KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A recently created ransomware decryptor illustrates how threat actors have to support Windows XP, even when Microsoft dropped supporting it seven years ago.
Windows XP reached its end of life on April 8th, 2014, and even though it no longer receives security updates, more people use XP than Windows Vista, according to StatCounter and BleepingComputer’s website visitor stats.
According to StatCounter, Windows XP is used by 0.84% of the people running Windows, doubling Windows Vista’s current usage.
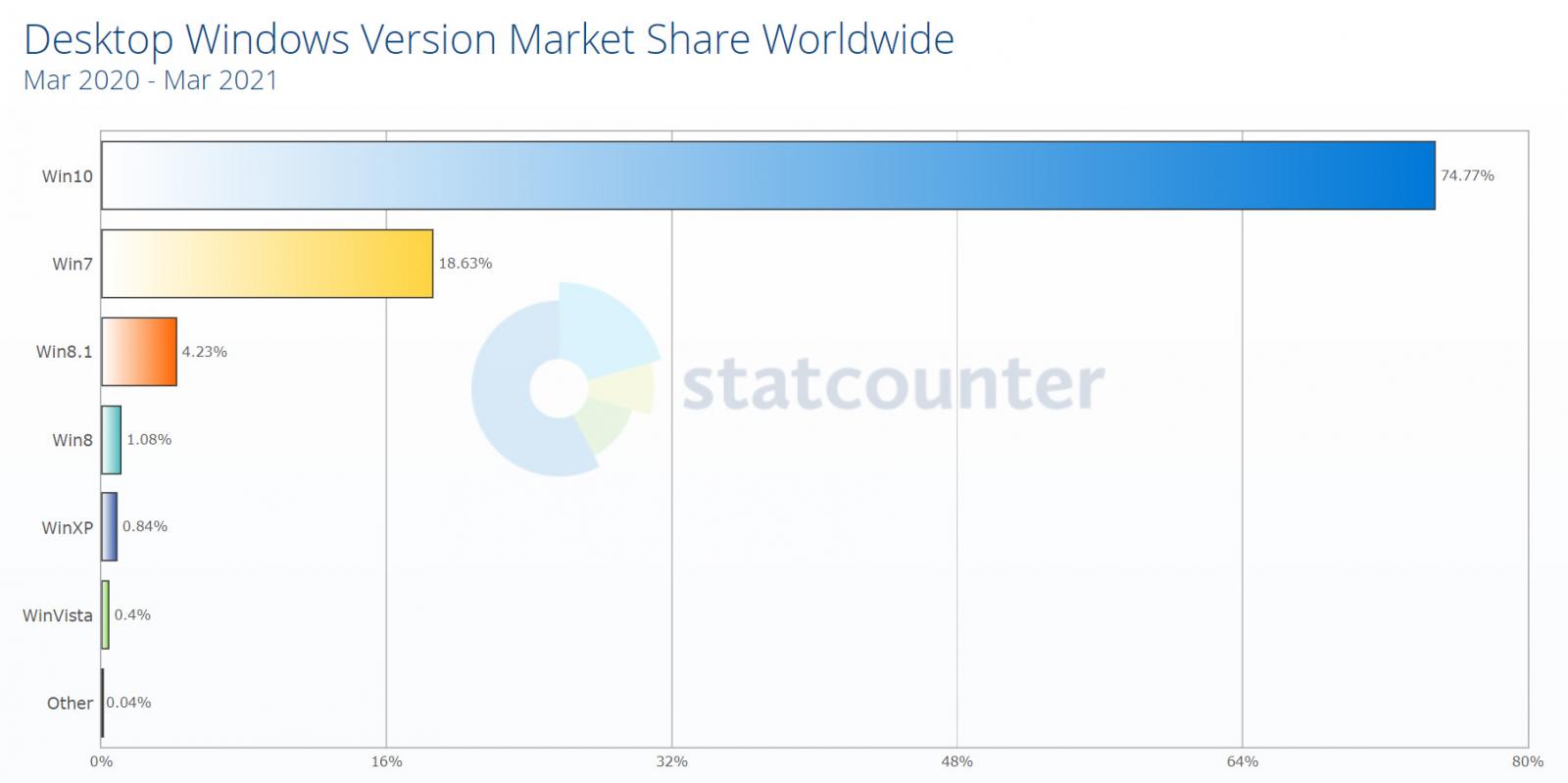
Similar percentages are seen with BleepingComputer’s visitors, with Windows XP being more commonly used today than Windows Vista. Furthermore, we are not talking about one or two people using Windows XP, but many thousands still actively using the operating system to browse the web.
Also Read: What You Should Know About The Data Protection Obligation Singapore
Why people are running such an old and insecure operating system is open to debate, but it could be due to legacy applications that they continue to use.
If an organization uses Windows XP and a ransomware attack encrypts the device, it now falls on the threat actors to support the operating system if they want to get paid.
This was shown by a new Avaddon ransomware decryptor discovered by MalwareHunterTeam that is created specifically to decrypt Windows XP devices.
When we asked Emsisoft CTO and ransomware expert Fabian Wosar why a ransomware gang would create a dedicated Windows XP decryptor, we were told it is likely due to lack of support for the operating system in modern compilers.
“Visual Studio 2019 no longer can compile for Windows XP. They need to use Visual Studio 2017 and an old XP compiler to build for XP.”
“The problem is when you want the latest C++ features, you need a newer compiler. But the newest compiler versions, won’t compile for XP.”
“So if your Crypto library you use for example uses C++17 features, you can’t build for XP at all, as there is no compiler targeting XP that has those features,” Wosar told BleepingComputer in a conversation.
Due to this, it is believed that the threat actors compile their normal decryptor on a new version of Visual Studio while using an older version of VC++ to support a Windows XP decryptor.
Wosar told BleepingComputer that Emsisoft does not offer their optimized and bug-free decryptors for Windows XP due to these issues.
Also Read: The Difference Between GDPR And PDPA Under 10 Key Issues
Should we feel bad that ransomware gangs have to deal with this? Nope.