KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The Security Service of Ukraine (SSU) has arrested five members of the international ‘Phoenix’ hacking group who specialize in the remote hacking of mobile devices.
The SSU’s announcement states that all five suspects live in Kyiv or Kharkiv and are higher technical education institutes graduates.
The goal of ‘Phoenix’ was to gain remote access to the accounts of mobile device users and then monetize them by hijacking their e-payment or bank accounts or selling their private information to third parties.
To steal mobile accounts of mobile device users, the actors used phishing sites that were clones of Apple’s and Samsung’s login portals.
Also Read: 5 Brief Concepts Between Data Protection Directive vs GDPR
This activity went on for at least two years, during which Phoenix hacked several hundred people’s accounts.
The hackers also offered remote mobile phone hacking services to others, charging between $100 and $200.
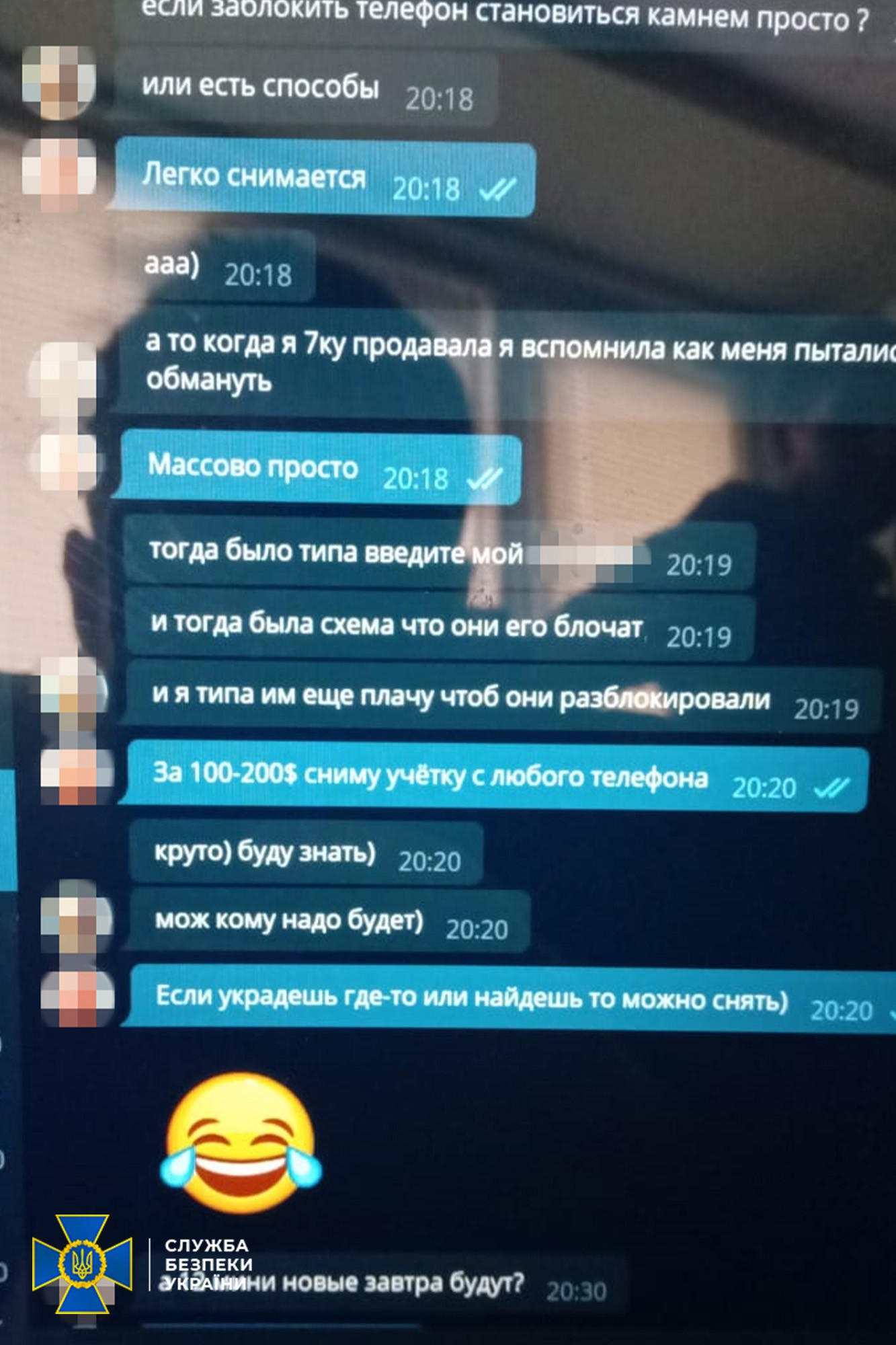
Finally, the group was also unlocking stolen or lost devices made by Apple, tied to the original purchaser by locking them to the first account created on the device.
The police have conducted five searches in each arrest location, seizing computer equipment, mobile phones, specialized software, and hardware.

While conducting searches of homes and fake telephone shops, officers found several devices that appeared to have been stolen and were being prepared for reselling as new in the Kyiv region.
Also Read: Top 10 Best Freelance Testing Websites That Will Pay You
The threat actors now face charges relevant to Article 361 of the Criminal Code of Ukraine for illegal interference in the work of electronic computers, systems, and computer networks.
While the five arrested individuals are most likely all the ‘Phoenix’ group members, the authorities will continue the investigations to potentially identify more conspirators.
Ukraine has been actively cracking down on cybercrime activity originating from their country, with recent arrests of ransomware members, money launderers, and threat actors behind DDoS attacks.