KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Researchers at Lucy Security recently discovered that a Russian hacker named m1x breached a Mexican government web portal and three days later once the government refused to pay a ransom, publicly-released some 14,000 Mexican taxpayer ID numbers.
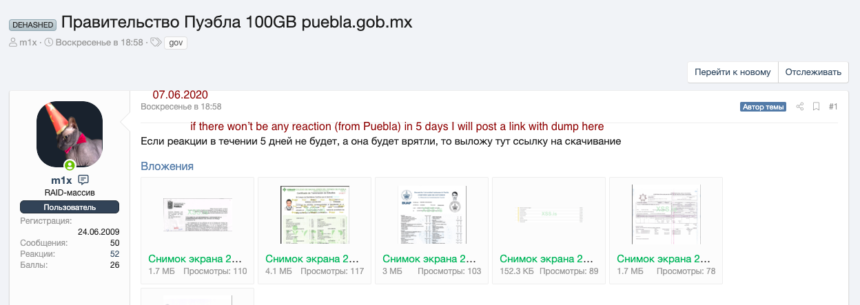
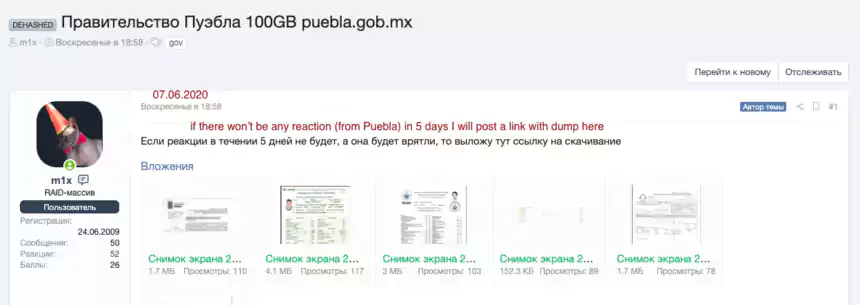
Colin Bastable, CEO of Lucy Security, said the researchers discovered the case on a hacking forum on the dark web Sunday, June 7. The hacker first announced that he was waiting for payment Sunday morning, but the Puebla staff did not know how to pay in bitcoin and the two parties could not reach an agreement fast enough. So on Wednesday of this week, m1x leaked 100 gigabytes of Mexican government data on a public cloud service.
“There appears to be a trove of credentials in the data,” Bastable said, who added that the taxpayer ID numbers included home addresses and phone numbers. The hacker also released an undetermined number of police records.
Also read: Cost of GDPR Compliance for Singapore Companies
Bastable said it’s interesting that m1x changed course in the middle of his plan. On Sunday, he gave the Mexican government five days to pay the ransom, but then released the data two days early.
“It’s not clear why he changed course, but’s what’s clear is that he rapidly accelerated the pressure on the victim, a tactic we’ve seen in several ransomware cases in the past several weeks,” Bastable said. “Typically, these type of hackers will do a public auction, but in this case the data was up there for anyone to grab.”
However, Bastable said the primary motivator appears to be money. He does not know for sure, but theorizes the m1x may release more data at a later point.
Alex Trafton, director at security company Pinkerton, said m1x has been around for several years and was definitely a Russian. He said he used the m1x moniker on one of the screen grabs (see photo) and according to a Russian translator Trafton spoke to, used the words Raid and then the Russian word for Massive next to the word Raid (Massive Raid).
“We never know for sure if they are connected to the government, but very often these players do hacking for the government and then the Russian government leaves them alone to do their criminal business,” Trafton said.
Bastable also confirmed that m1x has been around for several years. He said the hacker had been visiting the original Dark Web hacking site since June 24, 2009.
“All Mexicans should be concerned,” Bastable said. “Mexico is a dangerous place for police, journalists, politicians and most citizens – leaked data such as this exposes many people to physical danger as well as greater cyber risk.”
Also read: 7 Key Principles of Privacy by Design that Businesses should adopt