KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Security researchers have shared lists of organizations where threat actors deployed Sunburst/Solarigate malware, after ongoing investigations of the SolarWinds supply chain attack.
One of these lists—shared by cybersecurity firm Truesec—includes high-profile tech companies such as Intel, Nvidia, Cisco, Cox Communications, and Belkin, to name just a few.
Mediatek, the world’s second-largest provider of fabless semiconductors, might have also been specifically targeted in this campaign but TrueSec hasn’t yet fully confirmed the breach at this point.
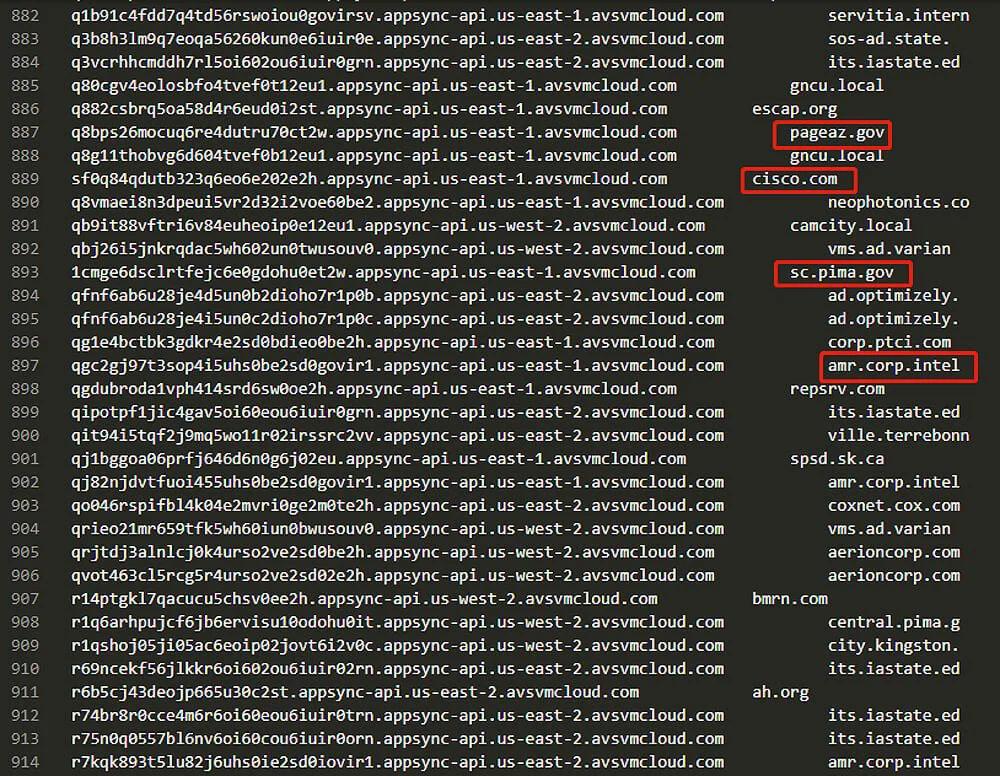
To build the list of victims infected with the Sunburst backdoor via the compromised update mechanism of the SolarWinds Orion IT management platform, the researchers decoded a dynamically generated part of the C2 subdomain for each of the compromised devices.
The list of encoded C2 subdomains used by the Sunburst malware was harvested from passive DNS (pDNS) datasets and web traffic pointing to the main avsvmcloud[.]com C2 domain contacted by the backdoor to exfiltrate stolen data.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
By decoding this list of subdomains generated by the malware’s domain generation algorithm (DGA), TrueSec and other security firms including QiAnXin RedDrip, Kaspersky, and Prevasio [1, 2], were able to find many well-known organizations that have already or may disclose targeted attacks later on.
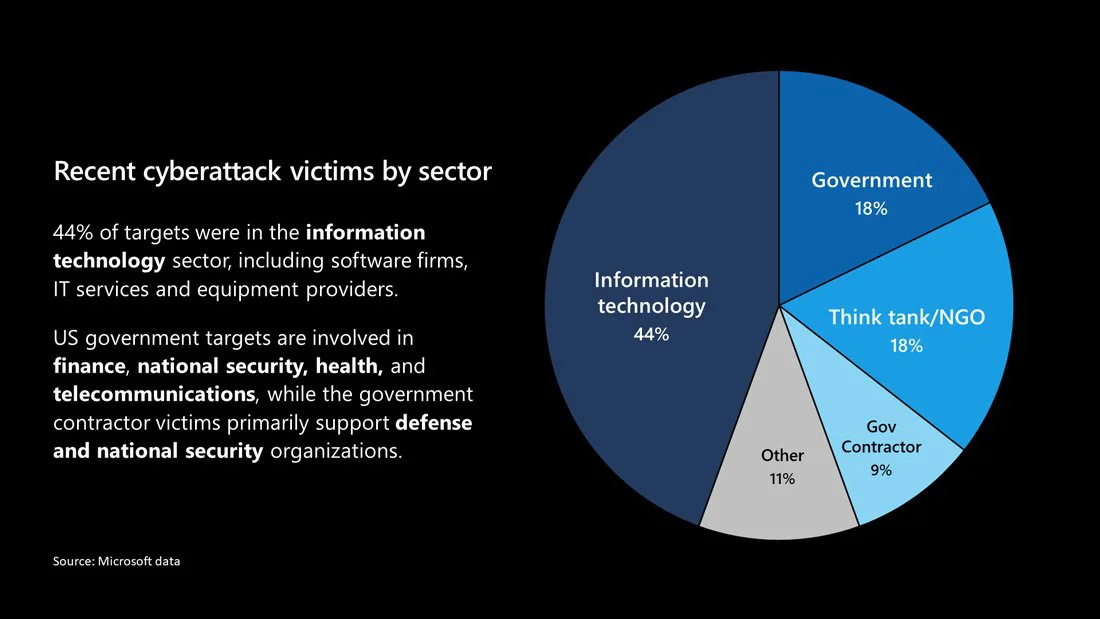
While Microsoft also found that more than 40 of its customers had their networks infiltrated following the SolarWinds supply chain attack, the company notified them but did not disclose their identity. Redmond did say that 80% of the victims were from the US and 44% were in the IT sector.
FireEye, Microsoft, and VMware were also breached by the hackers behind the SolarWinds supply chain attack but only FireEye was targeted for the second stage of the attack and had information stolen from its network.
Even though SolarWinds said that the malicious Orion updates were installed by roughly 18,000 customers in this attack, the threat actors who orchestrated it (tracked by FireEye as UNC2452 and by Volexity as Dark Halo) only targeted ‘high value’ orgs for further exploitation.
The known list of organizations hit by the SolarWinds supply chain attack also includes multiple US states and government agencies:
TrueSec’s extensive list of decoded Sunburst C2 subdomains provides a list of internal organization names that weren’t only infected with the backdoor but were also individually targeted and where the hackers likely escalated their attacks to further internal compromise.
“We have decoded the DGA parts of the requests to identify internal domain names of compromised organizations, correlated that with the responses received from the threat actor server, and mapped them with the hardcoded list of IP ranges in the backdoor code,” TrueSec said.
This allowed the researchers to get a partial list of breached organizations, as well as pinpoint the ones which were singled out by the hacking group for the second stage of the attack.
“This list contains the decoded values of internal domain names. We can therefore only assume that they belong to an organization based on the name of the domains and publicly available information,” TrueSec added.
“More information will be disclosed during the upcoming months but the full extent of this breach will most likely never be communicated to the public, and instead will be restricted to trusted parts of the intelligence community.”
The current list of decoded internal names for some of the companies that were breached by the SolarWinds hackers is embedded below (the organization names might be inaccurate given that they are based on decoded internal names).
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
| Decoded Internal Name | Organization (possibly inaccurate) | Response Address Family | Command | First Seen |
|---|---|---|---|---|
| mnh.rg-law.ac.il | College of Law and Business, Israel | NetBios | HTTP Backdoor | 2020-05-26 |
| ad001.mtk.lo | Mediatek | NetBios | HTTP Backdoor | 2020-08-26 |
| Aeria | NetBios | HTTP Backdoor | 2020-06-26 | |
| Ameri | NetBios | HTTP Backdoor | 2020-08-02 | |
| ank.com | Ankcom Communications | NetBios | HTTP Backdoor | 2020-06-06 |
| azlcyy | NetBios | HTTP Backdoor | 2020-08-07 | |
| banccentral.com | BancCentral Financial Services Corp. | NetBios | HTTP Backdoor | 2020-07-03 |
| barrie.ca | City of Barrie | NetBios | HTTP Backdoor | 2020-05-13 |
| BCC.l | NetBios | HTTP Backdoor | 2020-08-22 | |
| bhq.lan | NetBios | HTTP Backdoor | 2020-08-18 | |
| cds.capilanou. | Capilano University | NetBios | HTTP Backdoor | 2020-08-27 |
| Centr | NetBios | HTTP Backdoor | 2020-06-24 | |
| chc.dom | NetBios | HTTP Backdoor | 2020-08-04 | |
| christieclinic. | Christie Clinic Telehealth | NetBios | HTTP Backdoor | 2020-04-22 |
| CIMBM | NetBios | HTTP Backdoor | 2020-09-25 | |
| CIRCU | NetBios | HTTP Backdoor | 2020-05-30 | |
| CONSO | NetBios | HTTP Backdoor | 2020-06-17 | |
| corp.ptci.com | Pioneer Telephone Scholarship Recipients | NetBios | HTTP Backdoor | 2020-06-19 |
| corp.stingraydi | Stingray (Media and entertainment) | NetBios | HTTP Backdoor | 2020-06-10 |
| corp.stratusnet | Stratus Networks | NetBios | HTTP Backdoor | 2020-04-28 |
| cosgroves.local | Cosgroves (Building services consulting) | NetBios | HTTP Backdoor | 2020-08-25 |
| COTES | Cotes (Humidity Management) | NetBios | HTTP Backdoor | 2020-07-25 |
| csnt.princegeor | City of Prince George | NetBios | HTTP Backdoor | 2020-09-18 |
| cys.local | CYS Group (Marketing analytics) | NetBios | HTTP Backdoor | 2020-07-10 |
| digitalsense.co | Digital Sense (Cloud Services) | NetBios | HTTP Backdoor | 2020-06-24 |
| ehtuh- | NetBios | HTTP Backdoor | 2020-05-01 | |
| escap.org | NetBios | HTTP Backdoor | 2020-07-10 | |
| f.gnam | NetBios | HTTP Backdoor | 2020-04-04 | |
| fhc.local | NetBios | HTTP Backdoor | 2020-07-06 | |
| fidelitycomm.lo | Fidelity Communications (ISP) | NetBios | HTTP Backdoor | 2020-06-02 |
| fisherbartoninc.com | The Fisher Barton Group (Blade Manufacturer) | NetBios | HTTP Backdoor | 2020-05-15 |
| fmtn.ad | City of Farmington | NetBios | HTTP Backdoor | 2020-07-21 |
| FWO.I | NetBios | HTTP Backdoor | 2020-08-05 | |
| ggsg-us.cisco | Cisco GGSG | NetBios | HTTP Backdoor | 2020-06-24 |
| ghsmain1.ggh.g | NetBios | HTTP Backdoor | 2020-06-09 | |
| gxw | NetBios | HTTP Backdoor | 2020-07-07 | |
| htwanmgmt.local | NetBios | HTTP Backdoor | 2020-07-22 | |
| ieb.go.id | NetBios | HTTP Backdoor | 2020-06-12 | |
| int.ncahs.net | NetBios | HTTP Backdoor | 2020-09-23 | |
| internal.jtl.c | NetBios | HTTP Backdoor | 2020-05-19 | |
| ironform.com | Ironform (metal fabrication) | NetBios | HTTP Backdoor | 2020-06-19 |
| isi | NetBios | HTTP Backdoor | 2020-07-06 | |
| itps.uk.net | Infection Prevention Society (IPS) | NetBios | HTTP Backdoor | 2020-08-11 |
| jxxyx. | NetBios | HTTP Backdoor | 2020-06-26 | |
| kcpl.com | Kansas City Power and Light Company | NetBios | HTTP Backdoor | 2020-07-07 |
| keyano.local | Keyano College | NetBios | HTTP Backdoor | 2020-06-03 |
| khi0kl | NetBios | HTTP Backdoor | 2020-08-26 | |
| lhc_2f | NetBios | HTTP Backdoor | 2020-04-18 | |
| lufkintexas.net | Lufkin (City in Texas) | NetBios | HTTP Backdoor | 2020-07-07 |
| magnoliaisd.loc | Magnolia Independent School District | NetBios | HTTP Backdoor | 2020-06-01 |
| MOC.l | NetBios | HTTP Backdoor | 2020-04-30 | |
| moncton.loc | City of Moncton | NetBios | HTTP Backdoor | 2020-08-25 |
| mountsinai.hosp | Mount Sinai Hospital | NetBios | HTTP Backdoor | 2020-07-02 |
| netdecisions.lo | Netdecisions (IT services) | NetBios | HTTP Backdoor | 2020-10-04 |
| newdirections.k | NetBios | HTTP Backdoor | 2020-04-21 | |
| nswhealth.net | NSW Health | NetBios | HTTP Backdoor | 2020-06-12 |
| nzi_9p | NetBios | HTTP Backdoor | 2020-08-04 | |
| city.kingston.on.ca | City of Kingston, Ontario, Canada | NetBios | HTTP Backdoor | 2020-06-15 |
| dufferincounty.on.ca | Dufferin County, Ontario, Canada | NetBios | HTTP Backdoor | 2020-07-17 |
| osb.local | NetBios | HTTP Backdoor | 2020-04-28 | |
| oslerhc.org | William Osler Health System | NetBios | HTTP Backdoor | 2020-07-11 |
| pageaz.gov | City of Page | NetBios | HTTP Backdoor | 2020-04-19 |
| pcsco.com | Professional Computer Systems | NetBios | HTTP Backdoor | 2020-07-23 |
| pkgix_ | NetBios | HTTP Backdoor | 2020-07-15 | |
| pqcorp.com | PQ Corporation | NetBios | HTTP Backdoor | 2020-07-02 |
| prod.hamilton. | Hamilton Company | NetBios | HTTP Backdoor | 2020-08-19 |
| resprod.com | Res Group (Renewable energy company) | NetBios | HTTP Backdoor | 2020-05-06 |
| RPM.l | NetBios | HTTP Backdoor | 2020-05-28 | |
| sdch.local | South Davis Community Hospital | NetBios | HTTP Backdoor | 2020-05-18 |
| servitia.intern | NetBios | HTTP Backdoor | 2020-06-16 | |
| sfsi.stearnsban | Stearns Bank | NetBios | HTT P Backdoor | 2020-08-02 |
| signaturebank.l | Signature Bank | NetBios | HTTP Backdoor | 2020-06-25 |
| sm-group.local | SM Group (Distribution) | NetBios | HTTP Backdoor | 2020-07-07 |
| te.nz | TE Connectivity (Sensor manufacturer) | NetBios | HTTP Backdoor | 2020-05-13 |
| thx8xb | NetBios | HTTP Backdoor | 2020-06-16 | |
| tx.org | NetBios | HTTP Backdoor | 2020-07-15 | |
| usd373.org | Newton Public Schools | NetBios | HTTP Backdoor | 2020-08-01 |
| uzq | NetBios | HTTP Backdoor | 2020-10-02 | |
| ville.terrebonn | Ville de Terrebonne | NetBios | HTTP Backdoor | 2020-08-02 |
| wrbaustralia.ad | W. R. Berkley Insurance Australia | NetBios | HTTP Backdoor | 2020-07-11 |
| ykz | NetBios | HTTP Backdoor | 2020-07-11 | |
| 2iqzth | ImpLink | Enum processes | 2020-06-17 | |
| 3if.2l | 3IF (Industrial Internet) | ImpLink | Enum processes | 2020-08-20 |
| airquality.org | Sacramento Metropolitan Air Quality Management District | ImpLink | Enum processes | 2020-08-09 |
| ansc.gob.pe | GOB (Digital Platform of the Peruvian State) | ImpLink | Enum processes | 2020-07-25 |
| bcofsa.com.ar | Banco de Formosa | ImpLink | Enum processes | 2020-07-13 |
| bi.corp | ImpLink | Enum processes | 2020-12-14 | |
| bop.com.pk | The Bank of Punjab | ImpLink | Enum processes | 2020-09-18 |
| camcity.local | ImpLink | Enum processes | 2020-08-07 | |
| cow.local | ImpLink | Enum processes | 2020-06-13 | |
| deniz.denizbank | DenizBank | ImpLink | Enum processes | 2020-11-14 |
| ies.com | IES Communications (Communications technology) | ImpLink | Enum processes | 2020-06-11 |
| insead.org | INSEAD Business School | ImpLink | Enum processes | 2020-11-07 |
| KS.LO | ImpLink | Enum processes | 2020-07-10 | |
| mixonhill.com | Mixon Hill (intelligent transportation systems) | ImpLink | Enum processes | 2020-04-29 |
| ni.corp.natins | ImpLink | Enum processes | 2020-10-24 | |
| phabahamas.org | Public Hospitals Authority, Caribbean | ImpLink | Enum processes | 2020-11-05 |
| rbe.sk.ca | Regina Public Schools | ImpLink | Enum processes | 2020-08-20 |
| spsd.sk.ca | Saskatoon Public Schools | ImpLink | Enum processes | 2020-06-12 |
| yorkton.cofy | Community Options for Families & Youth | ImpLink | Enum processes | 2020-05-08 |
| .sutmf | Ipx | Update config | 2020-06-25 | |
| atg.local | No Match | Unknown | 2020-05-11 | |
| bisco.int | Bisco International (Adhesives and tapes) | No Match | Unknown | 2020-04-30 |
| ccscurriculum.c | No Match | Unknown | 2020-04-18 | |
| e-idsolutions. | IDSolutions (video conferencing) | No Match | Unknown | 2020-07-16 |
| ETC1. | No Match | Unknown | 2020-08-01 | |
| gk5 | No Match | Unknown | 2020-07-09 | |
| grupobazar.loca | No Match | Unknown | 2020-06-07 | |
| internal.hws.o | No Match | Unknown | 2020-05-23 | |
| n2k | No Match | Unknown | 2020-07-12 | |
| publiser.it | No Match | Unknown | 2020-07-05 | |
| us.deloitte.co | Deloitte | No Match | Unknown | 2020-07-08 |
| ush.com | No Match | Unknown | 2020-06-15 | |
| xijtt- | No Match | Unknown | 2020-07-21 | |
| xnet.kz | X NET (IT provider in Kazakhstan) | No Match | Unknown | 2020-06-09 |
| zu0 | No Match | Unknown | 2020-08-13 | |
| staff.technion.ac.il | N/A | N/A | N/A | |
| digitalreachinc.com | N/A | N/A | N/A | |
| orient-express.com | N/A | N/A | N/A | |
| tr.technion.ac.il | N/A | N/A | N/A | |
| lasers.state.la.us | N/A | N/A | N/A | |
| ABLE. | N/A | N/A | N/A | |
| abmuh_ | N/A | N/A | N/A | |
| acmedctr.ad | N/A | N/A | N/A | |
| ad.azarthritis.com | N/A | N/A | N/A | |
| ad.library.ucla.edu | N/A | N/A | N/A | |
| ad.optimizely. | N/A | N/A | N/A | |
| admin.callidusc | N/A | N/A | N/A | |
| aerioncorp.com | N/A | N/A | N/A | |
| agloan.ads | N/A | N/A | N/A | |
| ah.org | N/A | N/A | N/A | |
| AHCCC | N/A | N/A | N/A | |
| allegronet.co. | N/A | N/A | N/A | |
| alm.brand.dk | N/A | N/A | N/A | |
| amalfi.local | N/A | N/A | N/A | |
| americas.phoeni | N/A | N/A | N/A | |
| amr.corp.intel | N/A | N/A | N/A | |
| apu.mn | N/A | N/A | N/A | |
| ARYZT | N/A | N/A | N/A | |
| b9f9hq | N/A | N/A | N/A | |
| BE.AJ | N/A | N/A | N/A | |
| belkin.com | N/A | N/A | N/A | |
| bk.local | N/A | N/A | N/A | |
| bmrn.com | N/A | N/A | N/A | |
| bok.com | N/A | N/A | N/A | |
| btb.az | N/A | N/A | N/A | |
| c4e-internal.c | N/A | N/A | N/A | |
| calsb.org | N/A | N/A | N/A | |
| casino.prv | N/A | N/A | N/A | |
| cda.corp | N/A | N/A | N/A | |
| central.pima.g | N/A | N/A | N/A | |
| cfsi.local | N/A | N/A | N/A | |
| ch.local | N/A | N/A | N/A | |
| ci.dublin.ca. | N/A | N/A | N/A | |
| cisco.com | N/A | N/A | N/A | |
| corp.dvd.com | N/A | N/A | N/A | |
| corp.sana.com | N/A | N/A | N/A | |
| Count | N/A | N/A | N/A | |
| COWI. | N/A | N/A | N/A | |
| coxnet.cox.com | N/A | N/A | N/A | |
| CRIHB | N/A | N/A | N/A | |
| cs.haystax.loc | N/A | N/A | N/A | |
| csa.local | N/A | N/A | N/A | |
| csci-va.com | N/A | N/A | N/A | |
| csqsxh | N/A | N/A | N/A | |
| DCCAT | N/A | N/A | N/A | |
| deltads.ent | N/A | N/A | N/A | |
| detmir-group.r | N/A | N/A | N/A | |
| dhhs- | N/A | N/A | N/A | |
| dmv.state.nv. | N/A | N/A | N/A | |
| dotcomm.org | N/A | N/A | N/A | |
| DPCIT | N/A | N/A | N/A | |
| dskb2x | N/A | N/A | N/A | |
| e9.2pz | N/A | N/A | N/A | |
| ebe.co.roanoke.va.us | N/A | N/A | N/A | |
| ecobank.group | N/A | N/A | N/A | |
| ecocorp.local | N/A | N/A | N/A | |
| epl.com | N/A | N/A | N/A | |
| fremont.lamrc. | N/A | N/A | N/A | |
| FSAR. | N/A | N/A | N/A | |
| ftfcu.corp | N/A | N/A | N/A | |
| gksm.local | N/A | N/A | N/A | |
| gloucesterva.ne | N/A | N/A | N/A | |
| glu.com | N/A | N/A | N/A | |
| gnb.local | N/A | N/A | N/A | |
| gncu.local | N/A | N/A | N/A | |
| gsf.cc | N/A | N/A | N/A | |
| gyldendal.local | N/A | N/A | N/A | |
| helixwater.org | N/A | N/A | N/A | |
| hgvc.com | N/A | N/A | N/A | |
| ia.com | N/A | N/A | N/A | |
| inf.dc.net | N/A | N/A | N/A | |
| ingo.kg | N/A | N/A | N/A | |
| innout.corp | N/A | N/A | N/A | |
| int.lukoil-international.uz | N/A | N/A | N/A | |
| intensive.int | N/A | N/A | N/A | |
| ions.com | N/A | N/A | N/A | |
| its.iastate.ed | N/A | N/A | N/A | |
| jarvis.lab | N/A | N/A | N/A | |
| -jlowd | N/A | N/A | N/A | |
| jn05n8 | N/A | N/A | N/A | |
| jxb3eh | N/A | N/A | N/A | |
| k.com | N/A | N/A | N/A | |
| LABEL | N/A | N/A | N/A | |
| milledgeville.l | N/A | N/A | N/A | |
| nacr.com | N/A | N/A | N/A | |
| ncpa.loc | N/A | N/A | N/A | |
| neophotonics.co | N/A | N/A | N/A | |
| net.vestfor.dk | N/A | N/A | N/A | |
| nih.if | N/A | N/A | N/A | |
| nvidia.com | N/A | N/A | N/A | |
| on-pot | N/A | N/A | N/A | |
| ou0yoy | N/A | N/A | N/A | |
| paloverde.local | N/A | N/A | N/A | |
| pl8uw0 | N/A | N/A | N/A | |
| q9owtt | N/A | N/A | N/A | |
| rai.com | N/A | N/A | N/A | |
| rccf.ru | N/A | N/A | N/A | |
| repsrv.com | N/A | N/A | N/A | |
| ripta.com | N/A | N/A | N/A | |
| roymerlin.com | N/A | N/A | N/A | |
| rs.local | N/A | N/A | N/A | |
| rst.atlantis-pak.ru | N/A | N/A | N/A | |
| sbywx3 | N/A | N/A | N/A | |
| sc.pima.gov | N/A | N/A | N/A | |
| scif.com | N/A | N/A | N/A | |
| SCMRI | N/A | N/A | N/A | |
| scroot.com | N/A | N/A | N/A | |
| seattle.interna | N/A | N/A | N/A | |
| securview.local | N/A | N/A | N/A | |
| SFBAL | N/A | N/A | N/A | |
| SF-Li | N/A | N/A | N/A | |
| siskiyous.edu | N/A | N/A | N/A | |
| sjhsagov.org | N/A | N/A | N/A | |
| Smart | N/A | N/A | N/A | |
| smes.org | N/A | N/A | N/A | |
| sos-ad.state.nv.us | N/A | N/A | N/A | |
| sro.vestfor.dk | N/A | N/A | N/A | |
| superior.local | N/A | N/A | N/A | |
| swd.local | N/A | N/A | N/A | |
| ta.org | N/A | N/A | N/A | |
| taylorfarms.com | N/A | N/A | N/A | |
| thajxq | N/A | N/A | N/A | |
| thoughtspot.int | N/A | N/A | N/A | |
| tsyahr | N/A | N/A | N/A | |
| tv2.local | N/A | N/A | N/A | |
| uis.kent.edu | N/A | N/A | N/A | |
| uncity.dk | N/A | N/A | N/A | |
| uont.com | N/A | N/A | N/A | |
| viam-invenient | N/A | N/A | N/A | |
| vms.ad.varian.com | N/A | N/A | N/A | |
| vsp.com | N/A | N/A | N/A | |
| WASHO | N/A | N/A | N/A | |
| weioffice.com | N/A | N/A | N/A | |
| wfhf1.hewlett. | N/A | N/A | N/A | |
| woodruff-sawyer | N/A | N/A | N/A | |
| HQ.RE-wwgi2xnl | N/A | N/A | N/A | |
| xdxinc.net | N/A | N/A | N/A | |
| y9k.in | N/A | N/A | N/A | |
| zeb.i8 | N/A | N/A | N/A | |
| zippertubing.co | N/A | N/A | N/A |