KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







UL LLC, better known as Underwriters Laboratories, has suffered a ransomware attack that encrypted its servers and caused them to shut down systems while they recover.
UL is the largest and oldest safety certification company in the United States, with 14,000 employees and offices in over 40 countries.
If you have ever looked at the back of an electric appliance, laptop, TV remote, lightbulb, or even your Apple USB charger, the UL logo imprinted on the device is instantly recognizable.

Also Read: How Bank Disclosure Of Customer Information Work For Security
When companies release new products, they commonly submit them to UL to be tested and certified under nationally recognized safety and sustainability standards. Based on what tests were conducted and their results, the product will receive varying UL certifications.
In addition to product safety certifications, UL is also develops the very popular 3DMark, PCMark, and VRMark PC and graphics benchmark utilities.
If you have first-hand information about this or other unreported cyberattacks, you can confidentially contact us on Signal at +16469613731 or on Wire at @lawrenceabrams-bc.
BleepingComputer has learned that UL suffered a ransomware attack last weekend that encrypted devices in their data center.
To prevent further spread of the attack, the company shut down its systems, making it impossible for some employees to perform their jobs.
UL told employees not to contact the threat actors or visit any sites related to the ransomware operation.
According to a source familiar with the attack, UL has decided not to pay the ransom and is restoring from backups instead.
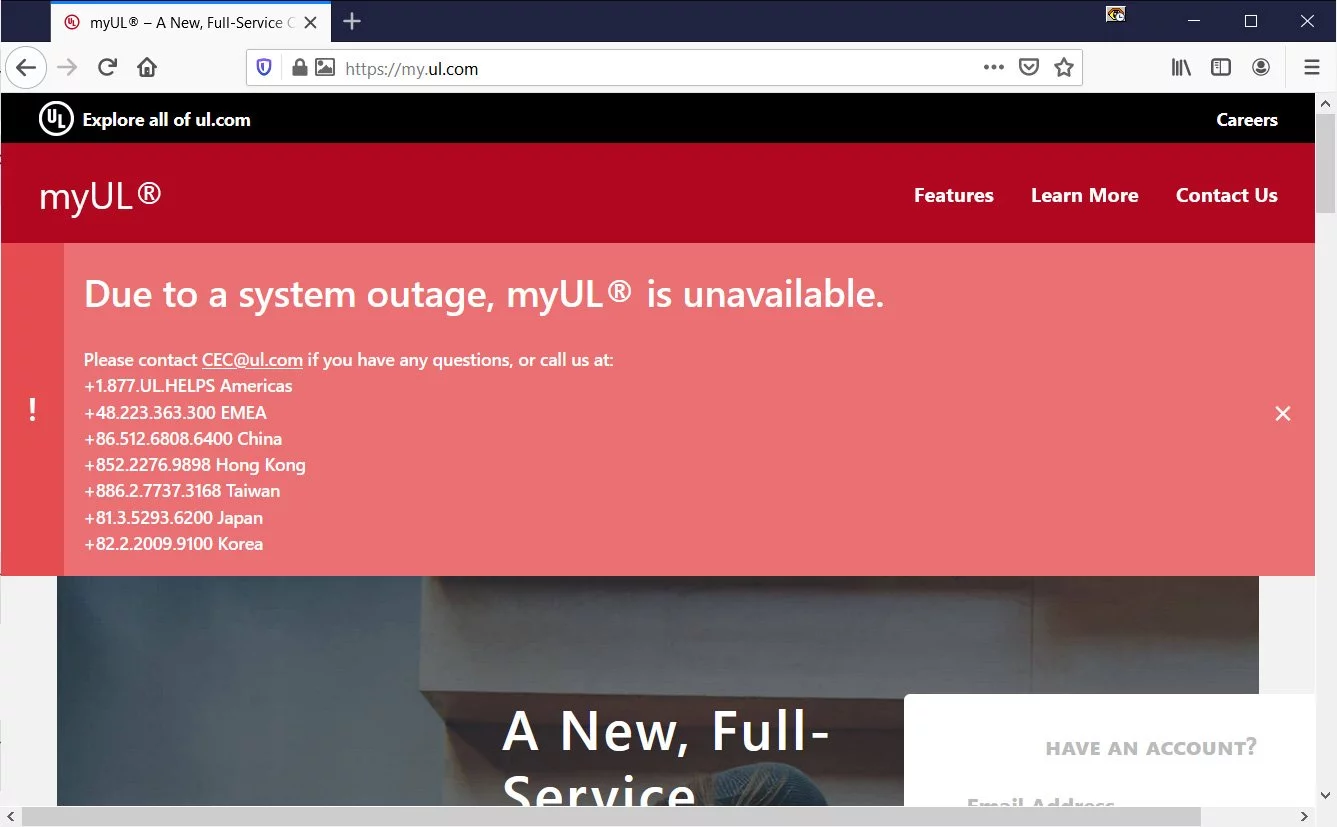
As it takes time to restore devices, the attack has led to the myUL client portal remaining offline while they recover.
In a statement to BleepingComputer, UL confirmed that the attack occurred on February 13th and is currently investigating the attack.
“UL detected unusual activity on its systems on February 13, 2021 and immediately took precautions to address the situation, including shutting down systems, engaging a leading cybersecurity firm to help us investigate and alerting appropriate authorities. Our immediate priority is to restore our systems to minimize any disruption this has on our customers.”
“Until we learn more from our investigation, we cannot speculate as to the type of information that may be potentially impacted. If we determine that data is impacted, we will take appropriate actions” – UL LLC
It is unknown what ransomware operation conducted the attack and whether they stole unencrypted files.
Also Read: Data Protection Framework: Practical Guidance For Businesses
As most enterprise-targeting ransomware operations steal unencrypted files to be used in a double-extortion strategy, the ransomware gang likely stole data during the attack.
Update 2/19/21: Added that they are the developers of PC benchmark tools.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
