KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Trend Micro antivirus has fixed a false positive affecting its Apex One endpoint security solution that caused Microsoft Edge updates to be tagged as malware and the Windows registry to be incorrectly modified.
According to hundreds of customer reports that started streaming in earlier this week on the company’s forum and on social networks, the false positive affected update packages stored in the Microsoft Edge installation folder.
As users further revealed, the Trend Micro Apex One flagged the browser updates as Virus/Malware: TROJ_FRS.VSNTE222 and Virus/Malware: TSC_GENCLEAN.
The cybersecurity software maker addressed the issue and published an advisory urging customers to update their products and ensure that the Smart Scan Agent Pattern and Smart Scan Pattern are updated to the latest version.
“Trend Micro is aware of a detection issue that was reported earlier today regarding a potential false positive with Microsoft Edge and a Trend Micro Smart Scan pattern,” the company said.
Also Read: How To Check Data Breach And How Can We Prevent It
“The pattern has been updated to remove the detection in question and we are doing an investigation on the root cause of the issue. More information can be provided after the investigation is complete.
“Please confirm that both the Smart Scan Agent Pattern is 17.541.00 or later AND Smart Scan Pattern is 21474.139.09 or later which resolves the issue.”
Trend Micro also shared a temporary workaround if the pattern update didn’t fix the issue which requires adding multiple Microsoft Edge folders to Apex One’s exclusion list.
While the fix provided by Trend Micro for the false positive can easily be applied by updating Apex One, some customers also reported that this issue also led to Windows registry entries being altered after the agent’s Damage Cleanup tool was executed.
“It was reported that some customers observed some registry changes as a result of the detection depending on their endpoint cleaning configuration settings,” Trend Micro added.
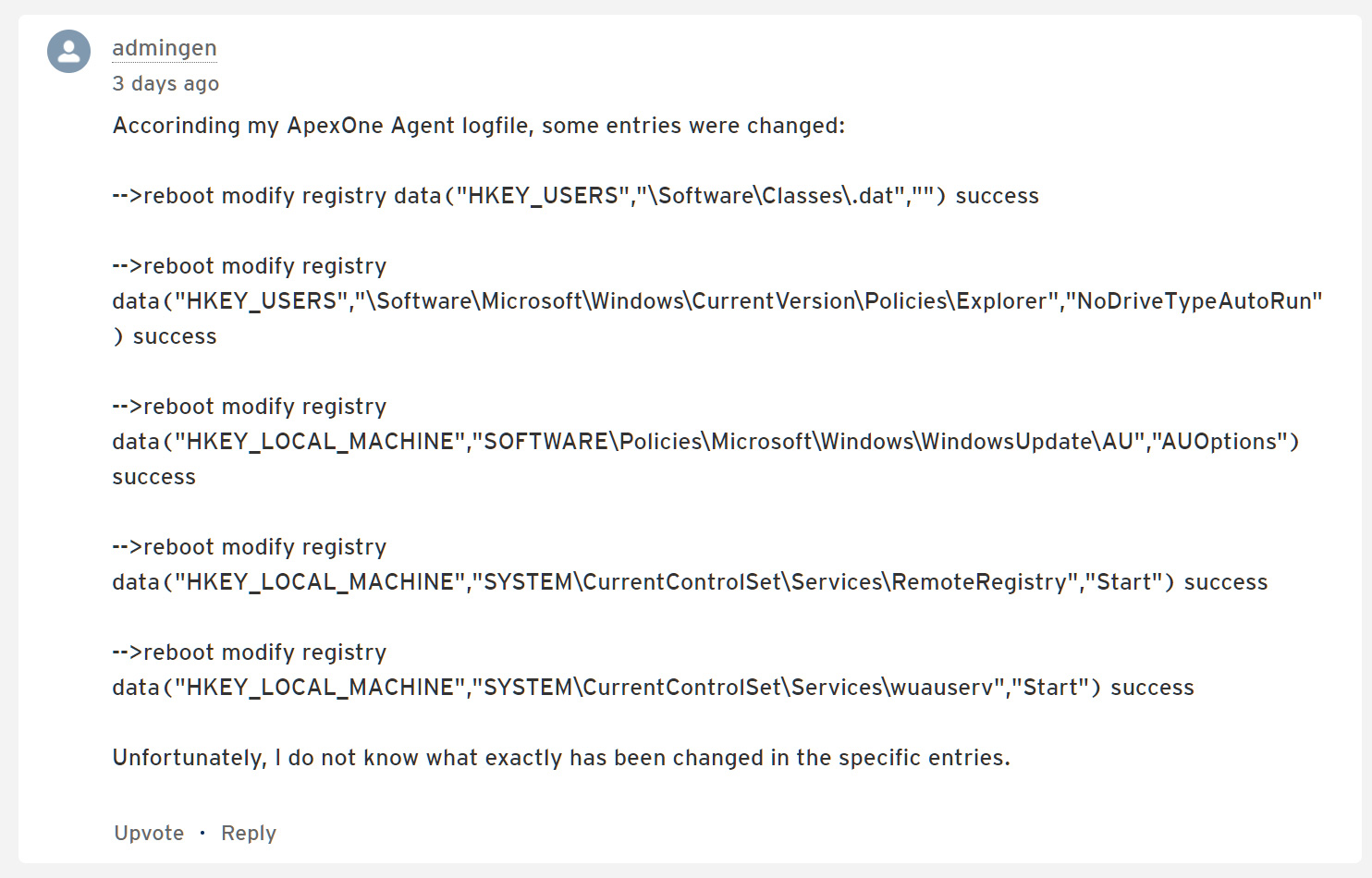
This requires affected users to restore backups made by the Apex One agent through a procedure that will help revert the changes made by Damage Cleanup.
Also Read: Top 8 Main PDPA Obligations To Boost And Secure Your Business
The company also shared a script that would help system admins to automate the registry restoration procedure with the help of group policies or other enterprise scripting tools.
However, you should first test this automation tool before running it across the entire environment.
“Please note that administrators looking to utilize this script as a batch file or via other method should first carefully review the script and test in their environment before any widespread development,” Trend Micro explained.
“Customers who are continuing to have issues are advised to contact their authorized Trend Micro representative for further assistance.”