KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A security analyst has devised a way to capture Visual Voice Mail (VVM) credentials on Android devices and then remotely listen to voicemail messages without the victim’s knowledge.
The security researcher, Chris Talbot, discovered the flaw on June 21, 2021, and filed the vulnerability under CVE-2022-23835.
The bug is not a flaw in the Android operating system but rather how the service is implemented by mobile carriers.
However, the flaw has a “disputed” status because AT&T and T-Mobile dismissed the report for describing a non-exploitable risk, while Sprint and Verizon have not responded.
Also Read: 6 Simple Tips on Cyber Safety at Home
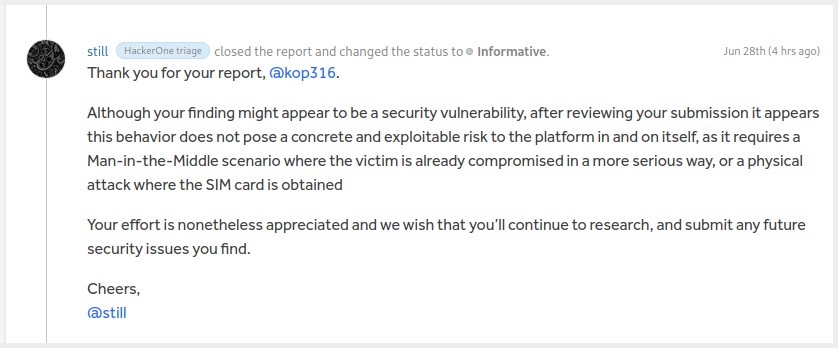
Even though the flaw’s exploitability is in question, the CERT Coordination Center has published the details of Talbot’s discovery today due to the potential impact and the existence of a published PoC (proof of concept) tool to exploit the bug.
Visual Voice Mail is a voicemail system used by numerous mobile carriers that allow customers to view, listen to, and manage voicemails in any order.
Utilizing the method discovered by Talbot is a significant breach of privacy as it allows a remote person to potentially listen to someone’s private, and in many cases, sensitive messages.
To exploit CVE-2022-23835, the attacker must use an app with the READ_SMS permission required to eavesdrop on the VVM IMAP server credentials.
Also Read: 7 Key Principles of Privacy by Design that Businesses should adopt
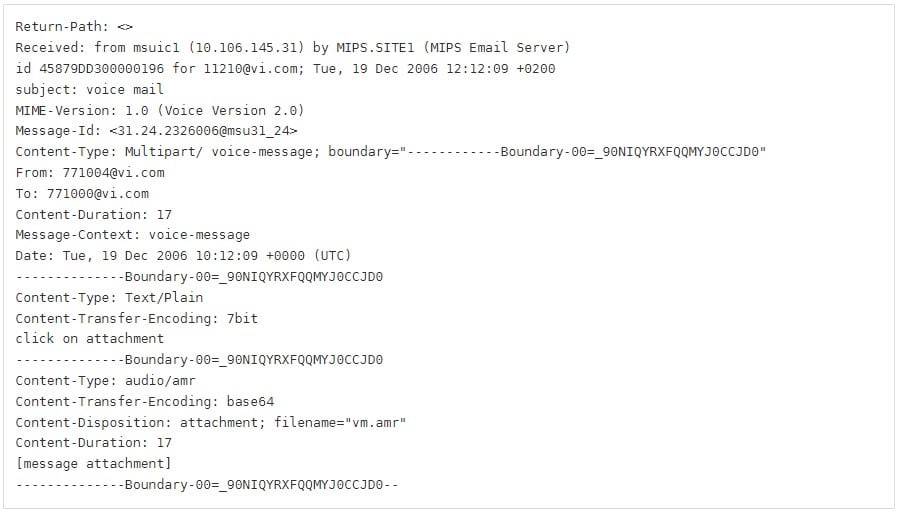
Because VVM IMAP credentials are sent in an unencrypted form via the SMS protocol, any malicious application with the permissions to read SMS content can snatch them.
These SMS messages are sent and received when registering on VVM, activating/deactivating, and logging in to the VVM client app. The users never see these SMS messages as they are handled by the VVM system in the background.
After the credential-stealing step is over, the attacker would no longer need access to the SIM card and SMS, and would be empowered to access the victim’s VVM independently and without leaving a trace.
Since Android leaves all voice messages on the IMAP server until the user deletes them in the client app, a malicious actor could access not only recent messages but an entire historical archive, depending on the victim’s data-wiping diligence.
The analyst tested the exploit against Android VVM applications, but the iPhone, which also supports VVM functions, wasn’t tested.
Also, when the victim switches to a new smartphone, the carrier doesn’t reset the VVM password even if the IMEI number associated with the particular SIM card has changed.
At this point, the only way for consumers to protect themselves against these attacks is to treat SMS permission granting requests with caution.
Remember, most instant messaging apps request this permission, so only install apps of this kind from trustworthy sources and publishers.
Additionally, change your VVM password periodically and delete voicemail messages you have accessed and no longer need.
Finally, accessing VVM services via a web portal is a lot safer than using client apps on your mobile device.