KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The Windows 10 KB5017308 cumulative update released this Patch Tuesday is reportedly causing Group Policy Object (GPO) issues, according to admin reports.
According to reports shared across multiple social networks and on Microsoft’s online community, GPO file operations will no longer work as they can no longer create or copy shortcuts correctly after installing KB5017308.
“Specifically, we copy a batch file into public\documents, then copy a shortcut to the current user’s desktop to run it,” one admin said on Reddit.
“Since the update, the icons are not transferring over for the shortcut (i.e they are blank icons now) and the batch file is actually empty when copied over.”
Also Read: What is Pseudonymisation: 5 Techniques and Its Best Practices
Another one confirmed this issue on the Microsoft Community website, saying that all shortcuts created by GPO are “created empty with 0 bytes and no info where shortcut “leads” to.”
While Microsoft is yet to officially acknowledge the issue and provide a fix or a workaround, multiple Windows admins have reported that un-checking the “Run in user security context” option on the affected GPOs will address the shortcut creation problems.
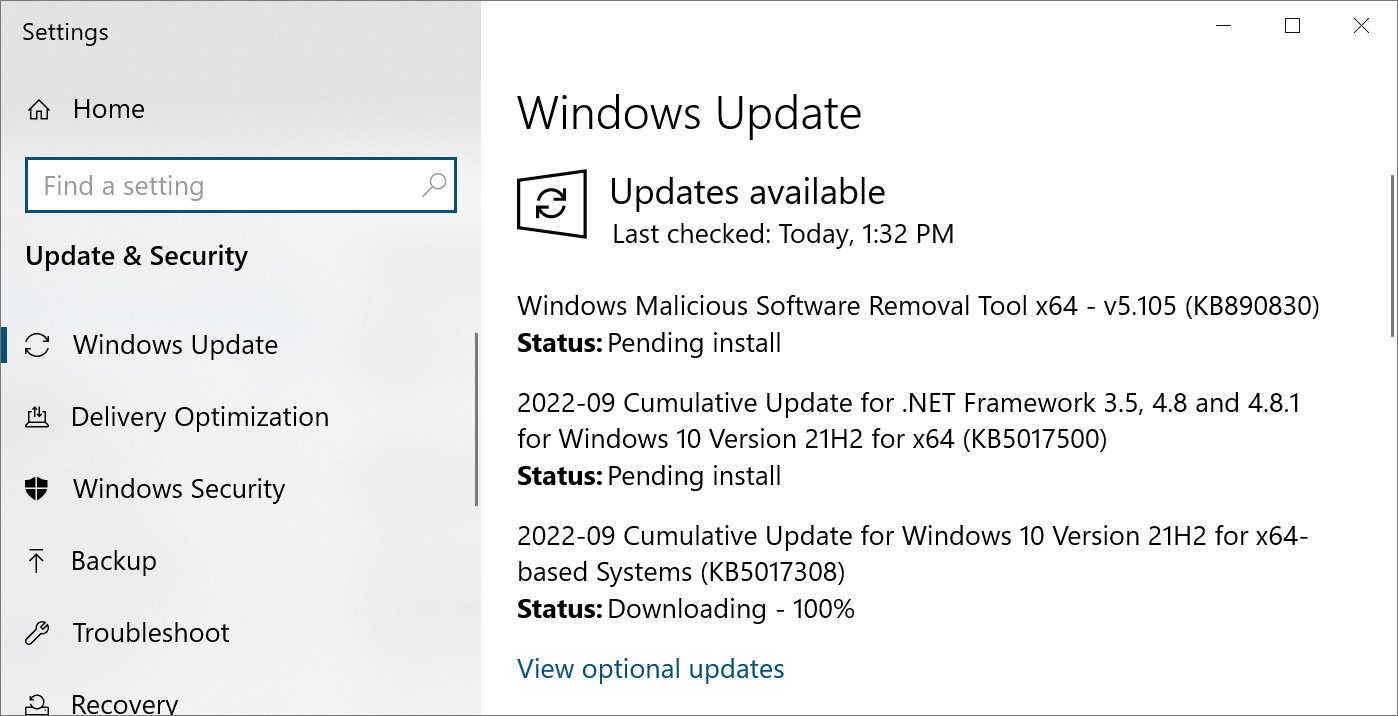
Others have also suggested a more radical fix that requires manually uninstalling and hiding the KB5017308 cumulative update.
“To remove the LCU after installing the combined SSU and LCU package, use the DISM/Remove-Package command line option with the LCU package name as the argument. You can find the package name by using this command: DISM /online /get-packages,” Microsoft says.
“Running Windows Update Standalone Installer (wusa.exe) with the /uninstall switch on the combined package will not work because the combined package contains the SSU. You cannot remove the SSU from the system after installation.”
However, it’s important to mention that, since Microsoft bundles all security fixes into a single update, removing KB5017308 may resolve the bug but will also remove all fixes for recently patched security vulnerabilities.
Also Read: 5 Simple Instructions on How to Access Request Form PDF
Another seemingly widespread problem encountered after deploying KB5017308 is affecting Windows 10 systems that will hang on reboot after installation with an 0x800F0845 added to the event log.
“Ever since that update was downloaded the machine hangs on the required reboot after the install. I have disabled updates until I can find a fix. I’ve tried to download the update and install manually but get the same results,” a user report reads.
Those affected say that the automatic rollback will only trigger after rebooting the affected systems twice in a row.
While downloading the update from the Microsoft Update Catalog and installing it manually usually fixes issues where the updates can’t be deployed, users who tried it said that, in this case, they encountered the same reboot hang bug.
The KB5017308 cumulative update was released on Tuesday to resolve bugs and address security vulnerabilities on systems running Windows 10 20H2, 21H1, and 21H2.
This Windows 10 update is mandatory and will automatically be installed by Windows Update during the servicing window.
H/T Günter Born