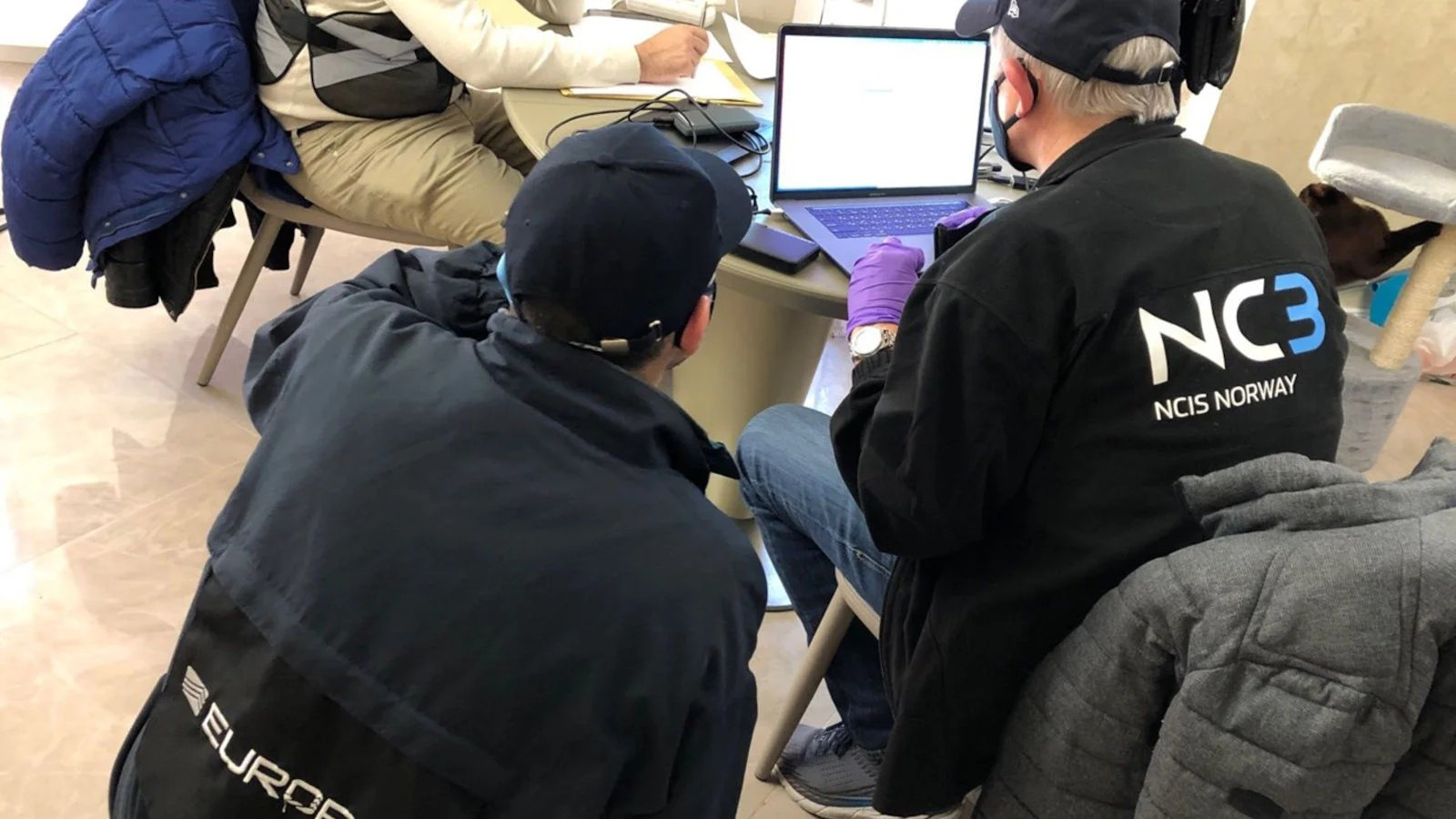
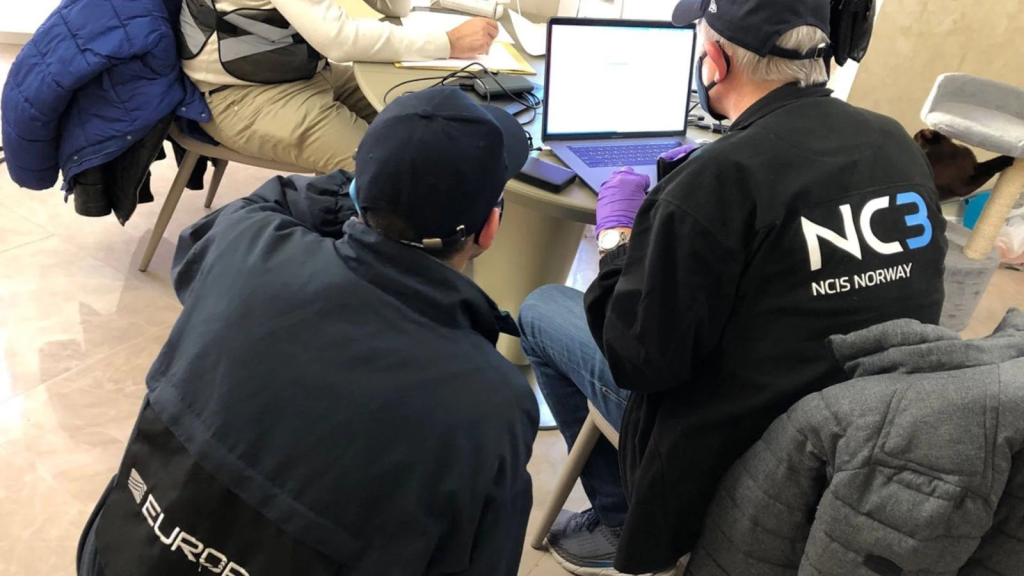
The arrests took place in Ukraine and Switzerland on October 26, 2021, and as a result of the simultaneous raids, the police seized five luxury vehicles, electronic devices, and $52,000 in cash.
As Europol explains, the arrested individuals are considered high-value targets in the sense that they’re thought to have spearheaded multiple high-profile ransomware cases.
As such, the forensic examination and the interrogations that follow the action will be extensive and may very likely bring up new investigative leads.
The cyber-criminals fulfilled specialized roles in a highly organized criminal organization, with each person being responsible for distinct operational aspects.
Some engaged in network penetration, others in brute force attacks, while others performed SQL injections or handled credential phishing operations.
In the post-infection stage, their roles were transposed to a new domain, with the actors deploying malware, network reconnaissance, and lateral movement tools, carefully stealing data while staying undetected.
Also Read: Data Protection Act of Singapore: Validity in the Post-pandemic World
Eventually, the actors encrypted the compromised systems and left ransom notes demanding the victims to pay exorbitant amounts of money in Bitcoin in exchange for decryption keys.
Some of the individuals who were arrested now are thought to be in charge of the money laundering operation, using Bitcoin mixing services to obscure the money trace.
This operation is a massive law-enforcement success, made possible thanks to more than 50 investigators from seven European police departments, six Europol specialists, and members of the FBI and the US Secret Service.