KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A list of dozens of online stores hacked by a web skimming group was inadvertently leaked by a dropper used to deploy a stealthy remote access trojan (RAT) on compromised e-commerce sites.
The threat actors use this RAT for maintaining persistence and for regaining access to the servers of hacked online shops.
Once they connect to the stores, the attackers deploy credit card skimmer scripts that steal and exfiltrate customers’ personal and financial data in digital skimming attacks (also known as Magecart).
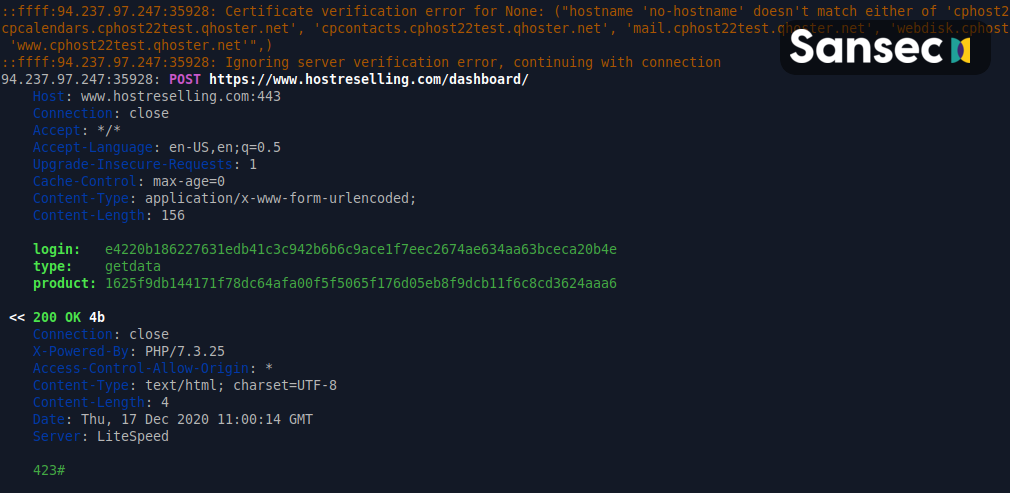
Researchers at Sansec, a security company focused on protecting e-commerce stores from web skimming attacks, said that the malware was delivered in the form of a 64-bit ELF executable with the help of a PHP-based malware dropper.
Also Read: Data Protection Authority GDPR: Everything You Need To Know
To evade detection and hinder analysis, the unnamed RAT is designed to camouflage itself as a DNS or an SSH server daemon so that it doesn’t stand out in the server’s process list.
The malware also runs in sleep mode almost throughout the day, only waking up once per day early in the morning, at 7 AM, to connect to its command-and-control server and ask for commands.
RAT samples harvested by Sansec from several compromised servers have been compiled by the threat actors behind these attacks on both Ubuntu and Red Hat Linux.
“This may indicate that multiple people were involved in this campaign,” Sansec says in a report published earlier today.
“Or, for example, that the RAT source code is publicly available, and possibly for sale on dark web markets.”
Despite the quite advanced RAT malware they used as a backdoor into hacked e-commerce servers, the Magecart group also made one rookie mistake by including a list of hacked online stores within their dropper’s code.
Sansec hijacked the attackers’ RAT dropper and found that it also contained a list of 41 compromised stores besides the usual malicious code used to parse deployment setups for several Magecart scripts.
This might be explained by the fact that the dropper has been coded by someone who seems to have a lot less experience with PHP as it “uses shared memory blocks, which is rarely used in PHP but is much more common in C programs.”
Sansec has also reached out to the online stores included in the Magecart malware dropper’s code to let them know that their servers have been infiltrated.

During the last couple of months, Sansec researchers have unearthed multiple Magecart skimmers and malware samples that use innovative tactics for persistence or to evade detection.
A credit card stealer script found in three different stores, still active when BleepingComputer reported the info last week, hides in plain sight on hacked sites using CSS code as it avoids getting discovered via conventional methods such as automated security scanners and even manual security code audits.
Also Read: The Importance Of Knowing Personal Data Protection Regulations
They also recently discovered web skimming malware capable of camouflaging as SVG social media buttons and an almost impossible to get rid of credit card stealer that bundles a persistent backdoor.