KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The recent cyberattack that forced the Dutch Research Council (NWO) to take its servers offline and suspend grant allocation processes was caused by the DoppelPaymer ransomware gang.
The hackers gained access to NWO’s network on February 8 and stole internal documents, threatening with leaking them unless the organization paid a ransom.
Since NWO does not cooperate with cybercriminals, DoppelPaymer published proof of the stolen internal data on their leak site. This tactic is typical to ransomware gangs and the purpose is to pressure victims into paying the ransom.
NWO is the main body that funds researchers at universities and institutes in the Netherlands, making annual investments of up to one billion euros.
The organization announced on February 14 that its network had been hacked, without providing details regarding the incident, only about the impact it has on its activity.
Also Read: Trusted Data Sharing Framework IMDA Announced In Singapore
On Wednesday, the DoppelPaymer ransomware gang leaked a dozen files stolen from NWO’s servers to show that they have a larger cache and are still open to negotiations.
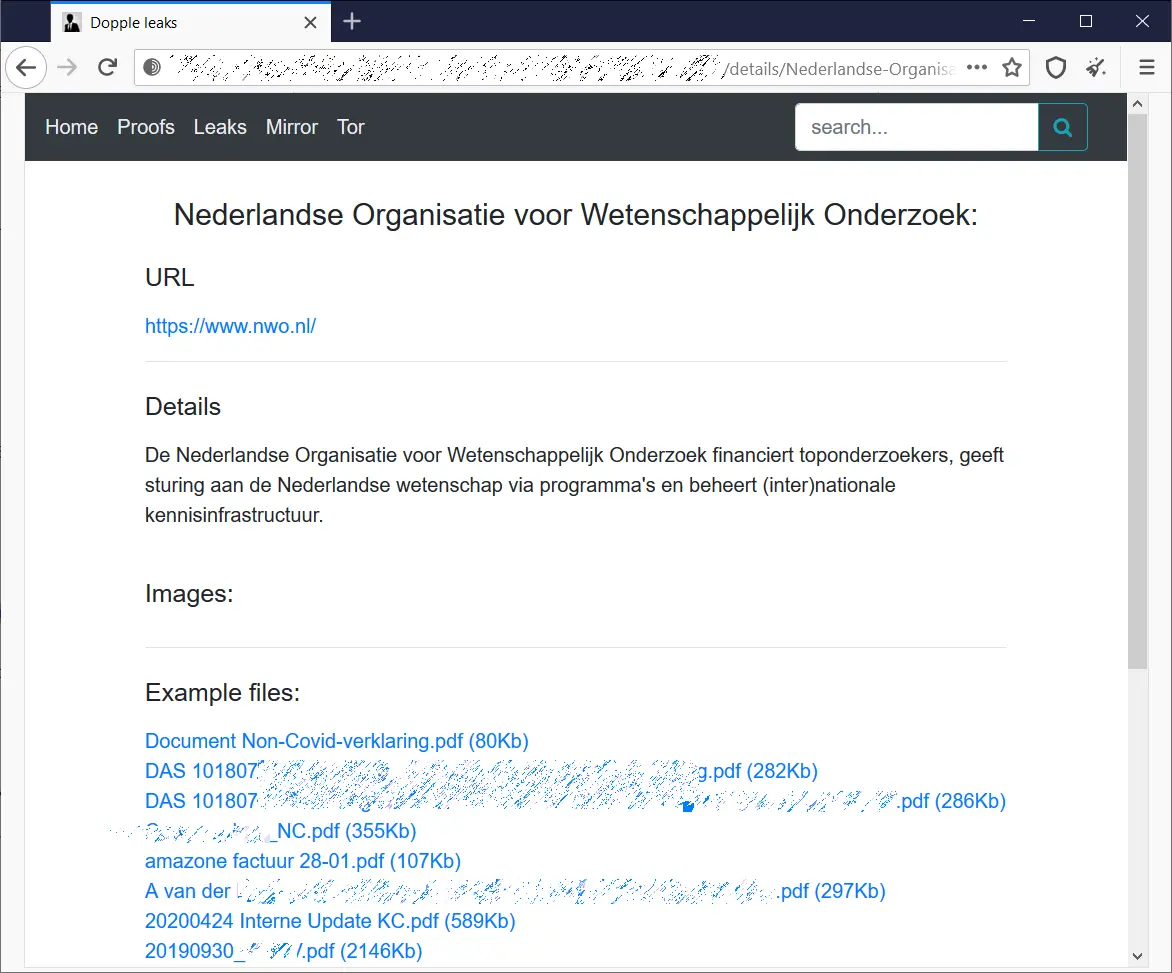
[Although the ransomware gang call themselves Dopple, the media refers to this actor as Doppel because of the extension “doppeled” they append to the encrypted files on a victim’s system]
In an update on the incident yesterday, the organization says that the hackers have internal NWO documents from the past years that include details about its employees. This does not change its decision not to pay the hackers.
NWO is currently working on restoring the network, which indicates that systems have been encrypted, typical to most ransomware actors. Operations are expected to resume in a few weeks.
A FAQ from the organization informs that the cyberattack impacted network disks with data processed by NWO, the NWO-I office, the National Governing Body for Practice-oriented Research SIA, and the Netherlands Initiative for Education Research (NRO).
Other organizations using the same network servers are the NRO Steering Body, SIA Steering Body, TKI-HTSM, TKI Chemie, European Polar Board, and the LNVH were affected.
The UK Research and Innovation (UKRI) agency, which has the same mission as NWO, has also been hit by a ransomware attack in January that encrypted data and affected some of its services.
Also Read: Data Protection Authority GDPR: Everything You Need To Know
While NWO still has some work to do to restore services and operations, UKRI announced that it restored services provided by its UK Research Office (UKRO) based in Brussels. Users will have to reset their passwords at login.