KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The US Department of Justice charged the admin of the WireX Android botnet for targeting an American multinational hotel chain in a distributed denial-of-service (DDoS) attack.
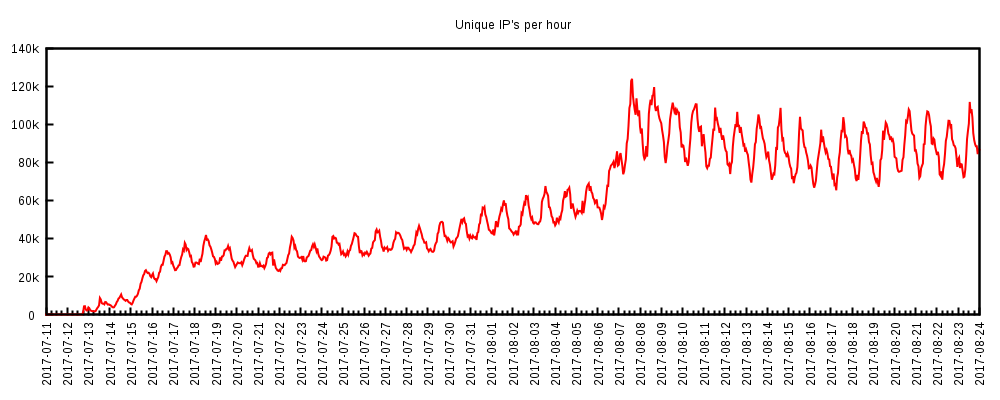
Izzet Mert Ozek, the defendant, used the botnet which consisted of tens of thousands of enslaved Android devices — more than 120,000 based on the unique IP addresses observed in some WireX attacks — to target the company’s online booking system website in August 2017.
“The hospitality company, which managed luxury hotels and resorts, was headquartered in Chicago and the servers for its website were located in northern Illinois,” a DOJ press release says.
“As part of the DDoS attack, the attacker directed large amounts of computer network traffic to Company A’s servers that hosted Company A’s website and online booking service, causing available resources to be consumed by the attack and resulting in no or few resources left to accommodate legitimate users,” according to court documents.
Ozek was charged on Wednesday with one count of intentionally causing damage to a protected computer punishable by up to ten years in prison.
Also Read: How does Do Not Call (DNC Registry) Affect Marketing 2020
The defendant has not yet been arrested and a warrant for his arrest is yet to be issued. He is believed to currently reside in Turkey.
While the DOJ didn’t reveal if Ozek was a customer or a WireX botnet admin, BleepingComputer was able to link him to the infrastructure used by the botnet.
His LinkedIn page shows him as the founder of a company named AxClick, a term used in multiple sub-domains of a single root domain (axclick[.]store) part of the WireX command and control (C2) infrastructure used to instruct the botnet to launch DDoS attacks against specific targets.
The WireX botnet surfaced in mid July 2017 and was built using hundreds of trojanized apps distributed via the Google Play Store and third-party app stores.
While the botnet’s attacks started in July (occasionally dropping ransom notes on some of its targets), it only landed on the radars of security researchers on August 17 when it was used in large-scale Layer 7 (application-level) DDoS attacks targeting multiple Content Delivery Networks (CDNs) and content providers, exhausting server memory resources and taking down online services.
Also Read: Free Guide For Appointing A Data Protection Officer (2020)
According to researchers who analyzed these mid-August incidents, the botnet launched DDoS attacks using bots from more than 100 countries, spread across more than 120,000 concurrent IP addresses.
Following these attacks, the botnet was quickly taken down by the end of August 2017, with the combined efforts of researchers from Akamai, Cloudflare, Flashpoint, RiskIQ, Google, Oracle Dyn, Team Cymru, some of its DDoS targets, other DDoS mitigation and intelligence firms, and the FBI.
“This trust group was formed immediately following the initial massive attacks that originated from Mirai,” Justin Paine, Head Of Trust & Safety at Cloudflare, told Bleeping Computer at the time.
“This group of researchers was also instrumental during the initial triage of WannaCry, NotPetya, and other events since Mirai.”