KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







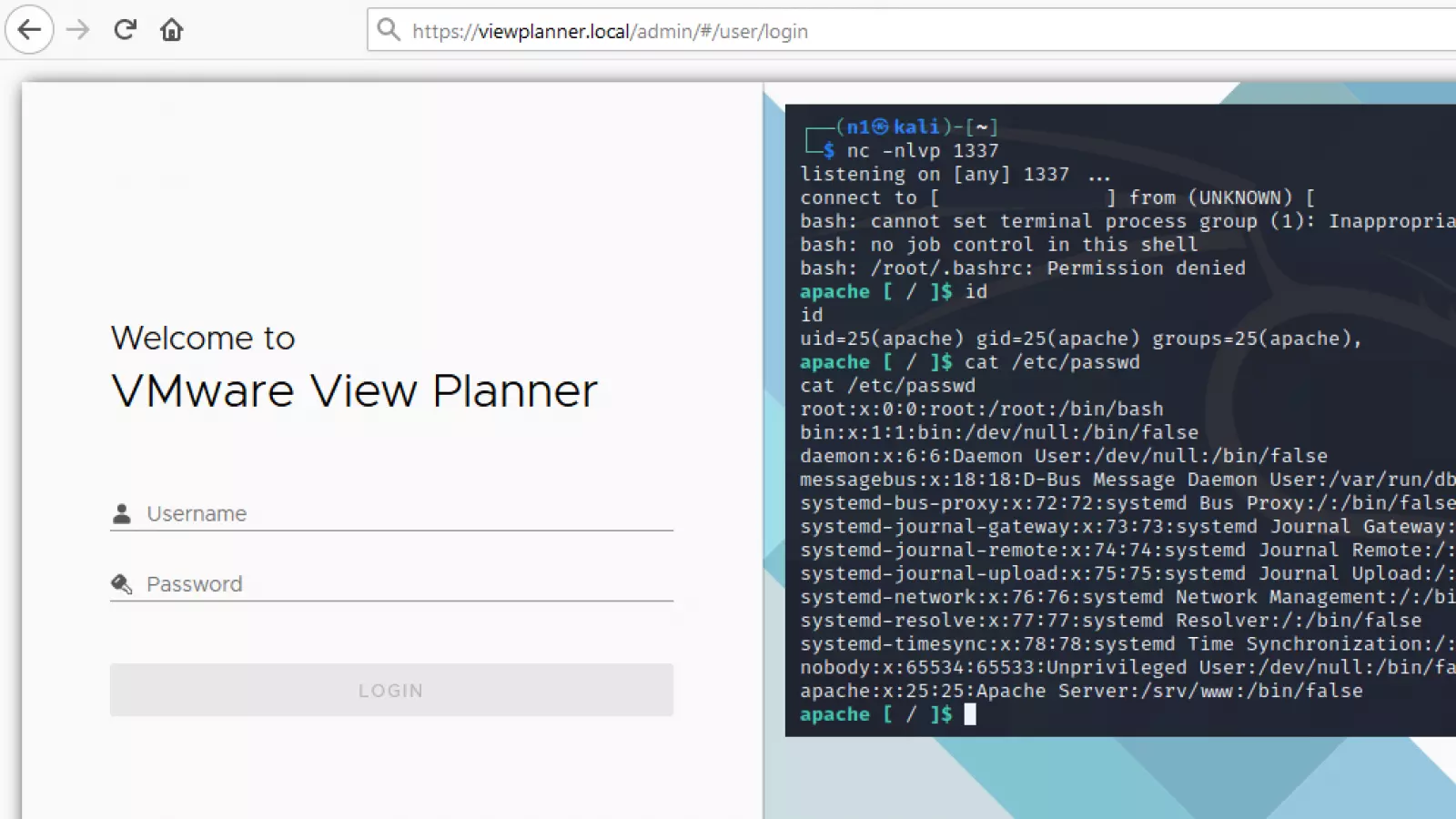
VMware has addressed a high severity unauthenticated RCE vulnerability in VMware View Planner, allowing attackers to abuse servers running unpatched software for remote code execution.
View Planner is a free tool for benchmarking desktop client and server-side performance in Virtual Desktop Infrastructure environments.
The vulnerability was discovered and reported to VMware by Positive Technologies web application security expert Mikhail Klyuchnikov.
According to VMware’s security advisory, the privately reported security flaw tracked as CVE-2021-21978 received a CVSS security rating of 8.6 out of 10.
CVE-2021-21978 can be exploited remotely by unauthenticated attackers in low complexity attacks that don’t require user interaction.
The flaw is caused by improper validation of file extensions due to improper input validation and lack of authorization bugs in the logupload web application.
Successfully exploiting VMware View Planner 4.x instances prior to 4.6 Security Patch 1 could allow remote attackers to upload arbitrary files via specially-crafted HTTP requests.
The attackers can then execute the uploaded files to run arbitrary malicious code on the compromised servers within the logupload container.
Also Read: Computer Misuse Act Singapore: The Truth And Its Offenses
Last month, VMware addressed another vulnerability (CVE-2021-21972) reported by Klyuchnikov, a critical RCE bug in the vCenter Server plugin affecting all default vCenter Client installations.
“The vSphere Client (HTML5) contains a remote code execution vulnerability in a vCenter Server plugin,” VMware said.
“A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server.”
Thousands of unpatched vCenter servers are reachable over the Internet, as shown by Shodan (over 6,700 exposed servers) and BinaryEdge (over 14,000).
Also Read: Personal Data Websites: 3 Things That You Must Be Informed
Attackers began mass scanning for vulnerable and Internet-exposed VMware vCenter servers within two days after security researchers published proof-of-concept (PoC) exploit code.