KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






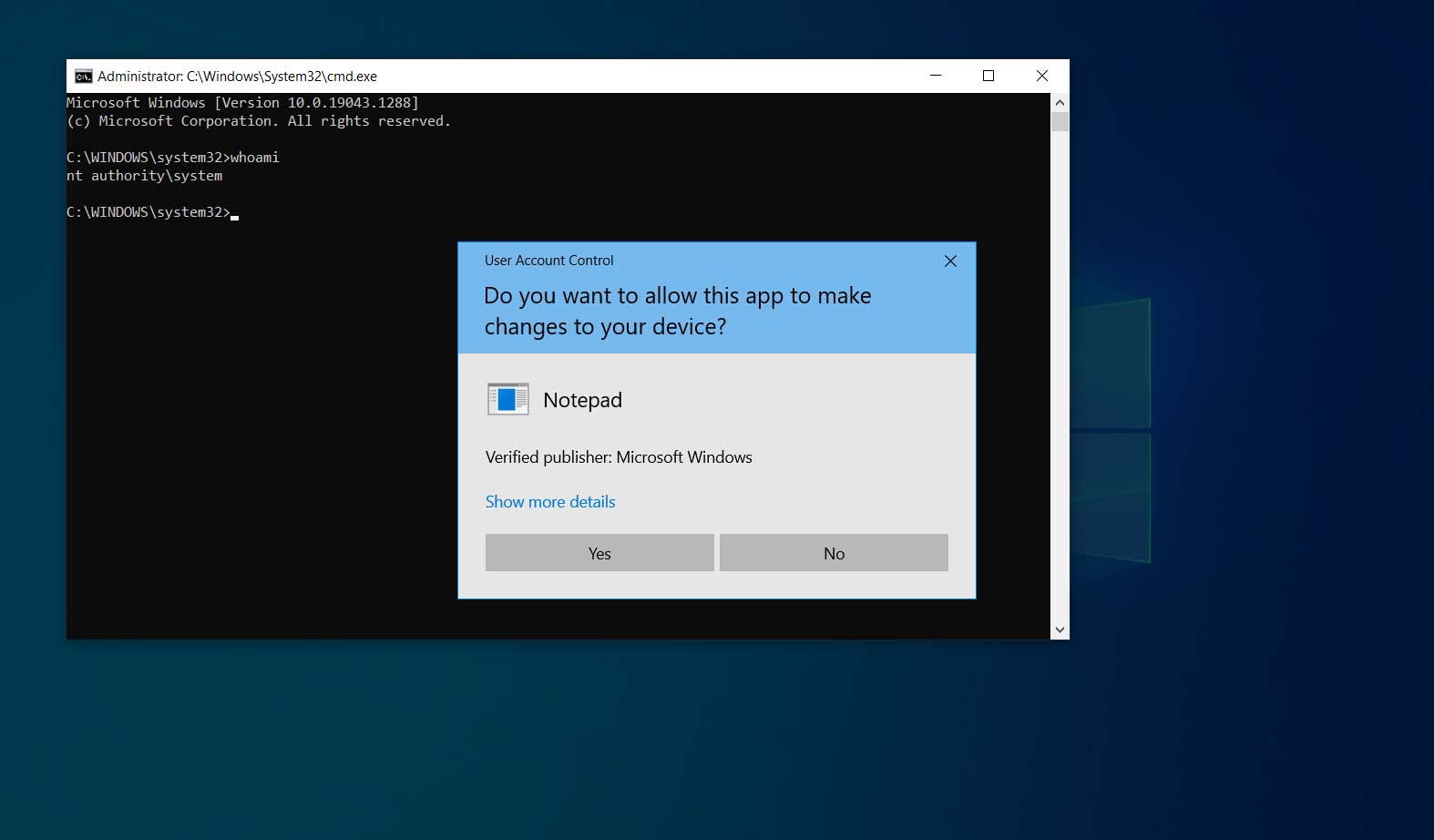
A Windows local privilege escalation zero-day vulnerability that Microsoft has failed to fully address for several months now, allows users to gain administrative privileges in Windows 10, Windows 11, and Windows Server.
The locally exploited vulnerability in Windows User Profile Service is tracked as CVE-2021-34484 and was given a CVSS v3 score of 7.8. While exploits have been publicly disclosed in the past, they are not believed to be actively exploited in the wild.
The peculiarity of this case lies in the fact that Microsoft has been unable to address the flaw since its discovery last summer and that it has marked the bug as fixed twice.
According to the 0patch team, which has been unofficially providing fixes for discontinued Windows versions and some vulnerabilities that Microsoft won’t address, the flaw is still a zero-day. In fact, Microsoft’s patches failed to fix the bug and broke 0patch’s previous unofficial patch.
Also Read: Ways to protect HR data and avoid penalties for data breaches
The Windows User Profile Service Elevation of Privilege Vulnerability, tracked as CVE-2021-34484, was discovered by security researcher Abdelhamid Naceri and disclosed to Microsoft, who fixed it as part of the August 2021 Patch Tuesday.
Soon after the fix was released, Naceri noticed that Microsoft’s patch was incomplete and presented a proof of concept (PoC) that bypassed it on all Windows versions.
The 0patch team stepped in at that point, releasing an unofficial security update for all Windows versions and making it free to download for all registered users.
Microsoft also responded to this bypass with a second security update released with the January 2022 Tuesday Patch Tuesday, giving the bypass a new tracking ID as CVE-2022-21919 and marking it as fixed. However, Naceri found a way to bypass that fix while commenting that this attempt was worse than the first.
While testing their patch against the researcher’s second bypass, 0patch found that their patch to the “profext.dll” DLL still protected users against the new exploitation method, allowing those systems to remain secure.
However, Microsoft’s second fixing attempt replaced the “profext.dll” file, leading to the removal of the unofficial fix from everyone who had applied the January 2022 Windows updates.
0patch has now ported the fix to work with the March 2022 Patch Tuesday updates and made it available for free to all registered users.
Also Read: Data Protection Act of Singapore: Validity in the Post-pandemic World
The Windows versions that can take advantage of the new micro-patch are the following:
It should be noted that Windows 10 1803, Windows 10 1809, and Windows 10 2004 are still protected by 0patch’s original patch, as those devices have reached the end of support and did not receive the Microsoft update that replaced the DLL.
The micro-patch will remain available as a free download to users of the above Windows versions as long as Microsoft hasn’t released a complete fix for the particular LPE problem and all its bypasses.
To those interested in taking up that offering, update your Windows 10 to the latest patch level (March 2022), create a free account in 0patch Central, and then install and register the 0patch Agent from here.
Doing that will initiate an automated micro-patching process with no manual actions or reboots required for the chances to take effect on your system.
Bleeping Computer has contacted Microsoft to ask if it’s planning to revisit the particular flaw and maybe try and fix it via a security update in the future, and a spokesperson of the company has shared the following comment:
“We’re aware of this report and will take action as needed to protect customers.”